baris
470 posts

Sabitlenmiş Tweet


mavi powerade damacana şeklinde satılıyor mu 500ml yetmiyor @Powerade_TR
Türkçe


Siz webscraping icin browser engine mi kullanıyonuz
Şerafettin Sarışen@ssarisen
web scraping ile uğraşıyorsanız obscuraya bakın. rustta yazılmış headless browser. chrome alternatifi. 30mb ram tek binary. stealth tarafında her sessionda tarayıcı parmak izini sıfırdan üretiyor bot tespitini zorlaştırıyor ve bilinen analisty,hotjar vs gibi 3520 tracker domaini başta bloklu geliyor. puppeteer/playwright desteği var ve çok minimal konfigrasyonda çalışıyor.eğer web scrape işleriniz için bir çözüm arıyorsanız muhakkak deneyin derim.
Türkçe

Bir domainin başına herhangi bir kelime ekleyince başka bir web sitesine gitmiş oluyorsun. Şunu kavrayamayan insanların bu zeka seviyesiyle nasıl hayatta kaldığına bazen şaşırıyorum.
BGY@bgyetherr
İnterneti keşfediyoruz
Türkçe

do you use screen time on apple devices, and would you like to see @heliumbrowser support it?
English
baris retweetledi

@fatihguzeldev dunyanin en dogru yorumu. hicbir dogru duzgun packagesi yok. hicbir telefonla dogru duzgun uyumu yok. responsiveness hak getire. nefret otesi bi teknoloji
Türkçe

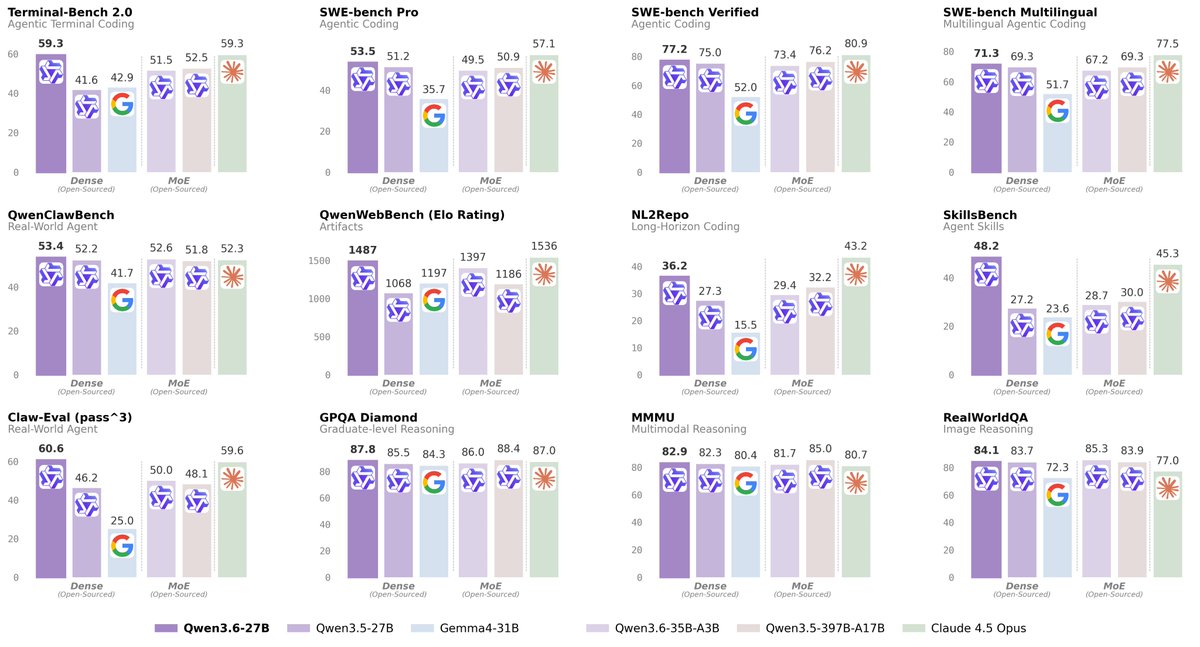
@talha_dilber @mstrYoda_ benchmaxxing chinese model ayriyeten 4.5 =/= 4.7 yine de qwen babayı severiz
Türkçe

@mstrYoda_ Qwen 3.6-27B neredeyse. Opus 4.5 seviyelerine geldi. Biraz baktım 5090 ile Q6 (en kayıpsız optimum quantization) da 50 token/s alan varmış. Zaten şuanda bir çok servis ortalamada 50 token/s veriyor. Ben 35B yi Q3 ile kullanıyorum bayağı iyi çalışıyor. Claude code rahat çalışıyor
Türkçe

Bunu ben de sürekli soruyorum, sizce Opus 4.6 muadili bir modeli lokalde çalıştırmamız için ne kadarlık bir zaman var?
Yousr@rsuyoy
What's a reasonable timeline for a GPT 5.4/Opus 4.6 level LLM that runs locally on a good Macbook 10 years? much less? much more?
Türkçe
baris retweetledi