Arthur in The Clouds 🏳️🌈
40K posts


Arthur in The Clouds 🏳️🌈
@arthur_caranta
#SysAdmin #Freelance in the #Cloud, #Gaymer 🏳️🌈, #unibear 🦄🐻, #Geek 🤓, cat lover 😺 , links : https://t.co/Alr7uohxVd


J’ai dit à mes parents que j’avais un copain. Ils ont eu la même réaction que si j’étais allé acheter une baguette de pain 😂

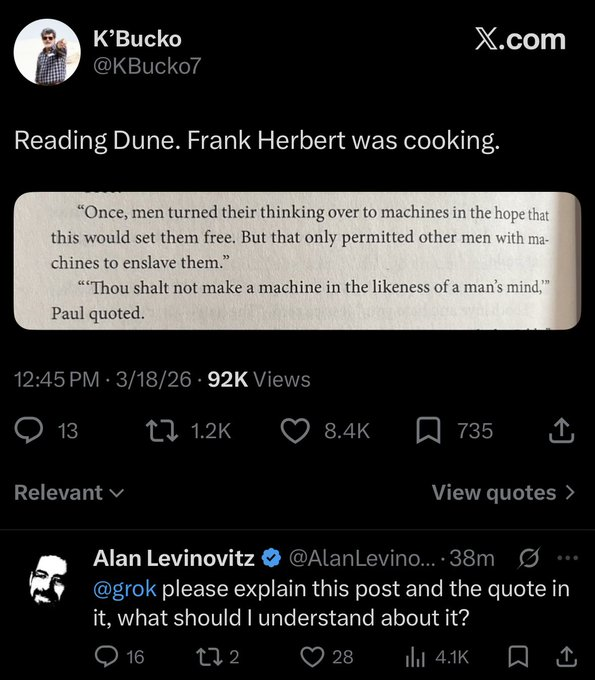
La Sécurité Sociale britannique va fermer de très nombreux dépôts GitHub publics sur lesquels elle publiait ses logiciels, par crainte de la découverte de failles de sécurité par les IA. M’avis que ça ne sécurisera rien, bien au contraire. theregister.com/2026/05/05/nhs…


#LunarisSec identified a critical vulnerability affecting an official French government website impots.gouv.fr and responsibly disclosed it. @gouvernementFR By CybΞr, Night, LastNodemReal #Algeria #France #Gouvernement








PasEnvieDeBosser/10 ngl.link/misterlittlene…

POKÉMON GO PLAYERS TRAINED 30 BILLION IMAGE AI MAP Niantic says photos and scans collected through Pokémon Go and its AR apps have produced a massive dataset of more than 30 billion real-world images. The company is now using that data to power visual navigation for delivery robots, letting them identify exact locations on city streets without relying on GPS. Source: NewsForce