Stuart Ashenbrenner 🇺🇸 🇨🇦
7.2K posts


@stuartjash
Principal macOS Security Researcher at @HuntressLabs | Creator of @Crash_Security | Reviewer at @bestthrillbooks | @MillennialGirlDad on @SubstackInc | 🏀




Hello World!



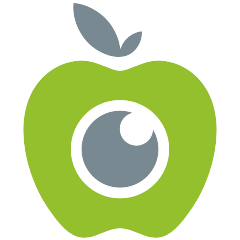
Is ESLogger or Mac Monitor your friend for dynamic malware analysis on macOS? Then i've got something that might come to use! An browser based ES/Mac Monitor log analyzer with a lot of neat features like story timelines, Sigma rule matching, an in-depth process tree analyzer and much more and the neat thing is, nothing is uploaded to any backend! I'm looking for feedback! Take a look at es.decompiler.dev #macos #malware #reverseengineering #re #ThreatHunting #dfir





Apple has released an update to XProtect for all macOS eclecticlight.co/2026/02/03/app… via @howardnoakley







🎉 A decade of Mac malware research 🎉 Just published our 10th annual “The Mac Malware of <year>” report ...2025 edition! For each new sample of 2025, covers: 🔎 IoCs 💉 Infection 💾 Persistence 📡 Capabilities ☣️ Samples for download Dive in 👇 objective-see.org/blog/blog_0x84…