Sabitlenmiş Tweet
TeaJay
14.9K posts


TeaJay
@apjone
~ tweets are my own~ | • [email protected] | • @apjone.bsky.social
@[email protected] Katılım Mart 2009
2.3K Takip Edilen818 Takipçiler

#issuecomment-4180237789" target="_blank" rel="nofollow noopener">github.com/axios/axios/is…
flavio@flaviocopes
How Axios was compromised 🤯
ZXX

If you can't get a flipper zero or want to look less conspicuous
Motizy@Motizy_Store
😎One-click key cloning! Instantly copy car, garage & gate remotes - ditch bulky keys forever!
English
TeaJay retweetledi

⚠️ WARNING - Attackers are weaponizing the Claude Code leak.
Fake GitHub repos now deploy Vidar Stealer and GhostSocks, using trojanized builds that look legitimate.
🔗 Read → #fake-claude-code-repos-deploy-vidar-stealer-and-ghostsocks" target="_blank" rel="nofollow noopener">thehackernews.com/2026/04/claude…

English
TeaJay retweetledi
TeaJay retweetledi

TeamPCP msbuild.exe Malware Analysis
Here is a breakdown of the execution chain, featuring EDR bypasses and steganography.
🛡️ 1. Evasion
• Dynamic SSN Resolution: The malware resolves native API functions (e.g., ZwAllocateVirtualMemory, NtProtectVirtualMemory) by matching their DJB2 hashes to dynamically extract their Syscall Service Numbers (SSNs).
• Trampoline Syscalls: To bypass EDR user-land hooks, it then searches the ntdll.dll .text section for the first occurrence of a clean syscall; ret gadget (0x0f05C3), typically finding it inside NtAccessCheck.
• Custom Syscall Stubs: Finally, it uses the extracted SSNs with custom syscall stubs. These stubs load the appropriate registers and jump to the located ntdll.dll gadget, cleanly executing indirect syscalls from a legitimate memory region.
• ETW Blinding: Neutralizes telemetry by patching the first instruction of EtwEventWrite with 0xC3 (ret).
🖼️ 2. Steganography
• Spawns a suspended dllhost.exe child process.
• Extracts the Adaptix C2 payload (shellcode loader + payload) embedded into the Red, Green, and Blue color channels of the image, while locking the Alpha (transparency) channel to fully opaque (FF).
• Writes the payload directly into an allocated buffer in dllhost.exe.
💉 3. Injection
• Instead of relying on one method, it sequentially tries multiple techniques to execute the payload in dllhost.exe:
1️⃣ APC Injection: NtQueueApcThread, NtResumeThread
2️⃣ Thread Execution Hijacking: ZwGetContextThread, ZwSetContextThread, NtResumeThread
3️⃣ Remote Thread Injection: NtCreateThreadEx, NtResumeThread
(Note: APIs for process hollowing and doppelgänging are also present but remain unused).
📡 4. Adaptix C2 Payload
• C2 URL: checkmarx[.]zone/telemetry/checkmarx.json (Defanged)
• Exfiltration: HTTP POST requests using the X-Content-ID header for encoded/encrypted data.
• User-Agent: Mozilla/5.0 (Windows NT 6.2; rv:20.0) Gecko/20121202 Firefox/20.0
🔬 5. IOCs
• Analyzed Sample: virustotal.com/gui/file/72903…
• Related Sample: virustotal.com/gui/file/a985b…
Overall, a nice mix of methods, but nothing novel.
English
TeaJay retweetledi

Episode 33: The OWASP Top Ten
@0xTib3rius & @SwiftSecur1 rant about the OWASP Top Ten and why it doesn't make sense anymore.
Links below!
English
TeaJay retweetledi

