Sabitlenmiş Tweet

"To truly understand an adversary, you must rise to — or beyond — their depth.Because only depth reveals intent."
#CyberSecurity #MalwareAnalysis #APT #NationalLevelAPT #ThreatIntel #ReverseEngineering
English
clibm079
504 posts
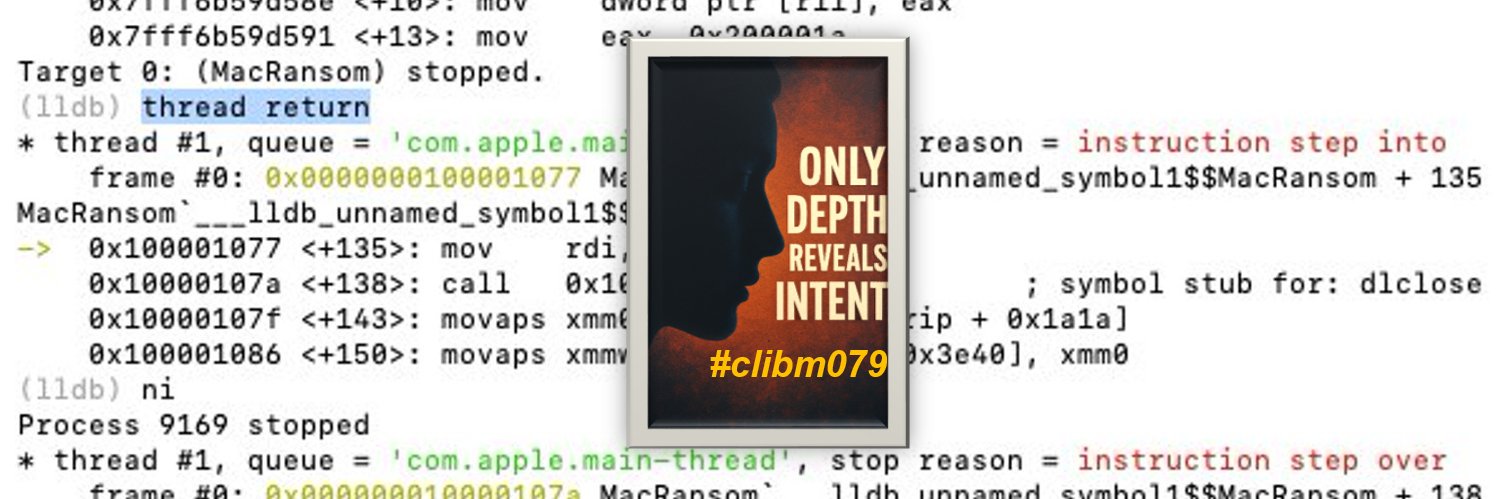

@clibm079
Independent Malware Analyst & Researcher,Notes (Philosophy & Poetry) — The Path of Clarity & Poems of Malware Analysis. Blog: https://t.co/DJ3Wxn2OWS