Sabitlenmiş Tweet
regne
556 posts

regne
@_regne
I break some apps, do some reversing and learn some languages ctf player @fireshellst 🇧🇷🇪🇸🇺🇸🇯🇵
Katılım Ekim 2021
465 Takip Edilen227 Takipçiler
regne retweetledi

If you missed the talk at @1ns0mn1h4ck , our latest blog post is now available for you to explore.
In this post, researchers @Hacker_Chai and @SachaKozma detail their journey to a 1-click RCE exploit on the Samsung S25 phone.
Check it out here: bugscale.ch/blog/shoot-for…
English
regne retweetledi

Interested in exploiting browsers? Join me as I go over the free section of @ret2wargames "Fundamentals of Browser Exploitation" course. This is a course delivered by real #Pwn2Own winners! So, you're learning from the best! This first video is very beginner friendly so check it out even if you're just curios🧐.
Video link below:
youtu.be/5ArMYqwCmD4

YouTube
English
regne retweetledi

For anyone dealing with RASP protected apps, frida-strace is now your first step. Trace the syscalls, find what the app checks, hook those specific
functions, bypass. No more guessing. Frida 17.8.0+, kernel 6.1+ required.
#Frida #MobileSecurity #AppSec
Tur.js@Tur24Tur
Frida 17.8.0 dropped with frida-strace syscall tracing on Android & iOS, no jailbreak. Thank you @fridadotre #Frida #MobileSecurity #AppSec
English

@NetworkChuck Thank you so much, truly. This video was my pill to AI anxiety.
English

regne retweetledi
regne retweetledi

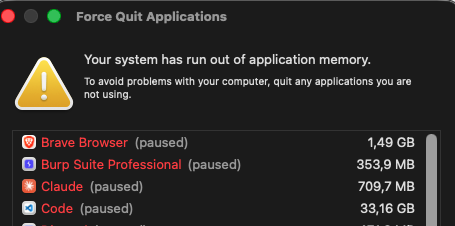
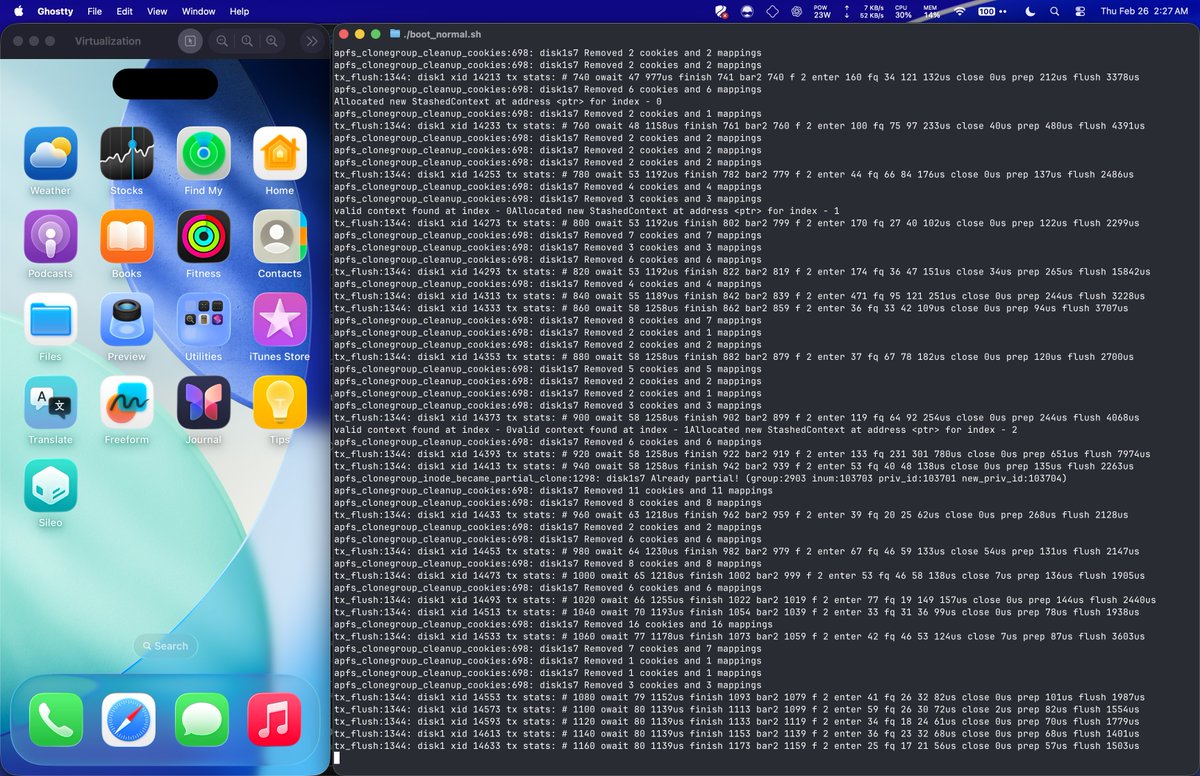
Finally got this virtual iPhone running iOS 26.1 up and running on macOS. It's jailbroken and going to help with security research a ton. Big thank you to @wh1te4ever for this.
This is not for the average user and is complicated to set up. Highly recommend Codex and/or Claude to assist.
For those interested, the project is here:
github.com/wh1te4ever/sup…
And the writeup is here:
github.com/wh1te4ever/sup…
English
regne retweetledi

🎄 XMAS GIVEAWAY ALERT! 🎅✨
🎉🔥 To celebrate the holiday season, we’re giving away TWO 12-month FREE vouchers for any of our premium courses:
▪️ Practical Mobile Application Exploitation
▪️ Offensive Mobile Reversing and Exploitation
▪️ Offensive iOS Internals
▪️ Offensive Android Internals
▪️ Practical AI Security: Attacks, Defenses, and Applications
How to participate:
➊ Like 👍 this post
➋ Comment which course you’d like to win and tag one friend. If you win, both of you get FREE access!
➌ Repost 🔁
➍ Follow @8kSec so we can DM you if you win
🎁 Two random winners will be selected and announced on December 24, 2025, on our socials. Both the winner and their tagged friend will receive FREE access to the selected course.
🔗 Learn more about our courses: academy.8ksec.io

English
regne retweetledi

"Only wimps use tape backup: real men just upload their important stuff on ftp, and let the rest of the world mirror it ;)" - Linus Torvalds, 1996 on LKML
"My data storage approach is: I upload it to the internet, and if it's worth saving, somebody else will save it for me." - Linus Torvalds, 2025 on Linus Tech Tips
English
regne retweetledi

Android Recon for Bug Bounty
Learn how to extract APKs, find hidden endpoints & secrets before exploitation using tools such as:
APKeep, APKTool, apk2url, jadx-gui, MobSF, MARA, Drozer
yeswehack.com/learn-bug-boun… via @yeswehack

English
regne retweetledi
regne retweetledi
regne retweetledi