Abbas Kudrati retweetledi

These movies are not answers.
They’re mirrors, maps, and warnings.
Follow @BoldExaltus for more on discipline, philosophy, psychology, and self-mastery.
English
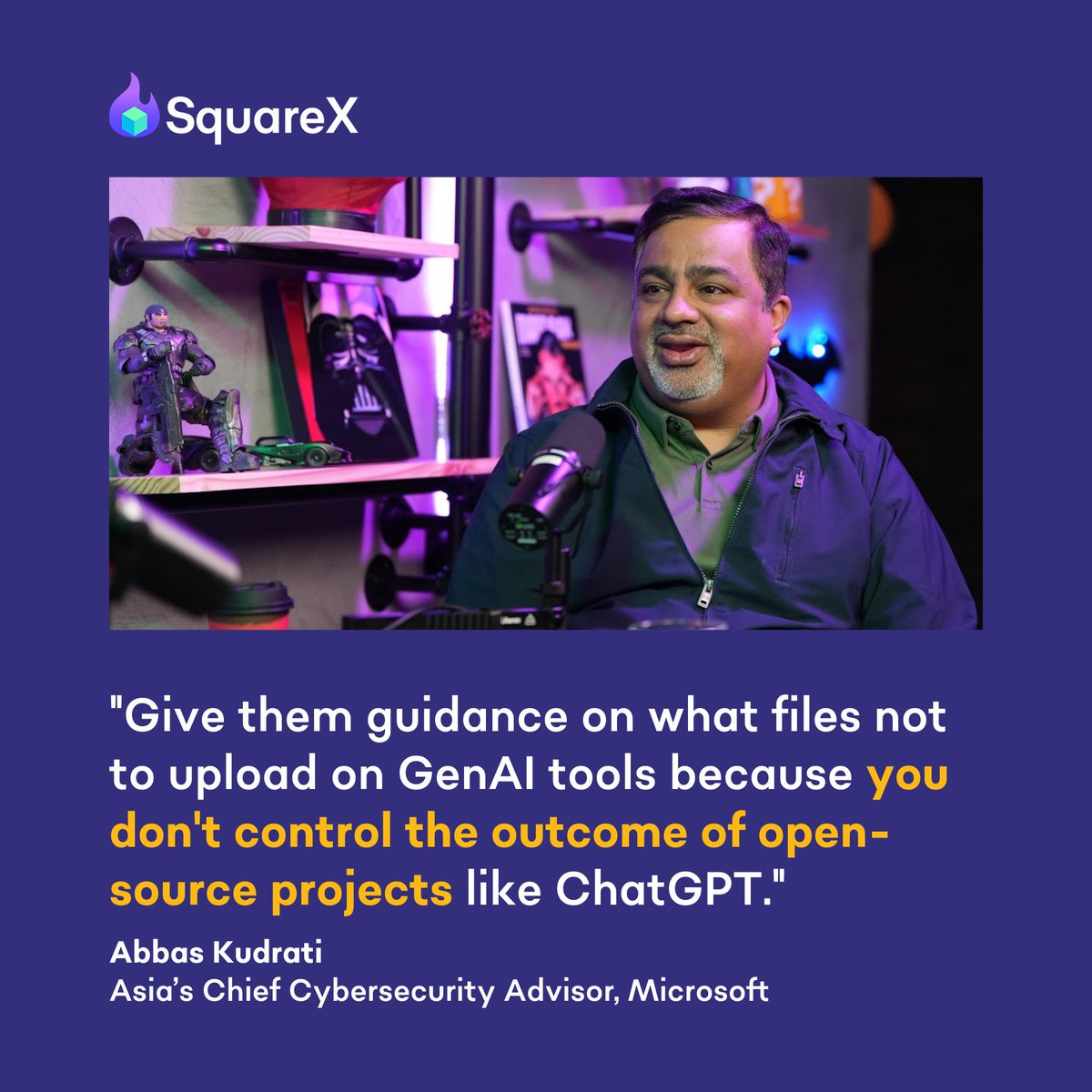
Abbas Kudrati
2.7K posts


@askudrati
Cyber exec @Silverfort | Ex-MSFT | Author of 5+ books | Prof @LaTrobe | Zero Trust believer | GRC whisperer | Identity is the new perimeter | Rider of a BMW R18







You’ve been lied to about weight loss. Cardio is a stupid way to lose fat. It barely burns any calories, makes you hungrier, and leads to overeating. Let me share a science-backed system to drop 20 pounds of fat before summer (without ever stepping on a treadmill): 🧵