belabs_engineer
99 posts


belabs_engineer
@belabs_engineer
Interested in anything (de)obfuscation related.
Katılım Kasım 2024
69 Takip Edilen128 Takipçiler

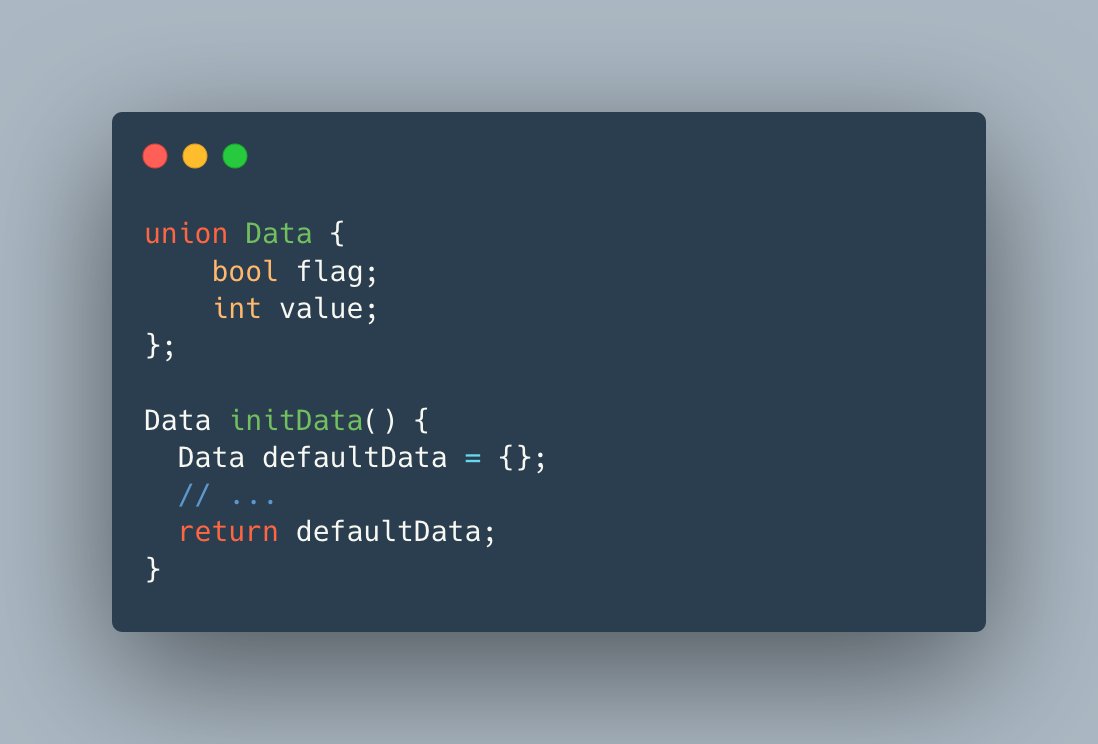
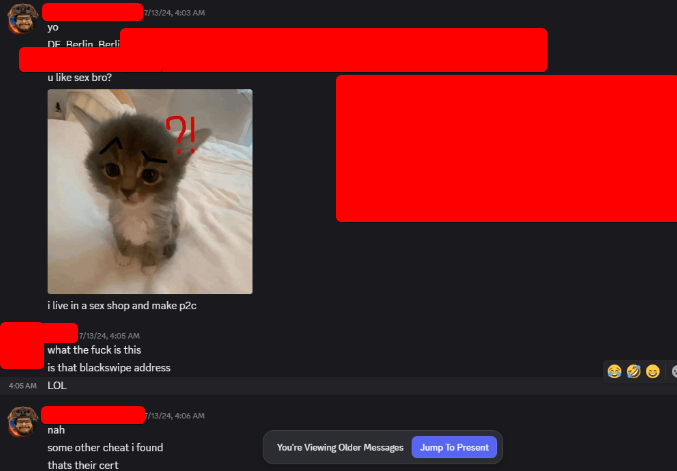
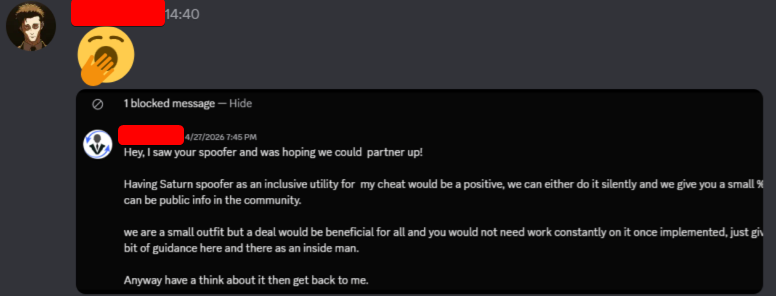
Serious allegations regarding Riot’s Vanguard anti-cheat system continue to grow, including:
• Claims that a Vanguard developer worked on a Vanguard spoofer called "Saturn" and other cheat related projects (a Javelin Anti-cheat Emulator)
• Claims that another Vanguard developer also defended the first Vanguard developer to EA and said he was not part of Riot
• Concerns that Vanguard may not fully delete user data after GDPR requests
• A leaked Vanguard panel screenshot appeared online
• Allegations that the first Vanguard developer mentioned also sent gifs in Discord servers containing signatures of a cheat blacklisted by Riot to ban legit people via Discord as Vanguard would think that the gif on your Discord is a cheat.
• Claims that a third Vanguard developer leaked Vanguard blacklisted signatures and private information
• Concerns that Vanguard can capture activity outside of League/Valorant when tabbing out often
This post reflects my personal opinion and interpretation. It does not claim any verified facts, and should not be taken as a statement of proven truth.


