Sabitlenmiş Tweet

Looking for a recon methodology on a web app ??
Look no further...
🔗👉🏼admapp.com/wapps/1-recon-…
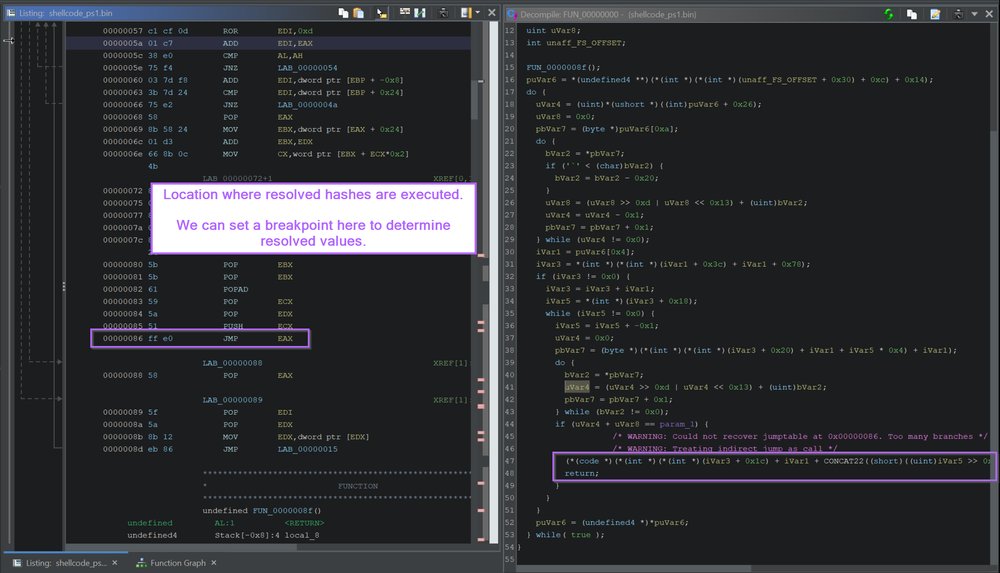
This is a graphical cheat-sheet that displays ways to find a variety of potential attack paths.
Covers the following & more:
✔️ Tech Stack
✔️ Asset Discovery
✔️App Functionality

English