The bug get fixed, so I wanted to share the story...
Write-up Link:
7-th.github.io/posts/admin-pr…
English
Mostafa Alrefai
78 posts


@__the7th
All Thanks To My God - الحمد لله



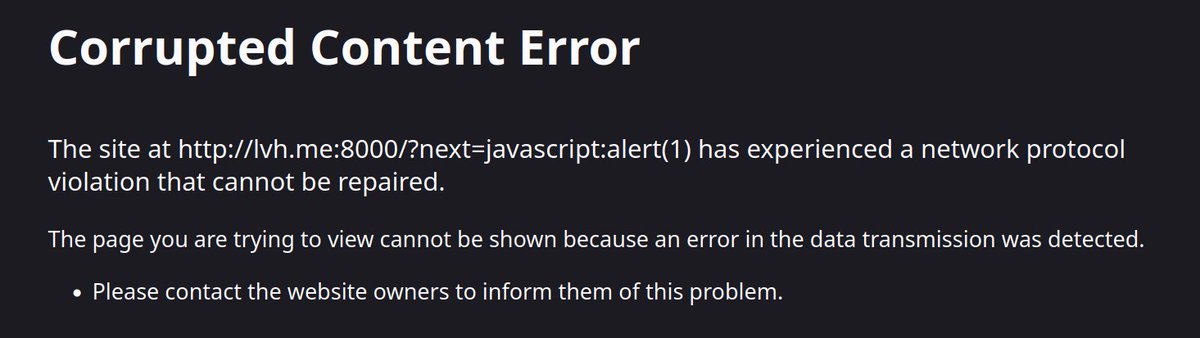
🧵Bug Bounty Diaries ( D4 ) How to escalate an "Open Redirect" from P5 to P3 or P1 Yesterday, I found an Open Redirect in a public VDP, and I wanted to teach you the exploitation process that you should take before reporting the bug as a P5 ... thread...