Sabitlenmiş Tweet
gajurel
49 posts

gajurel
@ankurgajurel
life enthusiast, sideproject @ankurgajurel
Katılım Şubat 2015
1.1K Takip Edilen673 Takipçiler

सिरोहियाले कान्तिपुरले पछिल्लो समय गरिरहेको रिपोर्टिङ –विशेषगरी गृहमन्त्री सुधन गुरुङमाथि लेखिएका समाचार– मा आफ्नो गम्भीर असहमति रहेको राजीनामामा उल्लेख गरेका छन् ।
ekantipur.com/news/2026/04/2…
NE

ryuk-ai.xyz/?ref=tweet1
what it does:
- on first connection, agent grabs your schema + column annotation for context
- agent writes + validates + executes SQL
- streams back reasoning, query results and chart options
- the queries are saved as metrics
- you build dashboards as a collection of these metrics
- when asked specifically, agent generates a report and saves it. you either export a pdf or share a public link
2/3
English

@ankurgajurel @realpurus @tridevgurung I will. The new data source that I am working out, is directly from my TMS account. So, I can now buy and sell from my telegram account. It also makes it easier for trading agents to execute trades themselves.

English

@nlethetech @realpurus @tridevgurung i wanted ltp as well lol check this out. the data comes directly from nepalstockdotcom
github.com/lagani-org/nep…
English

It took me around eight months to build. Initially, it was a CLI-based system focused only on trading. Later, I used Claude to develop the UI.
For live NEPSE data, I currently use the Unofficial NEPSE API, but I am working on an alternative that directly interacts with my TMS. The system also scrapes around 30 news websites and more than 300 government websites. It parses key data from NRB and integrates everything into a unified platform.
I use the Claude API as my LLM, supported by about $300 in monthly credits provided by my university as part of a research grant. The system is designed to be highly efficient, with usage costs of around $0.30 per day.
English
gajurel retweetledi
पुँजी बजारमा भारी गिरावटः प्रवेशका लगानी अवसर, लगानीकर्तालाई त्रसित बनाएर किस्ता खोस्दै माफिया
#NEPSE 😁
Mukund❤️🙏@Mukunda_Chettri
हिजो सबैले भने : टर्नओभर हेर्नुस्! आज बजारले भन्यो : धन्यवाद, liquidity का लागि।अब पोर्टफोलियो पनि हेर्नुस्। #NEPSE
NE


gajurel retweetledi

The US government declassifying a PoC:
#include<▇▇▇▇.h>
int ▇▇▇_▇▇▇▇ {
▇▇▇▇▇▇▇
▇▇▇▇▇▇
▇▇▇▇▇ ▇▇▇
return ▇▇;
}
/*
* ▇▇▇▇▇ ▇▇▇
* ▇▇▇▇▇▇▇ ▇
*/
English
gajurel retweetledi

