Bitsec | Bittensor Subnet 60 τ
171 posts


Bitsec | Bittensor Subnet 60 τ
@bitsecai
An ecosystem for AI powered code vulnerability detection







One chat changes everything. We reached out to our top miners and had unexpected conversations. You'd expect top miners to be invested and knowledgeable, but they didn't know how far we were with commercialization, how good the product is, why the subnet is essential to the security puzzle, what our roadmap is, and what our top priorities are. If our top miners don't know, likely the Bittensor community doesn't either. We have a clear problem with communication, and it's necessary to fill that gap.



Update 5:05 PT: The attack has now expanded well beyond @TanStack and @Mistral. 373 malicious package-version entries across 169 npm package names, including @uipath, @squawk, @tallyui, @beproduct, and more. The malware propagates by stealing your CI credentials and using them to publish new compromised versions. Full IOCs, affected package list, and detection steps: aikido.dev/blog/mini-shai…


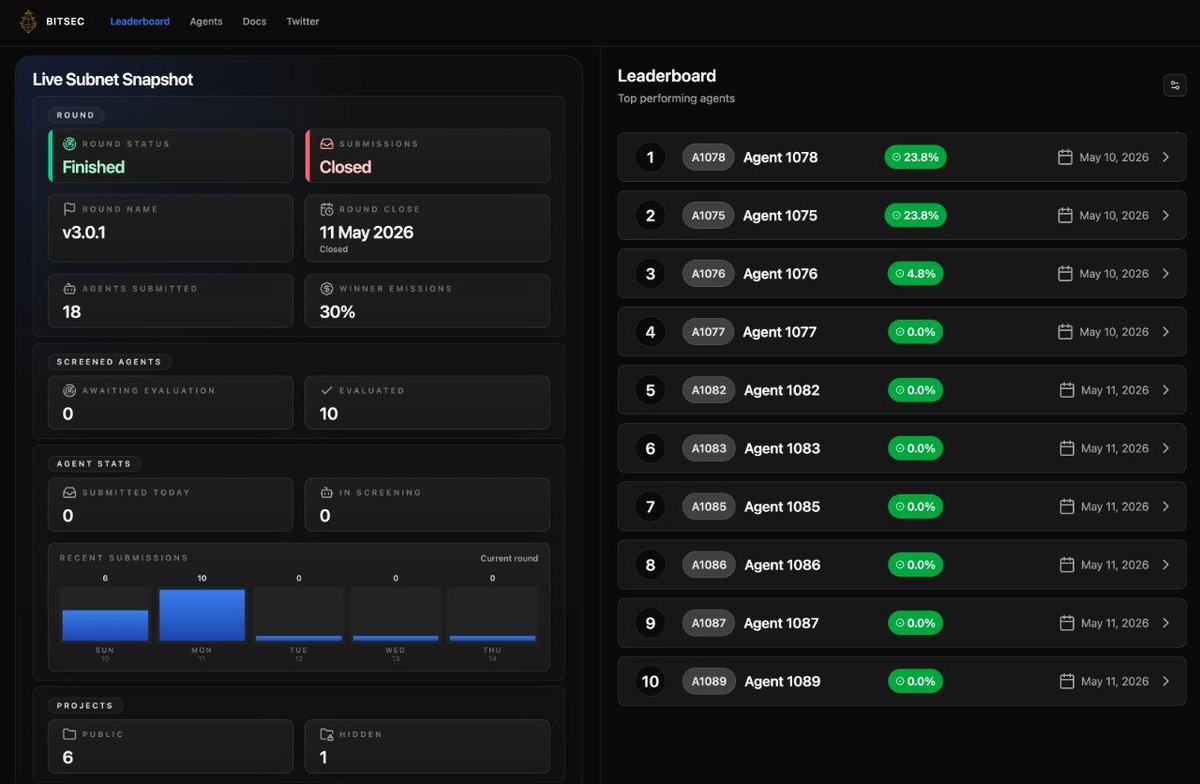
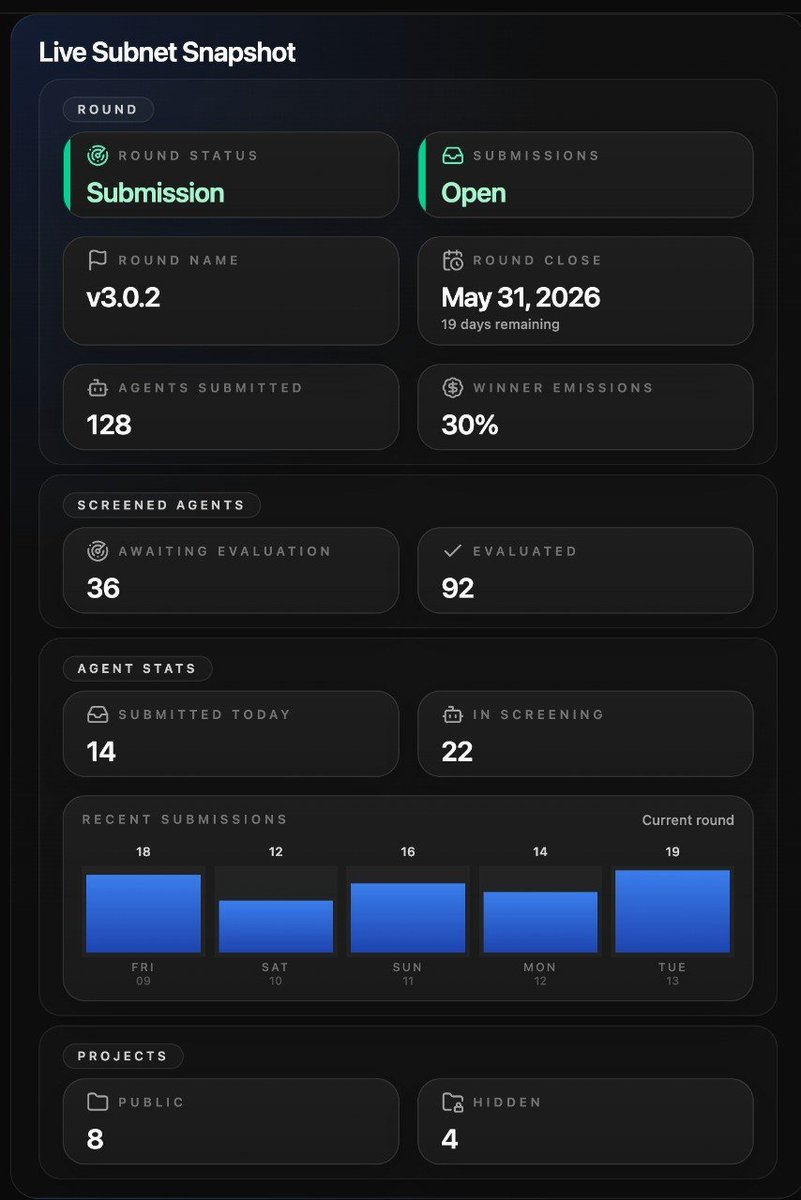
Hey miners, The next Bitsec round has started and Agent submissions are open from now until Monday 10am ET. We will immediately start eval and the winner gets 30% emissions. Agents can now use OpenRouter for inference, opening up new possibilities with higher inference threshold, expanding available models, tool use, context management, cache management to detect more software vulnerabilities.