
Edwin den Boer
20.2K posts


Edwin den Boer
@apertamono
Apertamono = Open Money



My son (age eleven) is definitely allowed to go places in the neighborhood but compared to how I remember myself does not have that much interest in doing so — “at home” has become way more entertaining than it used to be and most of his friends don’t live very close to us.



Niemand hat den "Kapitalismus" erfunden. Kapitalismus ist das, was freie Menschen von Natur aus tun - Waren und Dienstleistungen zu ihrem eigenen Vorteil tauschen.



Remember the security firm that Ubuntu hired to audit the (ill-advised, highly buggy) Rust-rewrites of all of the GNU Coreutils? Turns out that security firm is run by @gf_256, who: - Appears to be a man who thinks he's a woman ("trans"). - Uses an anime cartoon of a girl as his avatar. - Appears to have an OnlyFans page. I repeat: Ubuntu hired a "Trans" man, with an anime girl avatar and an OnlyFans page... to audit Rust code. It's hard to get more on-the-nose than that.





if you've got $100,000+ to lend out and want to earn ~6% fixed rate on your USDC please DM me



KYC bullshit would already be annoying if it worked as intended. Now try to get identified when have to submit a photo "without glare" of a glossy passport with reflective elements. I kept trying for an hour and failed to get approved for a Klarna debit card.


0/ Today, the Ethereum Foundation finalized the terms of a 10,000 ETH sale at an average price of $2,387 via OTC. For this sale, our OTC counterparts was @BitMNR.

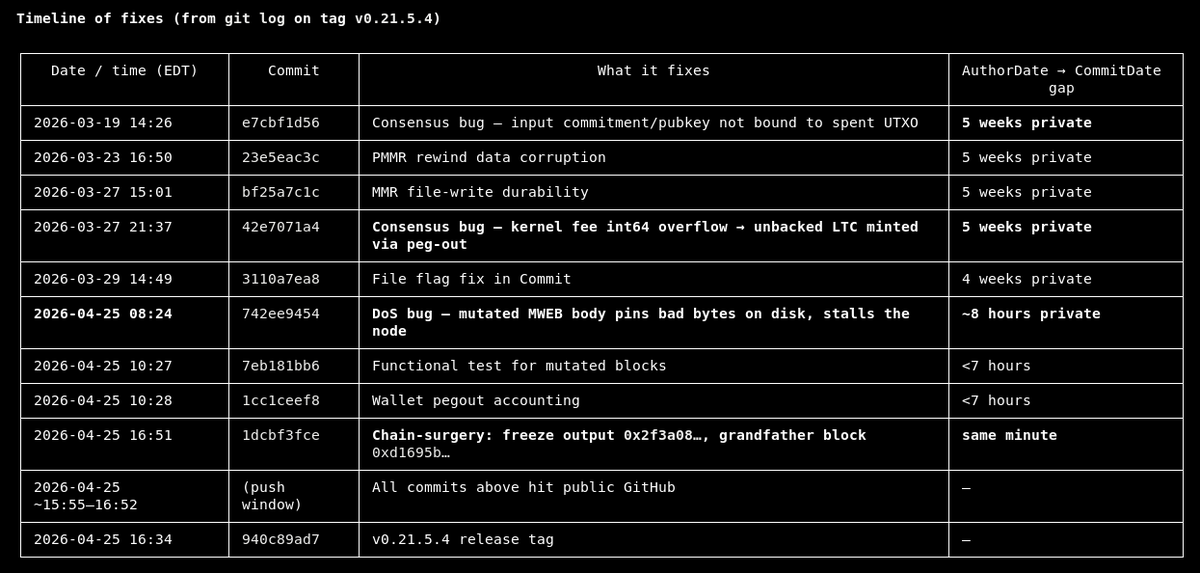
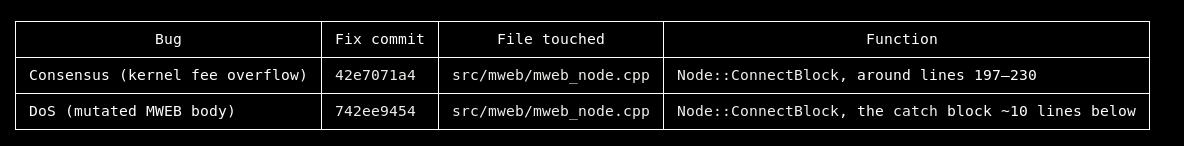
Zero-day or an inside job? 1. From our data the attacker was planning to swap LTC into ETH on this address: 0xfF18652A84aAd4f99F464f6B58cE7Ad929F6Fc10 which was funded 38h ago from @binance. Attacker knew about the bug for some time. 2. DoS attack was just putting nodes down to decrease the hashrate and there was indeed the bug in the MWEB txs. These two are different things. The MWEB bug is protocol bug. DoS is just a way to exploit it. 3. The fact that protocol automatically handled the reorg once DoS stopped (which is great) means that some portion of the hashrate was actually running an updated code. Thus, this bug was known and it's not a zero-day. So, somebody was able to DoS precisely upgraded hashrate up to the point that it was less upgraded hashrate than non-upgraded. Any chance the attacker knew who upgraded and who didn't, at least with high probability? If the bug was known and the miners were communicated with, then why RPC providers weren't? @Quicknode and others could have been omitting the blocks from non-upgraded miners. So these whole 13 invalid blocks would not be surfaced to anyone.



10) But wait! SP bondholders, who used to sit pari passu with deposits, now sit BELOW them. If you’re SP creditor of BNP, 1tn€ of liabilities just got ahead of you. The name "Senior Preferred" sounds a bit odd now: you just moved from the senior tranche to the mezz tranche.
