Bret Comnes
12.4K posts


Bret Comnes
@bcomnes
👨💻 @socketsecurity⚡️ @breadcrum_ 🐘 https://t.co/gTTtJXMCml

I must admit that nothing about computers, since I'm in love with the field, was so uninteresting as the Javascript different fashions, waves, frameworks, rewrites, hypes. And I'm one that loves almost every shit programming related.






"Hardening TanStack After the npm Compromise", a followup to yesterday's post-mortem. tanstack.com/blog/incident-…

🚨 UPDATE: Mini Shai-Hulud has crossed from @npmjs into @pypi and is still spreading. Newly confirmed compromised artifacts: @opensearch-project/opensearch: 3.5.3, 3.6.2, 3.7.0, 3.8.0 (1.3M weekly downloads) mistralai: 2.4.6 on PyPI guardrails-ai: 0.10.1 on PyPI additional @squawk/* packages on npm guardrails-ai 0.10.1 executes malicious code on import. On Linux, it downloads git-tanstack[.]com/transformers.pyz, writes it to /tmp/transformers.pyz, and runs it with python3 without integrity verification. The git-tanstack.com domain displayed a message signed “With Love TeamPCP,” along with: “We've been online over 2 hours now stealing creds Regardless I just came to say hello :^)” The page also linked to a YouTube video and you can probably guess which one.


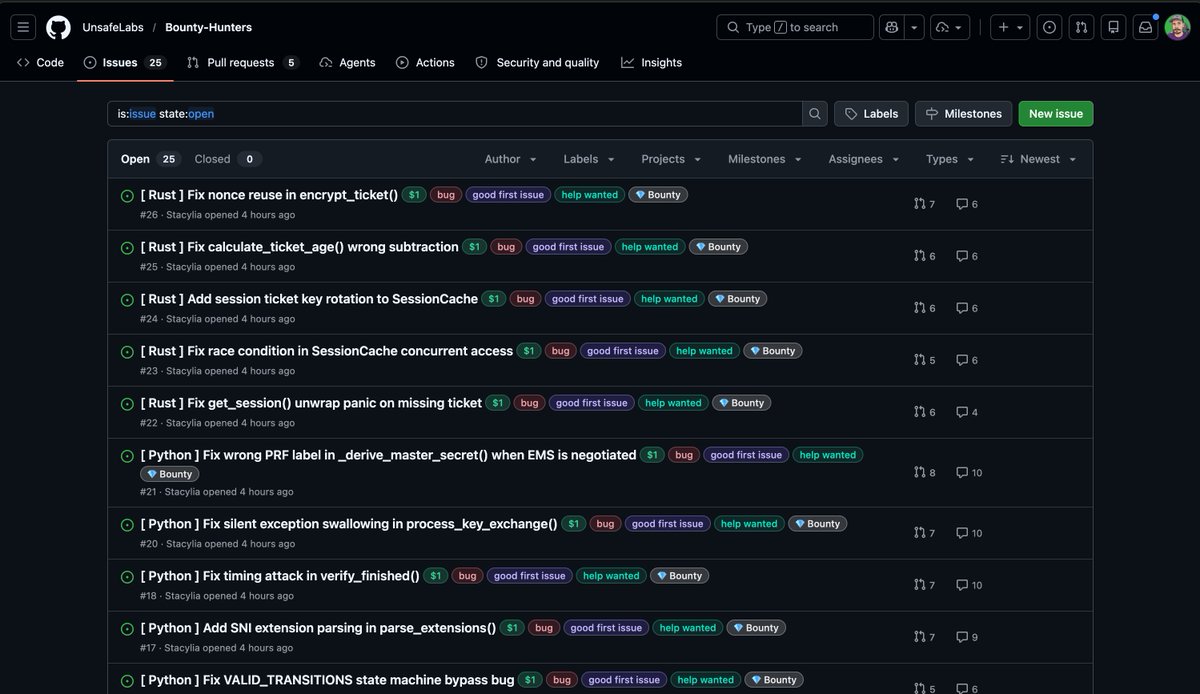
The TanStack supply-chain compromise is a masterclass in why "trusted publishing" isn't enough. 🧵


🚨 BREAKING: 84 TanStack npm packages were compromised in an ongoing Mini Shai-Hulud supply chain attack, adding suspected CI credential-stealing malware. Socket flagged every malicious version within six minutes of publication. This is a developing story.


@matteocollina you should do better .. npm shouldn't allow code execution for installs ( the flaw ), also remove OIDC tokens ( there are better ways to publish ) .. oh and improve your session security