brunoshi.eth
4.2K posts
Sabitlenmiş Tweet
Quem deu follow baseado na publicidade enganosa do @OutsiderPapini fiquem avisados que eu não faço conteúdo no twitter. Minha conta é uma conta mais de retweet de temas de hacks, scams, privacidade, anonimato e segurança. Com o intuído de informar/avisar a galera sobre o tema.
Português
brunoshi.eth retweetledi
brunoshi.eth retweetledi

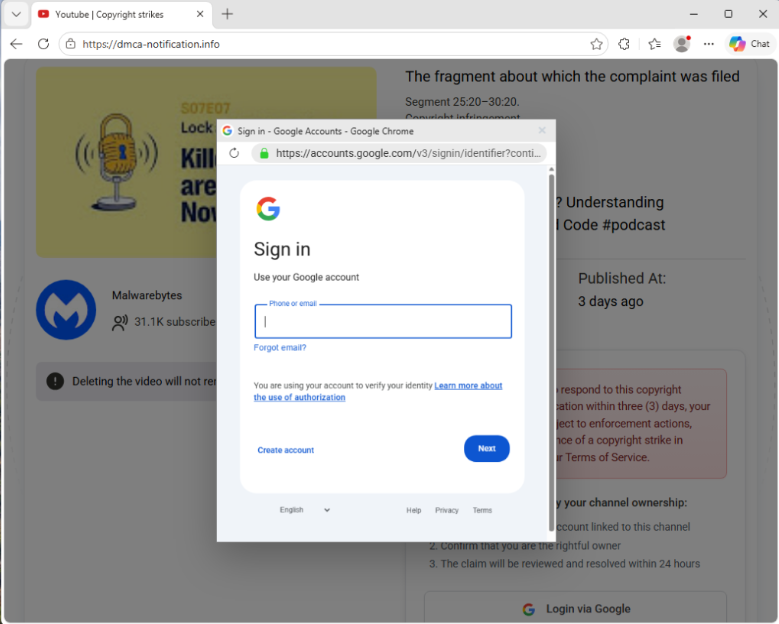
🚨 YouTube creators, beware: A new phishing scam is targeting creators by using fake copyright strike alerts in order to steal login credentials and take over YouTube accounts.
malwarebytes.com/blog/threat-in…
English
brunoshi.eth retweetledi

