beist
3.7K posts

beist
@beist
Retired security engineer but still hacking when free+beer
Seoul, Korea Katılım Aralık 2008
282 Takip Edilen6.9K Takipçiler

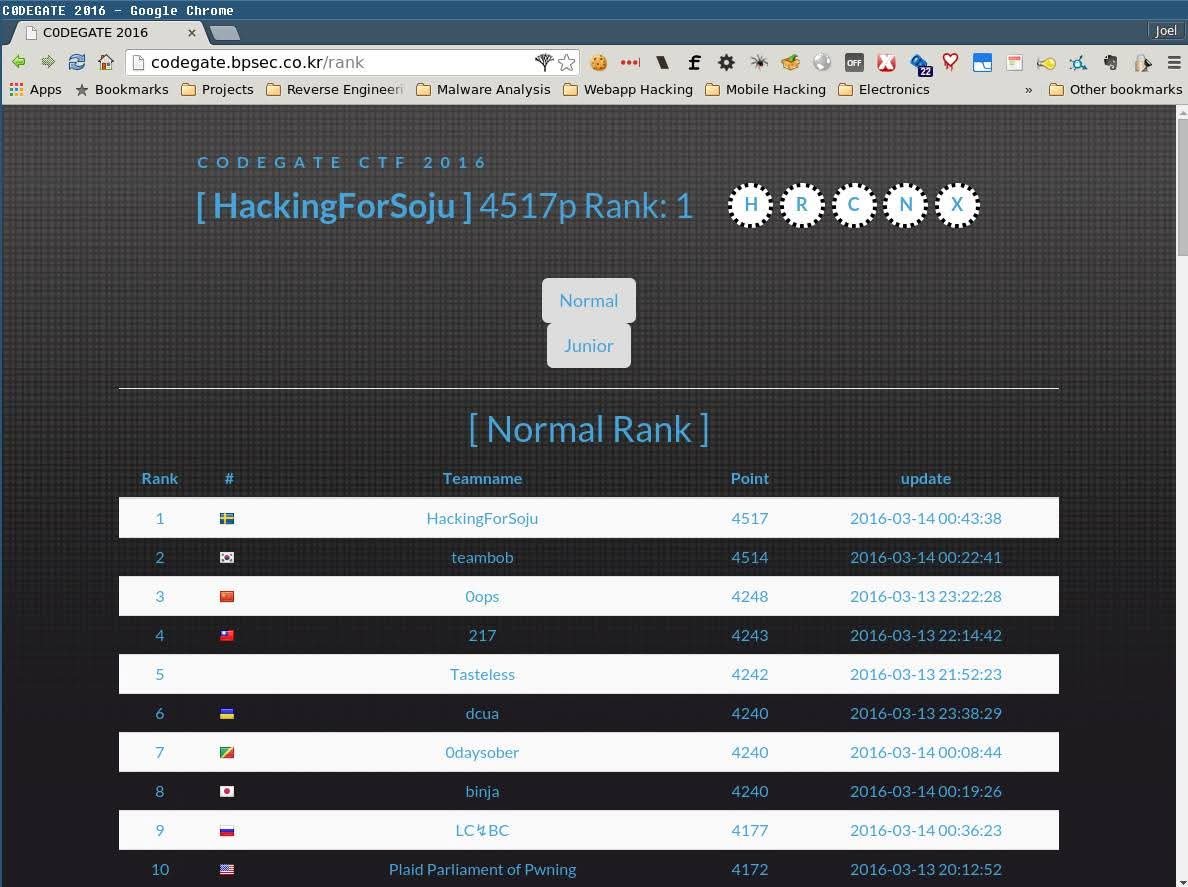
10 years ago, time flies! Competing in CodeGate with @HackingForSoju and partying with @beist was always lots of fun 😃
English
beist retweetledi
SPR was designed specifically to eliminate these attacks. Almost all other WiFi deployments carry inherent disconnects between L2/L3 that enable MITM attacks and packet injection, whether EAP-TLS or WPA3.
Matthew Green@matthew_d_green
This seems bad for WiFi encryption: arstechnica.com/security/2026/…
English
beist retweetledi

Reminder we are looking for talented security researchers in all areas (iOS, Android, Browser, 0click, AI) 🚀🚀 DM me or shoot us an email at catalystsecurity.com 🦊
English

@alfiecg_dev I came across an article about your talk - dailysecu.com/news/articleVi… I wasn’t able to attend PoC this time, so I couldn’t listen to your talk. Will the slides be released soon? And is the content mostly the same as what you’ve written on your blog?
English

Slides coming soon :) Thanks for the great conference!
POC_Crew@POC_Crew
Master of JSE Samuel Groß (@5aelo) – JavaScript Engine Security in 2025: New Bugs, New Defenses 🌐 #POC2025
English

@seanhn I found chairs with wheels, though they don’t have armrests. There’s Solo Booth at Starbucks Circles Ginza. I haven’t visited it yet, but I’m planning to check it out soon. Seems nice!
tokyoweekender.com/japan-life/sta…
English

@beist I failed at finding this for months so I hope you have better luck than me ;) The Share Lounge in the Marunouchi building (Tokyo station) has external monitors and you can swap between standing and sitting desks, but the chairs aren’t great =\
English
beist retweetledi

🔺iPhone models announced today include Memory Integrity Enforcement, the culmination of an unprecedented design and engineering effort that we believe represents the most significant upgrade to memory safety in the history of consumer operating systems. security.apple.com/blog/memory-in…
English

For those not keeping track, this past weekend at DEF CON @theori_io got:
* Yet another first place win at DEF CON CTF (9th win for many of us)
* A Pwnie for best priv esc bug
* 3rd place at DARPA's AIxCC
So proud to work at such an awesome company and security powerhouse 💪🏻👨🏻💻
English

These days, when I see the results of bug hunting using AI, I truly feel glad that I retired early.
Theori at aixcc: theori.io/blog/exploring…
Google big sleep: issuetracker.google.com/issues?q=compo…
Xbow: xbow.com/blog/top-1-how…
English
beist retweetledi

As a New Year resolution, consider applying to Project Zero :)
Tim Willis@itswillis
It doesn't happen very often, but Project Zero is hiring! goo.gle/41DBQBY Please share with anyone you think would be awesome for the role 🎉 Looking for at least one person. DMs open if you want to reach out about the role. The team: youtu.be/My_13FXODdU
English

The Parallels VM escape bug reminds me of a bug I reported to VMware about two years ago. I was waiting until a patch was released before posting, but I ended up forgetting. Just an LPE bug on the host side, feel free to check it out if you're curious. (A colleague of mine forgot his MacBook password, so I discovered the bug in order to read the admin hash and crack it. He made a 'guest' account luckily before.) The diagram might look ugly, tho. PoC is available if you want, but it's a simple logic bug, so easy to exploit.

English