English
belabs_engineer retweetledi
belabs_engineer retweetledi

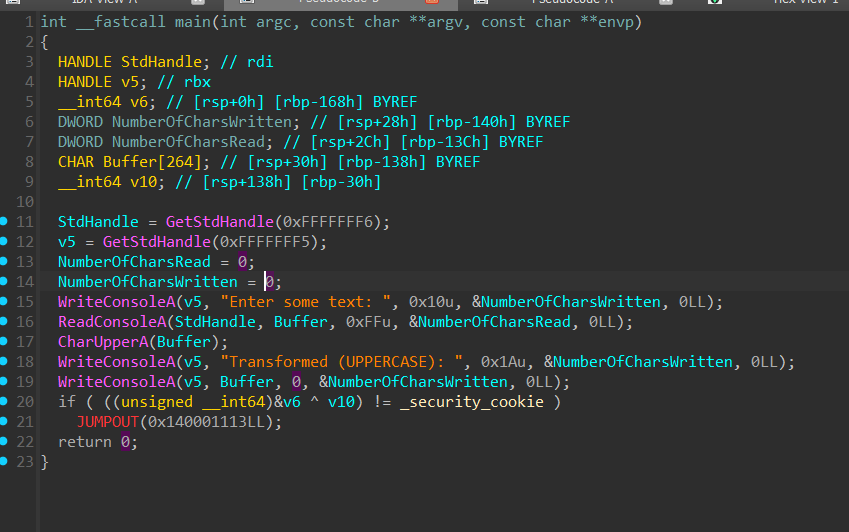
Static Devirtualization of Themida/CodeVirtualizer. The techniques in this article apply to pretty much every virtual machine obfuscator with minor modifications.
back.engineering/blog/09/05/202…
Original Program & Devirtualized Output
github.com/backengineerin…

English

China is shipping anti-cheat drivers that allow you to cheat, even in 2026. And they completely ignore any e-mail.
github.com/waryas/xign_po…
English

@nsg650 Maybe in 20 years, the inertia behind x86 is enormous
English
belabs_engineer retweetledi

I finally managed to finish the Hyper-V backend and execution times are crazy fast.
A sample application takes 1s to emulate using Hyper-V, while it takes more than 6s with Unicorn.
I feel like this opens up possibilities way beyond analysis 🥳
Maurice Heumann@momo5502
I'm adding Hyper-V (using the Windows Hypervisor Platform) as emulation backed to Sogen, my Windows userspace emulator: While providing slightly less analytical functionality, it should be a game changer in terms of speed 🥳 sogen.dev
English
belabs_engineer retweetledi

Wake up babe, new mba simplifier just dropped github.com/trailofbits/Co…
English
belabs_engineer retweetledi

We've uploaded our live stream from RE//verse 2026 where we sat down with @emesarecom from @vector35 to discuss WARP signatures used for symbol and type information recovery. Mason is a wealth of knowledge and it was a pleasure speaking with him at this amazing event!

English

@lauriewired @redsteakraw Glad you enjoyed the talk, was awesome seeing you there and talking to you about llvm based obfuscation afterwards.
English

well...not quite along those lines, but I really enjoyed this one talk that started out by reverse engineering VMProtect, pointing out the weaknesses, and then made their own cool obfuscator with some advanced techniques!
The talk isn’t quite up yet (too new), but they released the code here:
github.com/codedefender-i…
English

RE//Verse was genuinely one of the best technical conferences I’ve attended (and I’ve been to a lot!).
The caliber of the attendees was super high; one of the most technical audiences I’ve ever spoken to.
It was well organized, highly caring staff, not to mention the food was really good!
Giving the keynote was fun, and I really enjoyed all the other talks as well.