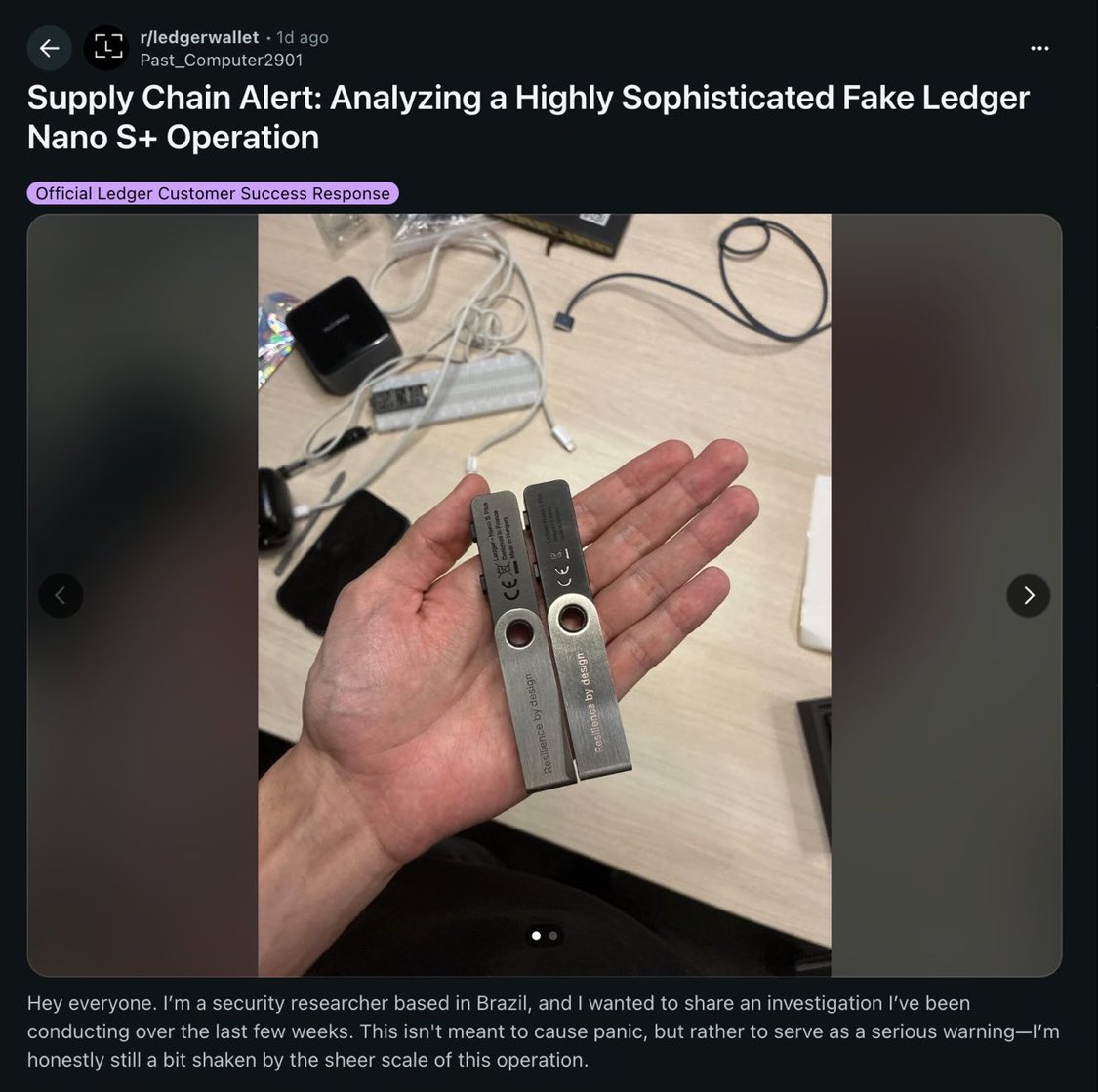
A security researcher just documented a large-scale counterfeit Ledger Nano S Plus operation selling compromised devices across multiple online marketplaces.
The fake units look identical to the real thing but contain completely different hardware. Instead of Ledger's secure element chip, the counterfeits run an ESP32 microcontroller with modified firmware labeled "Nano S+ V2.1." Seeds and PINs are stored in plain text and transmitted to attacker-controlled servers. Any wallet initialized on the device is drained.
The operation goes beyond the hardware. The sellers also distribute a fake version of Ledger Live built with React Native and signed with a debug certificate. It intercepts transactions and exfiltrates sensitive data to multiple command-and-control servers. The campaign spans five attack vectors: compromised hardware, Android APKs, Windows executables, macOS installers, and iOS apps distributed through TestFlight to bypass App Store review.
This comes days after ZachXBT documented a separate fake Ledger Live app that made it through Apple's Mac App Store review process. That operation drained over $9.5 million from more than 50 victims, including musician G. Love, who lost 5.92 BTC after entering his recovery phrase into what he believed was the legitimate app.
The pattern is clear: the attack surface for hardware wallet users has shifted from firmware exploits to supply chain and distribution fraud. The devices themselves remain secure. The problem is that users are being intercepted before they ever touch a real one.
Ledger's own "genuine check" feature can be bypassed when the hardware itself is compromised at the source, which makes where you buy the device as important as how you use it.
The rules haven't changed, but they've never been more important: buy hardware wallets only from the manufacturer. Never enter your recovery phrase into any software. If a companion app asks for your 24 words on a screen, it's a scam. Every time.
English
brunoshi.eth retweetledi
brunoshi.eth retweetledi

Russian crypto exchange Grinex paused trading services after a $13 million exploit it says was conducted by "foreign special services." decrypt.co/364656/russian…
English
brunoshi.eth retweetledi

The Ethereum Foundation reported that a six-month program helped expose around 100 DPRK IT workers across 53 crypto projects. decrypt.co/364671/ethereu…
English
brunoshi.eth retweetledi

⚠️ Attackers are using Obsidian’s plugin system to run malware.
Targets move LinkedIn → Telegram → shared vault, where code runs only after enabling plugins. The payload deploys PHANTOMPULSE with Ethereum-based C2.
🔗 Read how → thehackernews.com/2026/04/obsidi…
English
brunoshi.eth retweetledi

🚨 Critical Chrome Vulnerabilities Let Attackers Execute Arbitrary Code – Update Now!
Source: cybersecuritynews.com/chrome-vulnera…
Google has rolled out a crucial security update for its Chrome browser, addressing 31 vulnerabilities that could leave systems exposed to severe cyber threats.
Released on April 15, 2026, this Stable Channel update requires immediate attention from users worldwide, as the most severe flaws could allow attackers to execute arbitrary code on targeted machines.
The latest Chrome update, bringing the browser to version 147.0.7727.101/102 for Windows and macOS, and 147.0.7727.101 for Linux, tackles a massive batch of security defects.
#cybersecuritynews
English
brunoshi.eth retweetledi
brunoshi.eth retweetledi
brunoshi.eth retweetledi

