مچهول الهويه
85 posts



Meanwhile, I’m working on a video about Google API and dependency confusion. You can check out the article from my third-last video. I just checked my drafts today and realized I forgot to share it earlier. Thought it might be helpful for you.
infosecwriteups.com/a-practical-wo…
English

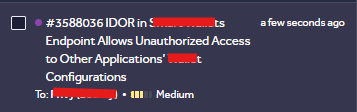
My Journey in Bug Bounty: Explaining IDOR Vulnerabilities to Delete User Private Lists
youtube.com/watch?v=XO7TU9…

YouTube
English

@thedawgyg Thank you for the advice. I would like to contribute or motivate people to search more.
English

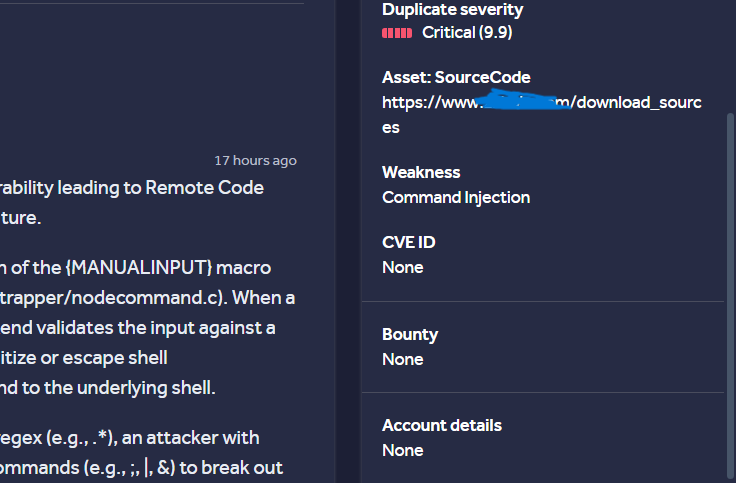
@adce626 congrats on the RCE, but becareful posting to much info in screen shots like this. the program is easily identified from the screenshot, and wouldnt want you to get in trouble with them or the platform. but as i said, great job getting the rce.
English


Just published a new article on bypassing live Cloudflare, ModSecurity, Fortinet, Akamai WAFs with SQL injection using Ghauri and Sqlmap. Don’t forget to read the Tips section for all methods and tricks that always worked for me.
infosecwriteups.com/mastering-sqlm…
English

@coffinxp7 Happy year to you, brother, I wish you dazzling success
English

I just published Guide 001 | Getting Started in Bug Bounty Hunting.. medium.com/p/guide-001-ge…

English

If you are selling your old phones, always format it first. After formatting, record a blank video until the storage is completely full. This process overwrites leftover data that may still exist on the device. Do this two or three times to make data recovery extremely difficult.
This step is important. If you sell a phone without properly wiping it, someone with technical skills may recover your personal information. In the worst case, your private photos, messages and other sensitive data could be exposed or misused by the wrong people.
GIF
English