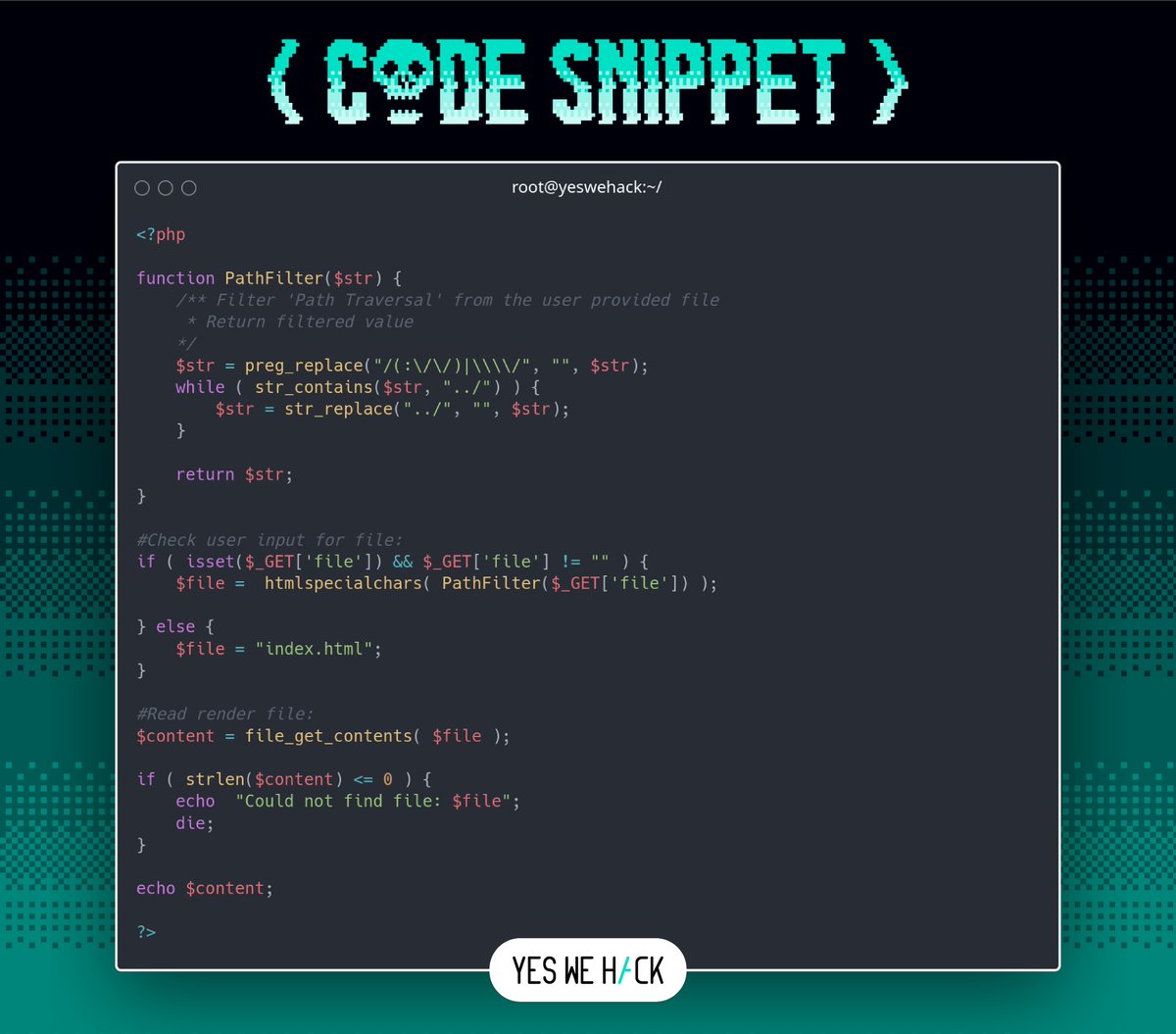
Vulnerable Code Snippets Time 🥷
Level: Medium 🐝
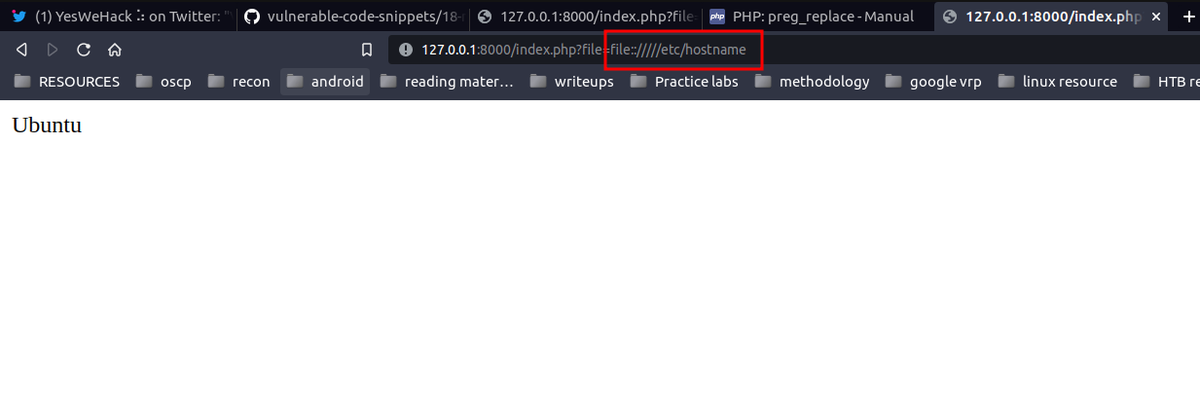
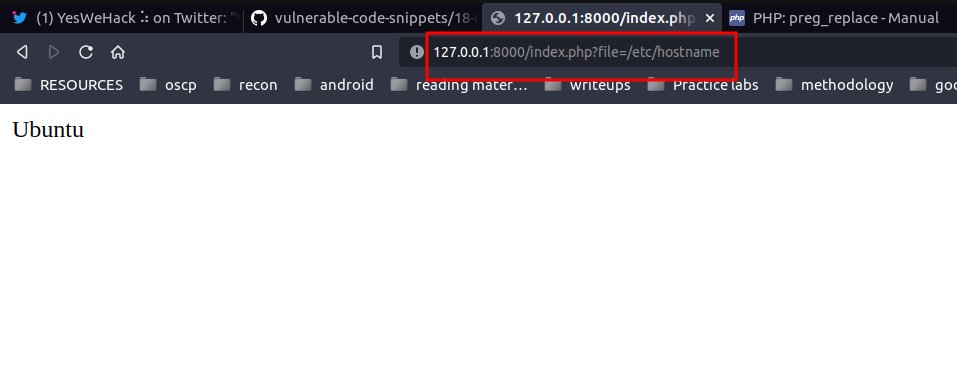
This web application does not like dot dot slash!
Try it out at Github: github.com/yeswehack/vuln…
#BugBounty #YesWeRHackers
Found the issue? Explain how in the comments! 👇
🎁 The best solution gets an exclusive swag!
English