yamakadi
175 posts

@kyleavery @modexpblog The credits are definitely missing your name. I referenced a few articles for this example but your well-structured and clearly commented code is what made it work.
English

@modexpblog @_yamakadi Planned to publish a short post on this topic today… never hit send. 🙃 Maybe tomorrow
English
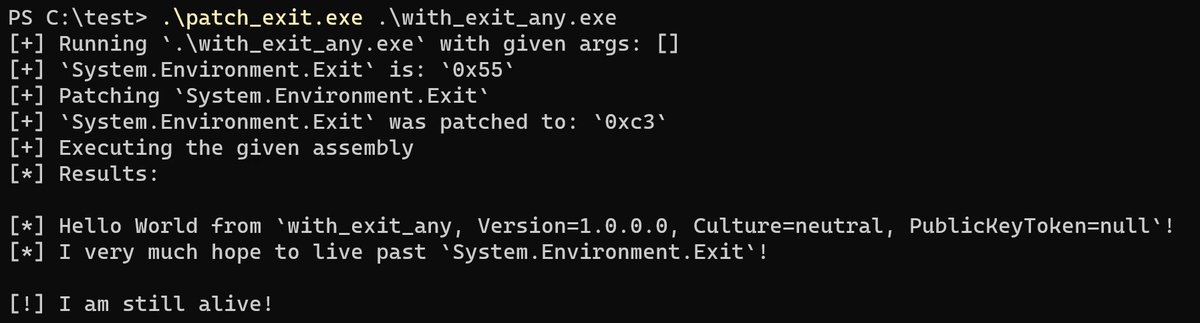
I have added an example for patching “Environment.Exit” to ClrOxide. You can keep the overeager to exit assemblies from crashing your processes now. 🤩 github.com/yamakadi/clrox…
English
@Octoberfest73 Price is usually less of an issue than the amount of red tape. Anything less than $500 with a one time payment option and a vague invoice is easier as a one off charge than a formal process that could take months and not even get approved. Consulting in Japan 😭
English
yamakadi retweetledi
@HakaiOffsec @memN0ps Great job! 😁 I couldn’t get around to releasing the fixed version of ldr and now I don’t have to 😆
English

After some hard work, coffee has been released! Our newest Rust COFF Loader!
If you want to check it out: github.com/hakaioffsec/co…
Don’t forget to check our blog post for more details:
labs.hakaioffsec.com/coffee-a-coff-…
English

@_xpn_ if I was crazy enough to get a Mac for dev work, what would you go for? Doesn't need to be portable so desktop or laptop is fine.
English

@_RastaMouse @_xpn_ How you gonna write your C# on a Mac 😤😤
English
@chvancooten @lpha3ch0 This is possible but awkward in rust and no guarantees for what kind of data you might end up with until trying to compile and making sense of the errors.
Nim really makes you appreciate it the farther you are away from it 😂
English

@lpha3ch0 People working in languages that don't have compile time preprocessing support reading this tweet be like
GIF
English

This is why I previously used slurp() in Nim to store a base64 encoded byte array of shellcode and then reverse the array, at compile time. Base64 is low entropy: const letters = slurp('sc.bin').encode().reverse()
Red Siege Information Security@RedSiege
"You’re encrypting your shellcode so you don’t get caught, and that might get you caught." In this new blog, Principal Consultant @hardwaterhacker discusses how the CrowdStrike Falcon detection works, and how to get around it. READ: redsiege.com/entropy #hacking #infosec
English
@Kharosx0 @Teach2Breach @memN0ps @trickster012 Sorry I missed this! Thank you for checking it out! I’ll go over it again! 😊
English
While I have some attention with ClrOxide, would anyone want to take a look at this and figure out why it’s not working? github.com/yamakadi/ldr @memN0ps @trickster012
English
yamakadi retweetledi
Credits to @C5pider and @R0h1rr1m by the way, and good folks at @TrustedSec. I’ve referenced their work thoroughly, and my code is basically CoffeeLdr in rust, but it’s missing something to actually make it work 😭
English
Huge shout-out to @chvancooten for forcing me to start on this by allowing risky commands into NimPlant, and @_Kudaes_ and @ropnop whose dinvoke_rs and go-clr libraries helped make things finally click!
English
Hi everyone! I've just released ClrOxide, a rust library that allows you to host the CLR and execute dotnet binaries. 😁 Your Rust C2's can finally do execute-assembly now 😜
github.com/yamakadi/clrox… / crates.io/crates/clroxide
English