English
belabs_engineer retweetledi
belabs_engineer retweetledi
belabs_engineer retweetledi
belabs_engineer retweetledi

Reverse engineers, this is your conference. RE//verse kicks off in Orlando this March! Console and Xbox hacking, firmware targets, real world anti RE, and many talks you won't want to miss. Tickets are limited and selling fast, so grab yours before they are gone: shop.binary.ninja/collections/re…

English
belabs_engineer retweetledi

Laurie (@lauriewired) is keynoting RE//verse 2026 with Thinking Like a Compiler: Obfuscation from the Other Side! From LLVM passes baked into the build to custom VM bytecode that leaves decompilers guessing, this one goes straight for the toolchain. Get your ticket asap: shop.binary.ninja/collections/re…

English
belabs_engineer retweetledi

Catch this talk at RE//verse 2026. Xusheng Li walks through breaking encrypted USB drives with time travel debugging and shows how TTD in Binary Ninja makes it simple to spot “encrypted” drives with no real encryption, client side password handling and broken crypto. Tickets on sale here: shop.binary.ninja/collections/re…

English
belabs_engineer retweetledi

Carl Svensson (@zetatwo) is bringing Age of Empires II Definitive Edition to RE//verse 2026 as a playground for tooling. This talk walks through Binary Ninja automation to decrypt and deobfuscate game code and a BNIL query system for matching obfuscated instruction patterns. If you like game reversing you will want to see this talk: shop.binary.ninja/collections/re…

English
belabs_engineer retweetledi

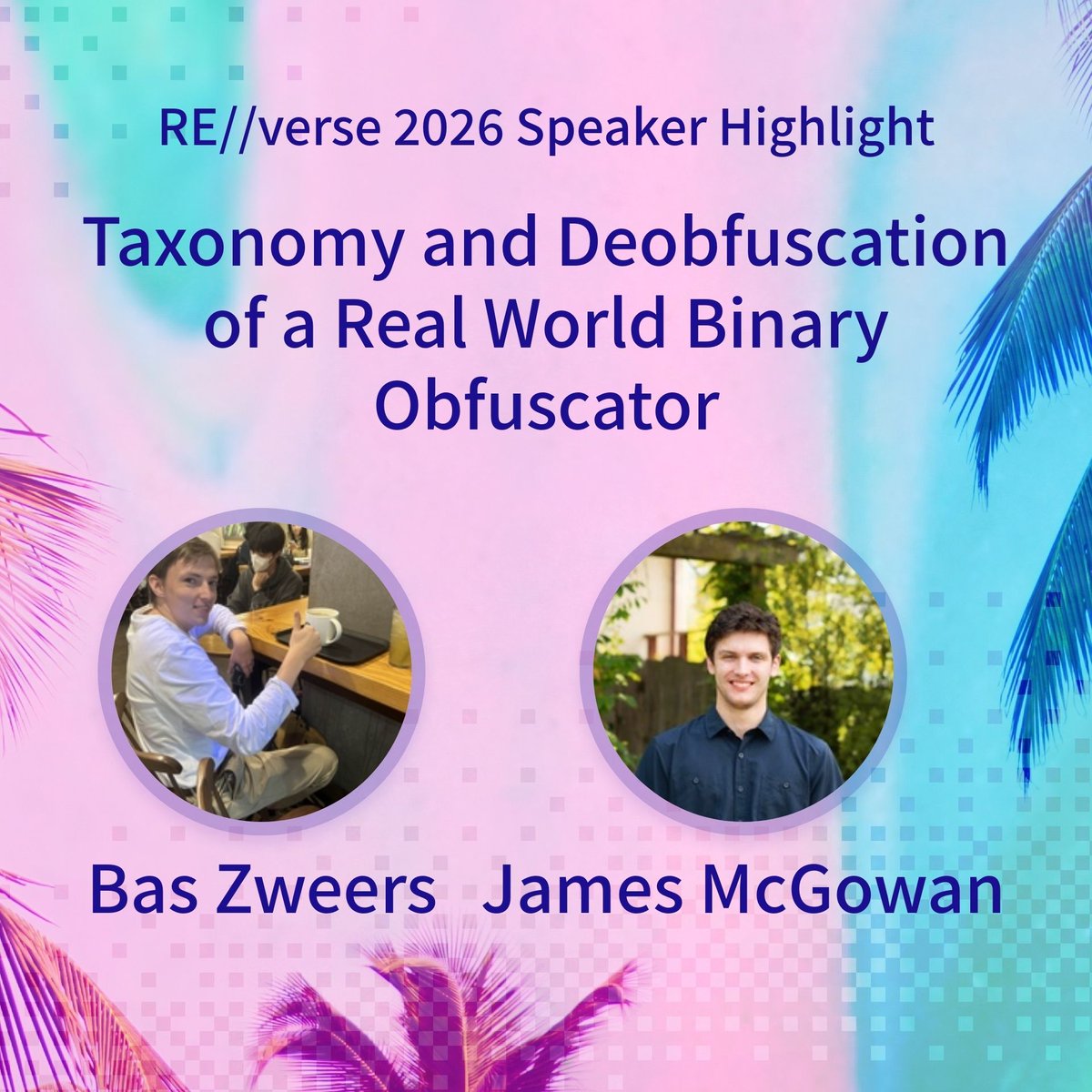
Bas Zweers (@belabs_engineer) and James McGowan (@backengineerlab) bring a look at a real world commercial binary obfuscator to RE//verse 2026. This talk walks through analysis and custom tooling to peel back obfuscation on Windows kernel mode anti cheat and ends with a full taxonomy of its tricks. Get your ticket: shop.binary.ninja/collections/re…
English