Sabitlenmiş Tweet
Ace Pace
3.2K posts

Ace Pace
@ace__pace
There is never enough time, thank you for yours.
Available elsewhere as acepace Katılım Ekim 2014
1.6K Takip Edilen1K Takipçiler
Ace Pace retweetledi

security research now has this weird incentive where finding the bug is only half the game. the other half is packaging the story as "claude/codex found it" because that’s where all the attention is right now. model providers, with their big accounts and distribution, will push the story for you.
it looks win-win. weirdly, the human taste, target selection, hand holding, all get compressed into "the model found it".
frontier model companies happily push that narrative, while the researcher slowly gets devalued.
English
Ace Pace retweetledi

The magical news you’ve all been waiting for: registration for the new BlueHat IL 2026 date is officially open! Spots are limited - go grab yours!
Register here: aka.ms/BlueHatILRegis…
Full Agenda: microsoftrnd.co.il/bluehatil/conf…

English
Ace Pace retweetledi

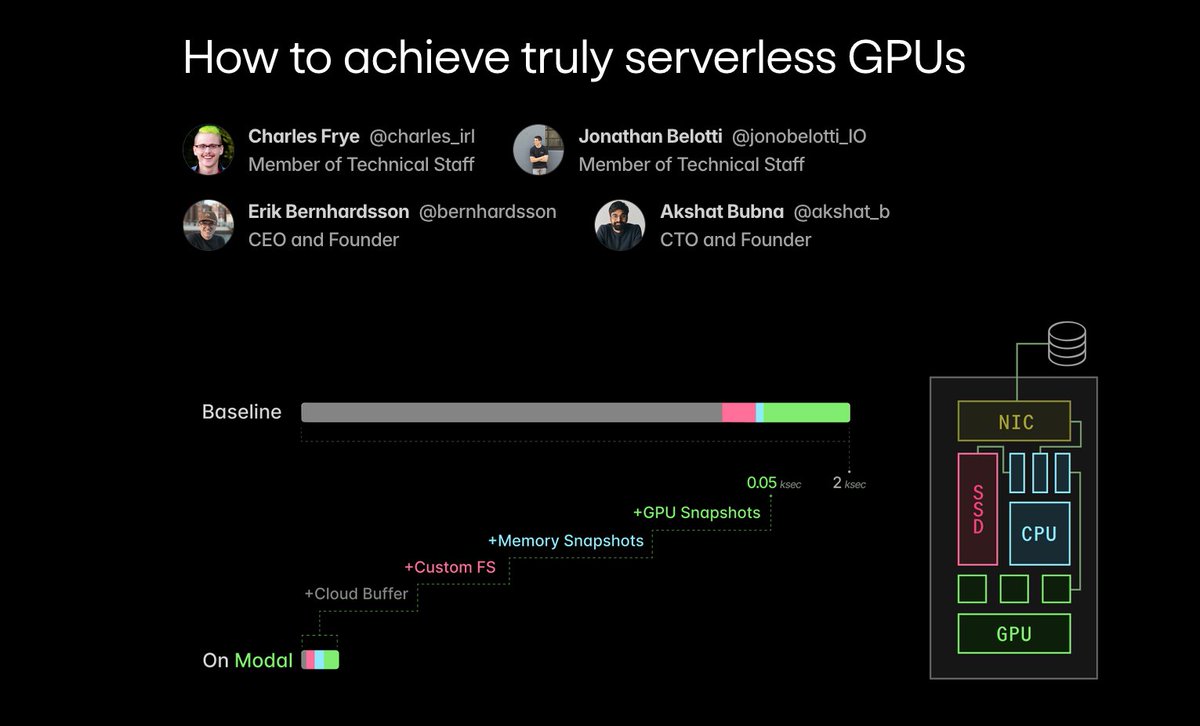
Inference isn't everything, but it does require a new stack -- not Kubernetes, not SLURM.
At @modal, we dove deep to build that stack.
In this blog post we explain how, from compute management & cloud-native cacheing to CRIU & GPU checkpointing.
modal.com/blog/truly-ser…
English
Ace Pace retweetledi

