Sabitlenmiş Tweet
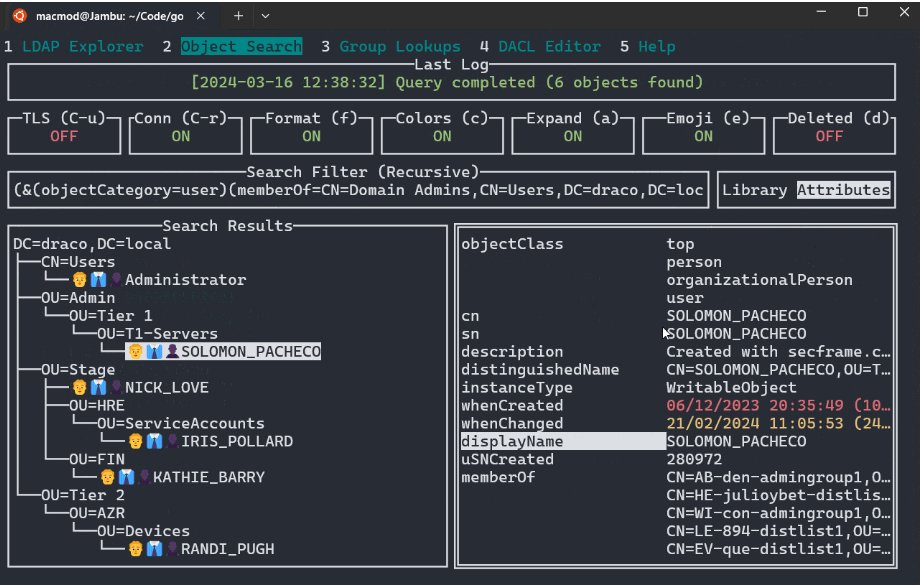
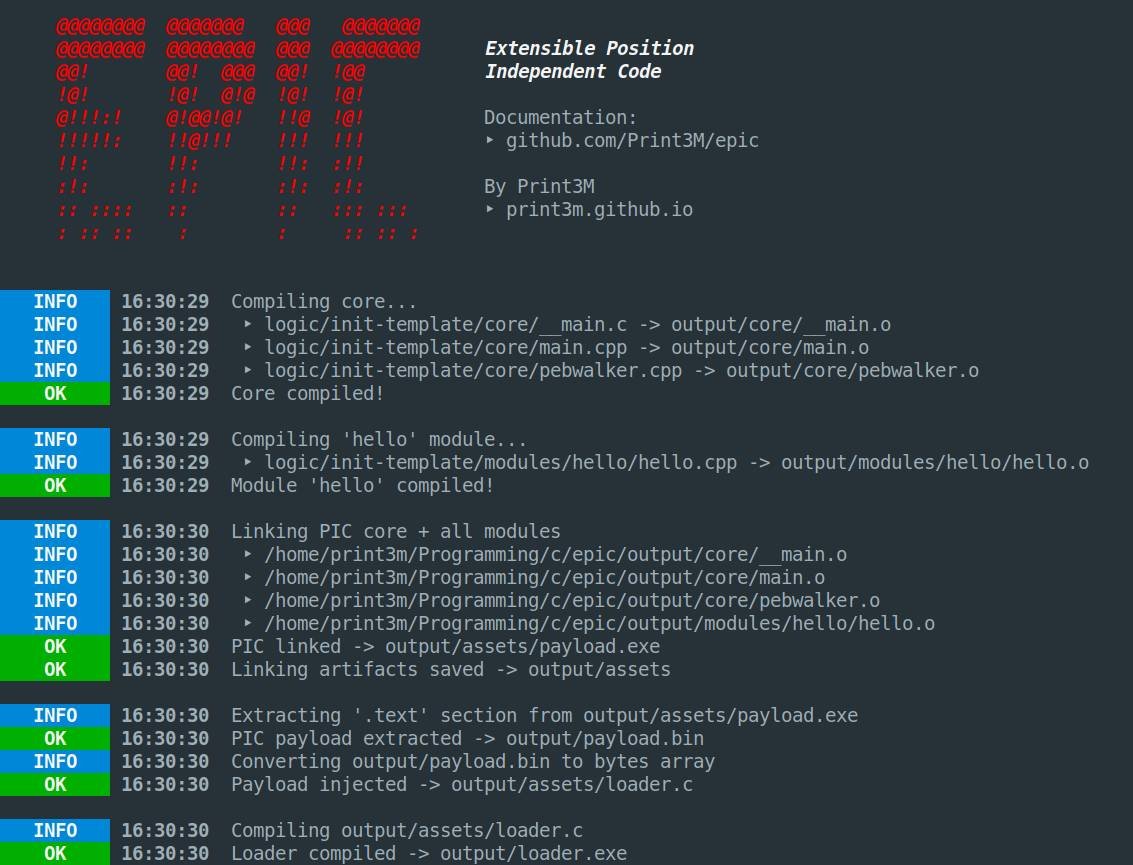
Releasing EPIC [Extensible Position Independent Code] – toolkit for C/C++ shellcode building 🔥
github.com/Print3M/epic
- Modularity (!)
- Dead-code & payload size optimization
- Global context
- Minimal PIC-friendly libc & win32 included
- More...
#redteam #malware #security

English