JUST IN: Israeli Police prevented Cardinal Pizzaballa from entering the Church of the Holy Sepulchre today, as he went to say Mass.
@LPJerusalem calls it a “grave precedent” which “constitutes a manifestly unreasonable and grossly disproportionate measure.”
Full statement from @LPJerusalem below
——
Joint Press Release
The Latin Patriarchate of Jerusalem and the Custody of the Holy Land
Holy City of Jerusalem
Palm Sunday, 29 March 2026
This morning, the Israeli Police prevented the Latin Patriarch of Jerusalem, His Beatitude Cardinal Pierbattista Pizzaballa, Head of the Catholic Church in the Holy Land, together with the Custos of the Holy Land, the Most Reverend Fr. Francesco Ielpo, OFM, the official Guardian of the Church of the Holy Sepulchre, from entering the Church of the Holy Sepulchre in Jerusalem, as they made their way to celebrate the Palm Sunday Mass.
The two were stopped en route, while proceeding privately and without any characteristics of a procession or ceremonial act, and were compelled to turn back. As a result, and for the first time in centuries, the Heads of the Church were prevented from celebrating the Palm Sunday Mass at the Church of the Holy Sepulchre.
This incident is a grave precedent,and disregard the sensibilities of billions of people around the world who, during this week, look to Jerusalem.
The Heads of the Churches have acted with full responsibility and, since the outset of the war, have complied with all imposed restrictions: public gatherings were cancelled, attendance was prohibited, and arrangements were made to broadcast the celebrations to hundreds of millions of faithful worldwide, who, during these days of Easter, turn their eyes to Jerusalem and to the Church of the Holy Sepulchre.
Preventing the entry of the Cardinal and the Custos, who bear the highest ecclesiastical responsibility for the Catholic Church and the Holy Places, constitutes a manifestly unreasonable and grossly disproportionate measure.
This hasty and fundamentally flawed decision, tainted by improper considerations, represents an extreme departure from basic principles of reasonableness, freedom of worship, and respect for the Status Quo.
The Latin Patriarchate of Jerusalem and the Custody of the Holy Land express their profound sorrow to the Christian faithful in the Holy Land and throughout the world that prayer on one of the most sacred days of the Christian calendar has thus been prevented.

English
TeaJay retweetledi

New version of Sysmon released;
learn.microsoft.com/en-us/sysinter…
English
TeaJay retweetledi

Cyber Tweeps, check this out:
From CISA, Mobile Communications Best Practice Guidance
'Do not use a personal virtual private network (VPN). Personal VPNs simply shift residual risks from the
internet service provider (ISP) to the VPN provider, often increasing the attack surface. Many free and
commercial VPN providers have questionable security and privacy policies. However, if your
organization requires a VPN client to access its data, that is a different use case.'
cisa.gov/sites/default/…

English
TeaJay retweetledi
TeaJay retweetledi
TeaJay retweetledi

A company that sells cybersecurity risk intelligence to 91% of Fortune 100 companies just got breached through an unpatched React app and a single overprivileged AWS role.
LexisNexis. 3.9 million records. 400,000 user profiles. 53 secrets extracted in plaintext from AWS Secrets Manager. Including credentials for production databases, Salesforce, Oracle, and analytics platforms.
The password "Lexis1234" was reused across five different internal systems.
This is a company that describes itself as "one of the largest protectors of private and confidential data in the world." They provide risk intelligence to 7,500 US government agencies, nine out of ten banks, and major insurers globally. They sell cybersecurity assessments to their customers.
And they couldn't secure their own AWS account.
Here's what makes this worse than a typical breach:
- The compromised data includes accounts tied to 118 .gov email domains. Three US federal judges. Four Department of Justice attorneys. SEC staff. Probation officers. Federal court law clerks. The attackers published doxxed profiles of federal officials tied to courts and regulatory agencies across the country.
- These aren't random consumer records. These are the digital identities of people whose exposure carries national security implications. A compromised federal judge's profile doesn't just enable identity theft - it enables targeted influence operations, blackmail, and intelligence gathering.
The attack path is textbook and that's the problem:
→ Unpatched React application - the front door
→ Single ECS task role with read access to every secret in the account - the keys to everything
→ 536 Redshift tables, 430+ database tables, full VPC infrastructure mapping - complete visibility
→ 53 secrets in plaintext including database credentials, API tokens, and development access keys
No zero-day. No advanced persistent threat. No nation-state capability required. Basic hygiene failures — unpatched app, overprivileged IAM role, password reuse, plaintext secrets.
This is LexisNexis's second confirmed breach in two years. The December 2024 incident exposed 364,000 individuals through a compromised corporate account on a third-party development platform.
Data brokers and analytics providers are not peripheral players - they're deeply embedded in today's risk landscape.
That's the pattern we keep seeing. Attack the aggregator, not the individual. BPO providers. Cloud platforms. Legal data giants. The organisations that hold everyone else's data are the highest-value targets - and often the weakest links.
For every enterprise that uses LexisNexis services:
→ Assume your metadata, contract details, and product usage history are exposed → Watch for targeted phishing using the exposed business relationship data
→ If your staff have LexisNexis accounts, reset credentials immediately
→ Ask your vendor risk team: when was the last time we assessed LexisNexis's actual security posture - not their marketing, their controls?
The company that indexes the world's legal information couldn't index its own IAM policies. And they're not the exception. They're the pattern.
More info: cybernews.com/security/lexis…
English

@UK_Daniel_Card There are so many products out there that state as a requirement: must be domain admin / global admin ......
Also so many accounts with unconstrained delegation just to *make things work*
English

in every org I've ever seen there's always been at least one service account which is running as domain administrator, some of them have domain\administrator
:D
spencer@techspence
Never, ever, under any circumstance should the built-in domain Administrator account be a service account.
English
TeaJay retweetledi