@NedWilliamson “We estimate that SockPuppet has an inherent exploit success rate limit of around 92%, meaning that even the best possible exploit that selects which exploit strategy to use based on the viable reallocation types would fail about 8% of the time.”
hey that’s still pretty good 🤣
English

apple.com/newsroom/2019/…
youtu.be/My_13FXODdU?t=…
security.apple.com/blog/what-if-w…
One last thing! I'm getting married soon so I'll be too busy to keep up. The AI boom is intense, but no matter how great the tension, cooperation and repair is always possible. Let's keep moving forward.

YouTube
English
Ace Pace retweetledi
Ace Pace retweetledi

The Unprompted.au CFP is officially OPEN! If you are doing cool stuff with AI in offense, defense, or working on core AI tech (from frontier models to open source LLMs), we'd love to hear from you! Submit here: unprompted.au
English
Ace Pace retweetledi

Things that have failed to bring the regime to negotiate in "good faith" (think tank slang for making concessions that aren't in its interests):
- Sanctioning Iran's Central Bank
- Kicking Iran off SWIFT
- Sanctioning Iran's oil
- Making Iran's currency collapse
- Assassinating everyone from Khamenei to Soleimani to Larijani
- Carpet bombing Tehran twice in 9 months
- Hitting every enrichment site
- Bombing the heart of Iran's industry
- Wiping out most of Iran's conventional navy
None of that worked. They haven't even agreed to the basic stuff like diluting the 60% enrichment stockpile which are the easier parts, let alone the trickier concessions.
Oh no but you don't understand the geniuses at the Brookings Institution have it figured out. The blockade will do what all those failed in.
Yea ok. The fruit flies infesting my home are more intelligent than these people ...
Robin Brooks@robin_j_brooks
The US blockade aims to do two things: (i) give Iran a taste of its own medicine for blockading the Strait of Hormuz; (ii) send Iran’s economy into a tailspin and thereby bring the regime to the negotiating table in good faith. It’s doing both. wsj.com/world/middle-e…
English

I'm not surprised that grsec wasn't impacted
grsecurity@grsecurity
If your kernel configuration is based on any major distro kernel configuration however and GRKERNSEC_MODHARDEN is enabled (as is done by default via auto-config) and algif_aead was not loaded as a module by a privileged user, exploitation is not possible by an unprivileged user:
English

@ace__pace Are still, but MODHARDEN should limit the impact in many common cases. Everyone involved handled this extremely poorly, it was most certainly not just a "you need fix X" issue, and the reporting company must know that, just like they should know...
English
Ace Pace retweetledi

@BarkolAmir מקלדת, משטח לשולחן, נעליים, ג'קט אמריקאי, משקפי שמש, מגבת חוף, סלסלת קניות שוק, מזוודה.
עברית

@lorgandon Never mind. The post also does the cardinal sin of asking the AI to explain its own decision, which is a recipe for making shit up
English

@lorgandon I don't understand what's new or surprising here. Most PaaS vendors such (Sturgons laws) and this entire post was written by an AI as rage bait where the author self-proclaims they were doing nothing according to best practice.
English


@daveaitel Yep using it. CSV export that suffers from inserting unescaped \n and breaks most parsers.
English

@ace__pace We're working on it. Stay posted. In the meantime, don't forget there's a comma separated value file download button.
English

@ryanaraine @craiu Again thank you for providing high-quality transcripts for free. This is really not trivial even with today's technology
English

NEW! On the Three Buddy Problem we talked to Mark Dowd on the state of offensive research, the economics of the exploit market, the AI hype machine, daily stresses of running an offensive shop, and state of zero-day market: youtu.be/NEDlOKHG8nY?si…

YouTube
English