Begin n Bounty
910 posts


Begin n Bounty
@beginnbounty
👉Practical Bug bounty tips 👉Beginner friendly 👉Pentesting DM for queries








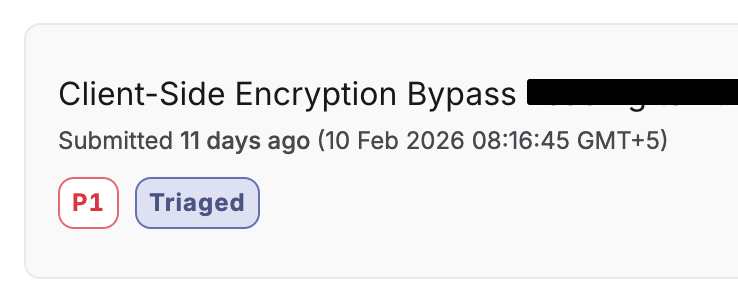
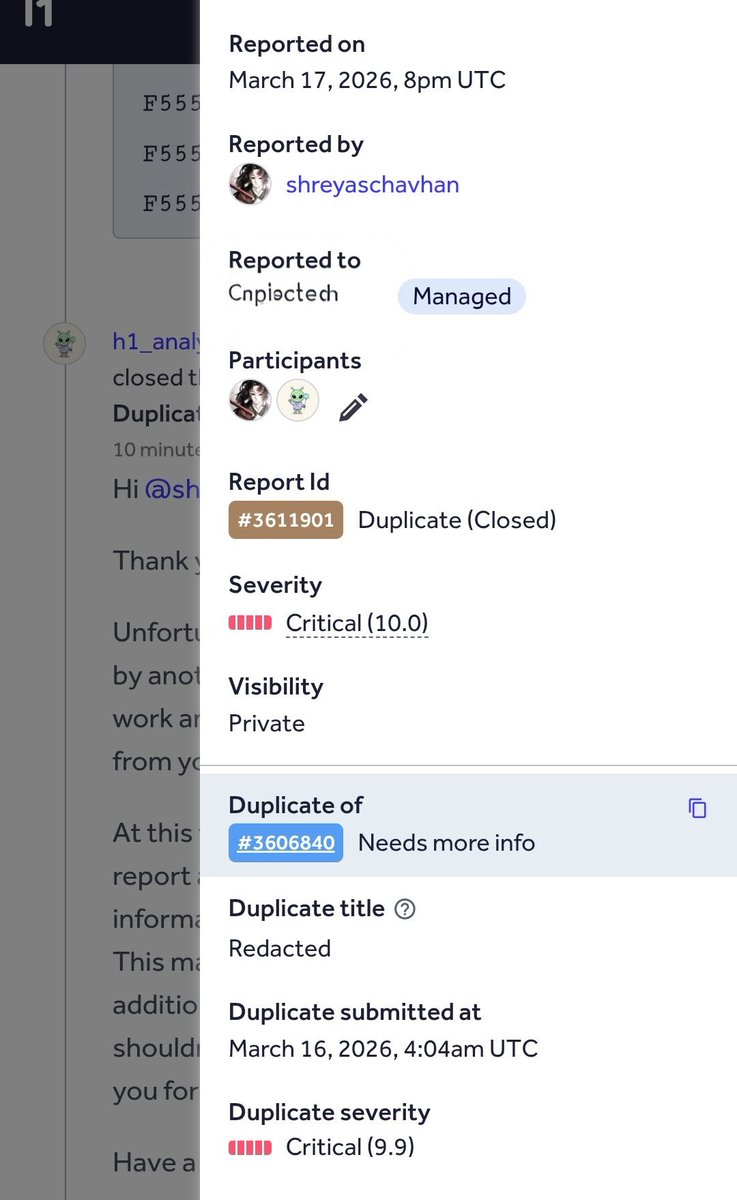
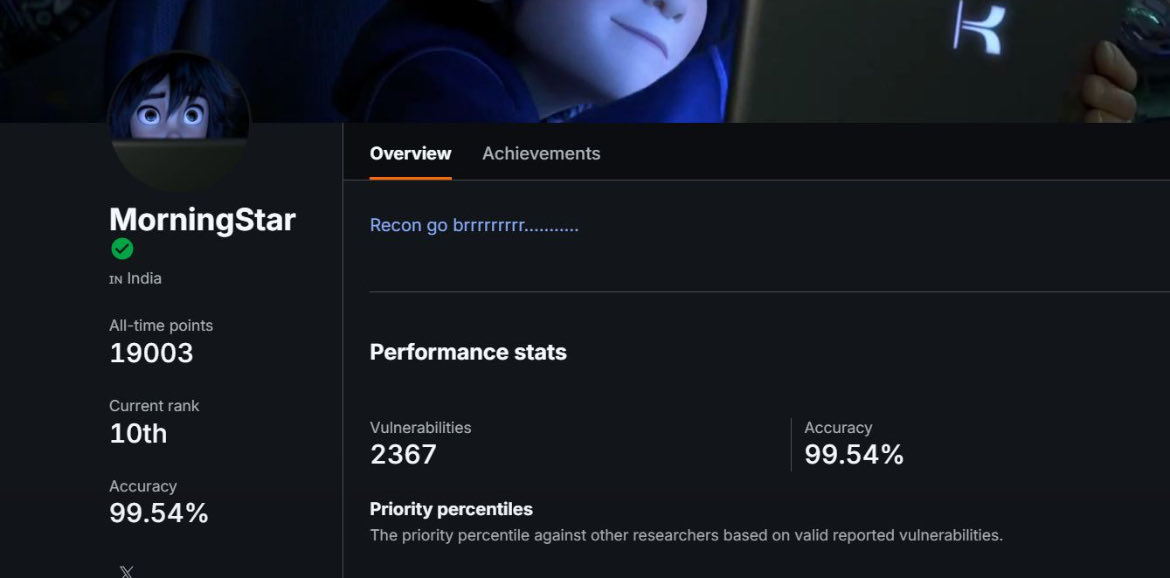
I made close to $10,000 from bug bounties this month. I'm 19. Still in engineering school. Here's what I didn't show you. I found a Critical RCE — Remote Code Execution via path traversal on a company's server. The kind of bug that pays $5,000-$20,000. Duplicate. Someone found it 12 days before me. $0. Same work. Same skill. Same report. Wrong timing. That's one of dozens. For every bounty I post, there are 15+ reports that got: → Duplicated → Marked informative → Ignored for months → Closed as "not applicable" → Lowballed after months of follow-ups But you know what I do when that happens? I wake up. No emotion. No hate. I open Burp Suite. Next target. Next report. Because if I don't, someone else will. Every day I take off is a day someone else dupes me on the next find. So I show up. Even when I don't feel like it. Even when it hurts. Bug bounty is not "find bug, get paid." It's find 50 bugs, fight for 6, get duped on some of your best work, get ghosted on others, and still show up the next morning. The $10K months are real. But behind every mountain is a hundred steps nobody sees. If you're starting out and getting duped and rejected — that IS the path. You're not doing it wrong. You're doing it. Keep going.




🔥🚨DEVELOPING: Indian State Media coverage of the conflict in Iran have been going viral due to how ‘overstimulating’ their news is compared to the rest of the planet.