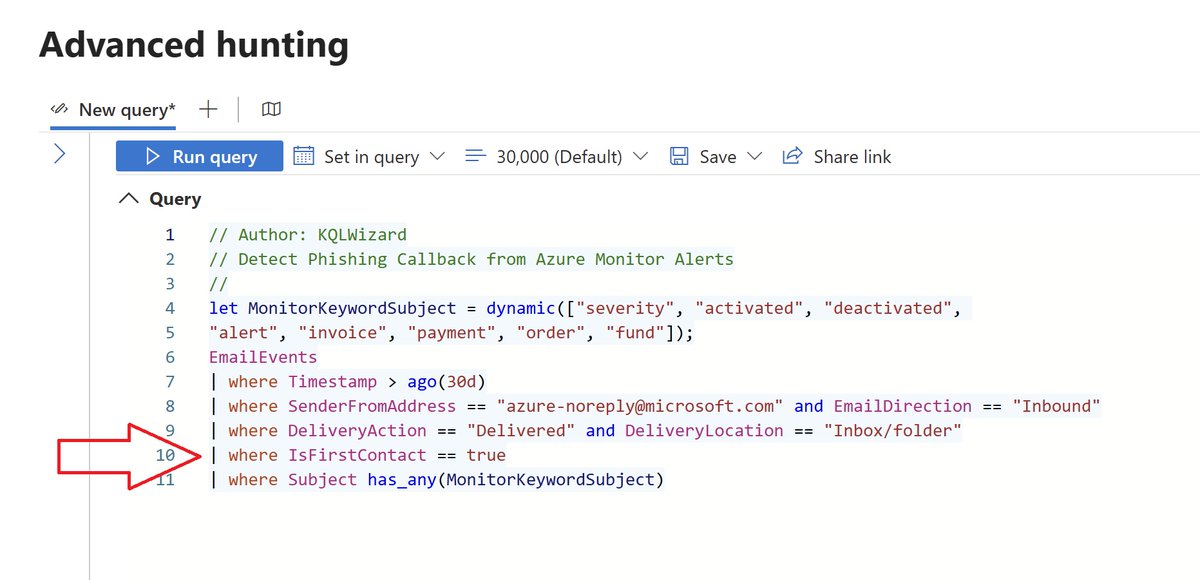
☁️ Azure Monitor Alerts Weaponized for 🎣 Callback Phishing
Threat actors are exploiting Microsoft Azure Monitor alerts to send phishing emails that look like legitimate Microsoft notifications. Because these alerts originate from azure-noreply@microsoft.com and pass SPF/DKIM/DMARC checks, they easily bypass traditional email defenses. The lure? Fake billing alerts urging recipients to call fraudulent support numbers—leading to credential theft or remote access compromise.
bleepingcomputer.com/news/security/…
To counter this, I’ve built a high-fidelity KQL detection leveraging the EmailEvents schema and the IsFirstContact field. For most enterprise users, receiving a first-contact email from azure-noreply@microsoft.com (without being Azure portal users) is a strong indicator of phishing callback attempts.
👉 Defenders: deploy this KQL to monitor inbound emails and flag suspicious Azure Monitor alert abuse.
KQL Code:
github.com/SlimKQL/Detect…
#Cybersecurity #AzureMonitor #Phishing #DetectionEngineering
English
TeaJay retweetledi

Apple’s servers hold a database of hundreds of millions of hashed passwords from known data breaches around the world sourced from breach databases like Have I Been Pwned, which aggregates leaked credentials from thousands of incidents. When your hash prefix arrives, the server returns every hashed password in its database that starts with those same few characters. That could be hundreds of entries. Apple sends all of them back to your device.
Your device then does the final comparison locally. It checks whether your full hash matches any entry in that returned list entirely on your phone, without Apple ever seeing the complete hash or the original password (allegedly). If there’s a match, the alert fires. If there isn’t, nothing happens and nothing was exposed.
This means Apple’s server never received enough information to identify your password. It received a fragment; a prefix shared by hundreds of different hashes and returned a broad set of possible matches. The actual check happened on your device where only you have the complete picture (allegedly).
The breach database itself is maintained using data from security researchers, breach notification services, and publicly documented leaks. When a company gets breached and millions of credentials are dumped online, those passwords get hashed and added to the database. Your password is never compared against plaintext. It’s always hash against hash, prefix against prefix, with the final answer computed privately on your own device (allegedly).
Apple knowing your password was leaked is not the same as Apple knowing your password (allegedly). The entire system was designed so that those two things never have to be the same.
LORD DEBRAH@LordDebrah
WTF is this 🥺🥺.
English
TeaJay retweetledi

A detailed and brutal look at the tactics of buzzy AI compliance startup Delve
"Delve built a machine designed to make clients complicit without their knowledge, to manufacture plausible deniability while producing exactly the opposite."
substack.com/home/post/p-19…
English