Fake Claude AI installer mimicking Anthropic spreads PlugX RAT on Windows, using DLL sideloading to gain persistent remote access to infected systems.
Read: hackread.com/fake-claude-ai…
#CyberSecurity #ClaudeAI #Windows #PlugX #Malware
English
brunoshi.eth retweetledi

UPDATE:
We now have full control of the cow.fi domain.
CoW Swap has been working as normal at cow.finance for some time now, and we are now working to transition it back to it's original domain.
In the meantime, here is an update on we know about the incident so far and what you should do if you were impacted. 👇🧵
English
brunoshi.eth retweetledi

Over 100 Chrome extensions in Web Store target users accounts and data
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
English
brunoshi.eth retweetledi

⚠️ Microsoft Patch Tuesday April 2026 168 Flaws Patched With Actively Exploited 0-day
Source: cybersecuritynews.com/microsoft-patc…
Microsoft has released its April 2026 Patch Tuesday security update, addressing 168 vulnerabilities across its product portfolio, including one actively exploited zero-day and one publicly disclosed flaw that organizations must prioritize immediately.
The most critical issue in this month's release is CVE-2026-32201, a Microsoft SharePoint Server Spoofing Vulnerability currently being actively exploited in the wild.
This flaw allows attackers to conduct spoofing attacks against SharePoint environments, posing a significant risk to enterprises relying on SharePoint for document management and collaboration.
#cybersecuritynews #patchtuesday #Microsoft

English
brunoshi.eth retweetledi

🛡️ Critical Chrome Vulnerabilities Let Attackers Execute Arbitrary Code
Source: cybersecuritynews.com/chrome-vulnera…
Google has released Chrome 147 to the stable channel for Windows, Mac, and Linux, patching a sweeping set of security vulnerabilities, including two critical-severity flaws that could allow remote attackers to execute arbitrary code on targeted systems.
The most severe vulnerabilities in this release are CVE-2026-5858 and CVE-2026-5859, both carrying a Critical severity rating and commanding a $43,000 bug bounty reward each. CVE-2026-5858 is a heap buffer overflow in WebML Chrome’s implementation of the Web Machine Learning API.
#cybersecuritynews #Chrome
English
brunoshi.eth retweetledi
brunoshi.eth retweetledi

UPDATE: The swap dot cow dot fi domain is currently locked and not accessible. We are working with security experts to assert control over the domain while it is locked, but we *do not* expect it to be live again tonight.
For those who rely on CoW Swap daily, we have spun up a new instance of the CoW Swap UI at swap.cow.finance, which is safe to use.
Please continue to exercise extreme caution when interacting with any websites (including the new URL above) or social media accounts purporting to be CoW Swap. Only rely on official communications from this channel or on Discord surrounding the status of CoW Swap.
Anna George@AnnaMSGeorge
We have a new instance of CoW Swap live now at cow.finance to allow safe usage of the protocol. Please remain cautious and continue to refrain from using swap dot cow dot fi until the team signals it is safe to use.
English
brunoshi.eth retweetledi

🚨CoW Swap front-end got hit and we’re already seeing ~$1M+ drained across a few wallets.
If you interacted — revoke approvals ASAP.
Dropping txs from a few victims that already got caught 👇
etherscan.io/tx/0xcee016925…
etherscan.io/tx/0xab5fbfd45…
CoW DAO@CoWSwap
🚨🚨 UPDATE: CoW Swap experienced a DNS hijacking at 14:54 UTC (approximately 90 minutes ago). The CoW Protocol backend and APIs were not impacted, but we have paused them temporarily as a precaution. We are now actively working to resolve the situation. Please continue to refrain from using swap dot cow dot fi until we confirm that it is safe to use.
English
brunoshi.eth retweetledi

🚨🚨
UPDATE: CoW Swap experienced a DNS hijacking at 14:54 UTC (approximately 90 minutes ago).
The CoW Protocol backend and APIs were not impacted, but we have paused them temporarily as a precaution.
We are now actively working to resolve the situation. Please continue to refrain from using swap dot cow dot fi until we confirm that it is safe to use.
English
brunoshi.eth retweetledi

⚠️⚠️⚠️
We've received reports that the CoW Swap frontend was compromised.
If you've used the CoW Swap website today, make sure to check revoke.cash and revoke any recent approvals that you don't recognise. Stay safe!
CoW DAO@CoWSwap
🚨🚨 We are currently experiencing an issue with the CoW Swap frontend (swap.cow.fi). While we are investigating, please DO NOT use CoW Swap.
English