i've been hacked
and traced the malware's wallet to see how much money they actually made from this new exploit
(if you use Next.js/React, READ THIS!)
I woke up to a terrifying email from Hetzner: "Netscan Detected."
my server was blocked and a botnet was using my IP to attack others
i dug into the logs and what I found the anatomy of the attack:
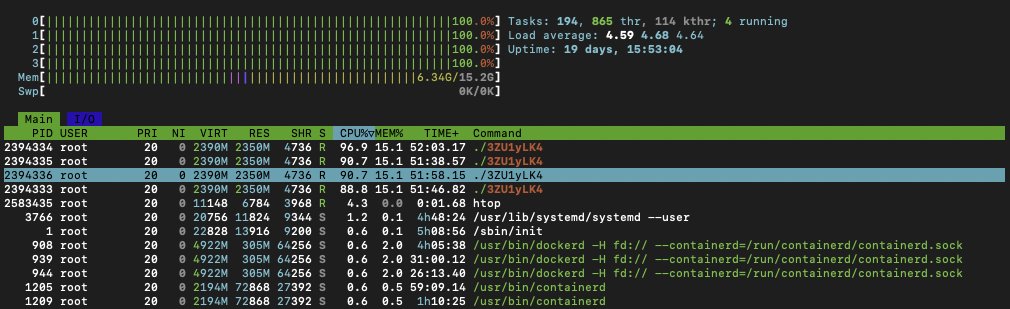
1) The Symptoms: I logged into htop and saw the mess:
- CPU usage: 361%
- A process named ./3ZU1yLK4 running wild
- Random connections to an IP in the Netherlands
my server wasn't serving my app anymore; it was mining crypto for someone else!
2) The Culprit: It wasn't a random SSH brute force. It was inside my Next.js container
the malware was sophisticated
it renamed itself nginxs and apaches to look like web servers
it even had a "killer" script that hunted down other hackers' miners to kill the competition
3) The "Root" Cause (literally): Probably the recent React/Next.js CVE-2025-66478 exploit was the entry point
(my project was running on "next": "15.5.4", behind cloudflare dns, but their recent fix didn't work apparently)
but the fatal error was mine: my Docker container was running as ROOT
Coolify deploys like this automatically when using Nixpacks, and I never changed it...
so because of USER root, the malware could install cron, systemd, and persistence scripts to survive reboots
meaning, it was able to infect my whole server, from a single Next.js docker!
4) The Forensics: I ran docker diff on the container - the hacker didn't just run a script, they installed a whole toolset..
- /tmp/apaches.sh (The installer)
- /var/spool/cron/root (The persistence)
- /c.json (The wallet config)
5) The Fix: I killed the container, scrubbed the host, and extracted the malware for analysis.
but the real fix is in the Dockerfile. if you are deploying Node/Next.js, DO NOT use the default (root), you must:
- RUN adduser --system nextjs
- USER nextjs
if you have Docker on ROOT and didn't update the exploited react version, you'll be hacked soon
check your containers NOW. Run: docker exec id
(or get the full list first: docker stats --no-stream)
If it says uid=0(root), you are one vulnerability away from being a crypto-miner host.
(it's easy to notice when hacked, it will be a command running on the top CPU%, using all your hardware resources)
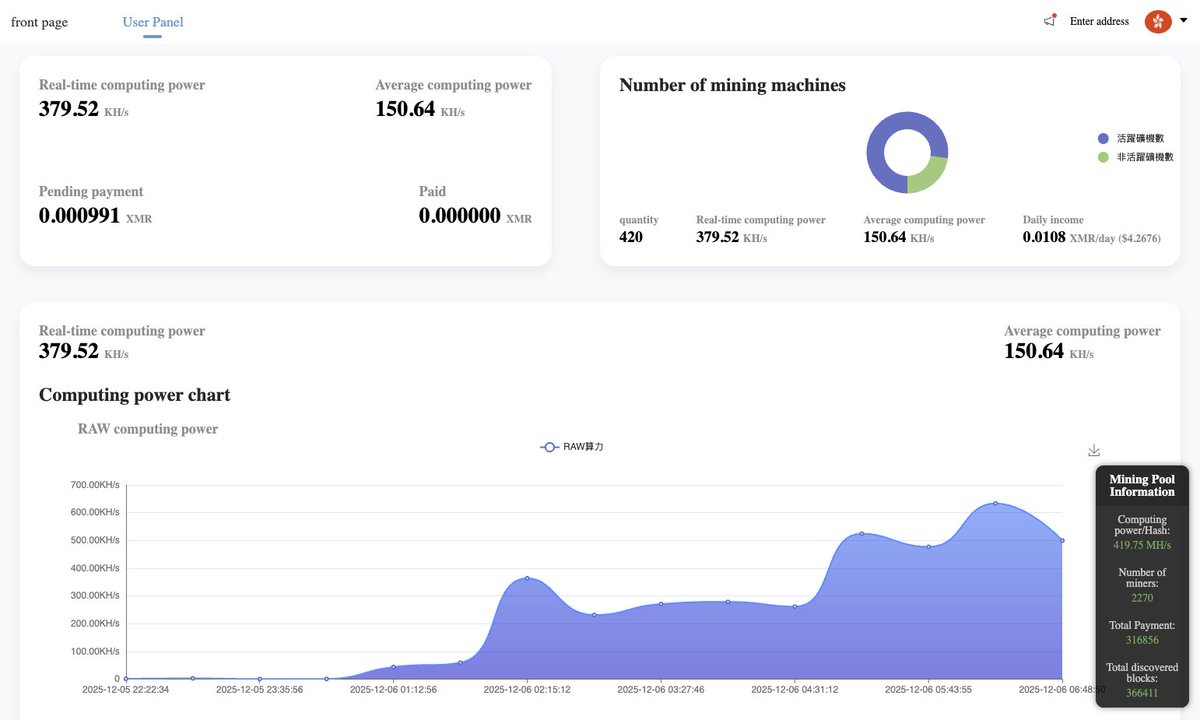
6) The Money: I dug deeper and recovered the config file (c.json)
- Wallet: A Monero (XMR) address: 831abXJn8dBdVe5nZ***
- Pool: auto.c3pool . org
and ofc i tracked the hacker’s wallet on the mining pool
7) The Scale: My server wasn't alone. It was just 1 of 415 active zombies in this botnet
they are burning the CPU of 400+ cloud servers... to earn...
guess how many millions?
$4.26/day
on the image attached you can see: "Total Paid: 0.00", meaning this campaign just started. I caught them on Day 1.
i also tracked back the server where they hosted the malware, and by inspecting the code, I found several comments in Chinese, so I guess that's their origin
im rebuilding from scratch on a fresh VPS. the lesson was expensive, but at least I caught it before the hosting nuked my account permanently...
PS: I have the IP for all the other machines mining with that malware, not sure how I can help them, but feel free to contact me if ur doing infosec
stay safe
English