Ahmed retweetledi

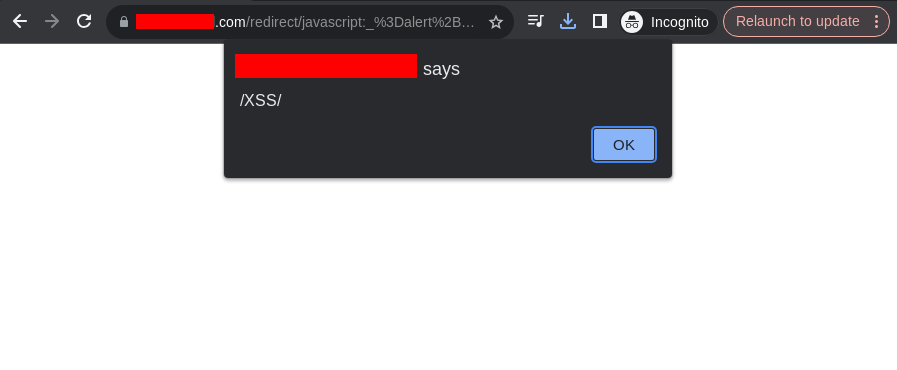
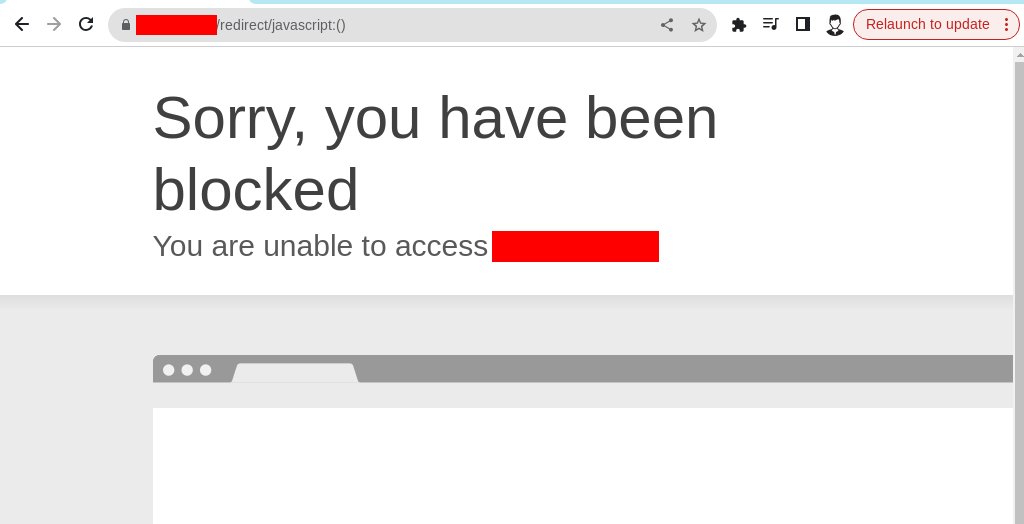
Alhamdulillah, just discovered a new bug!
-Tip:
When hunting Open Redirects, try inserting
//evil.com/..;/css in the URL
The server treats it as a local path but the browser redirects outside
Add a .js or .css file at the end.
#CyberSecurity #Hacker101 #bugbountytips #BugBounty

English