5pider
3K posts

5pider
@C5pider
research & developer @InfinityXCurve






After 10 years at Elastic/Endgame, today is my last day. Incredibly proud of what this small but mighty team has built. Working alongside our community of users has been one of the most rewarding parts of the journey. On to a very exciting new adventure soon, stayed tuned!


#PhantomCLR shows again why generic detections matter in modern attacks. By targeting commonly reused functionality across different threat actors, we can detect and cover new variants from day one. In this case, the sample was already covered by multiple of our generic rules targeting: encryption routines, dynamic function resolving, shellcode allocation, and typical obfuscation indicators. Two of these rules are more than three years old and still provided coverage for this and similar variants before they were even observed publicly.


Introducing Combat Theater, a malware technique emulator built for blue teams, detection engineers and security researchers to perform testing and detection validation quickly and easily. Check out the introduction blog to learn more! combat.theater/blogs/introduc…



New research: InsomniacUnwinding "Call stack spoofing is mandatory for sleep masking" No, it's not. Surgical UNWIND_INFO preservation: ~250 bytes vs ~6KB .rdata. Signatures encrypted, stack intact, no spoofing. Github: github.com/kapla0011/Inso… Blog: lorenzomeacci.com/unwind-data-ca…

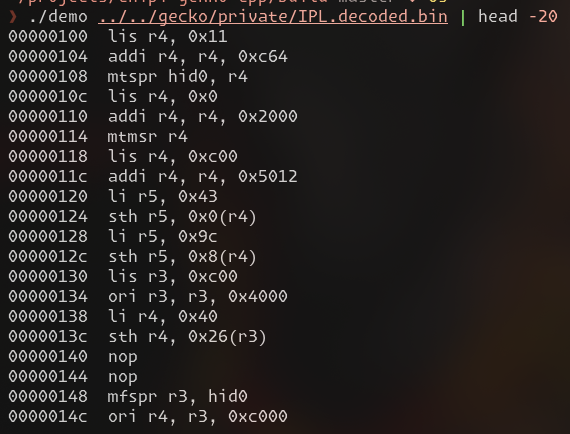
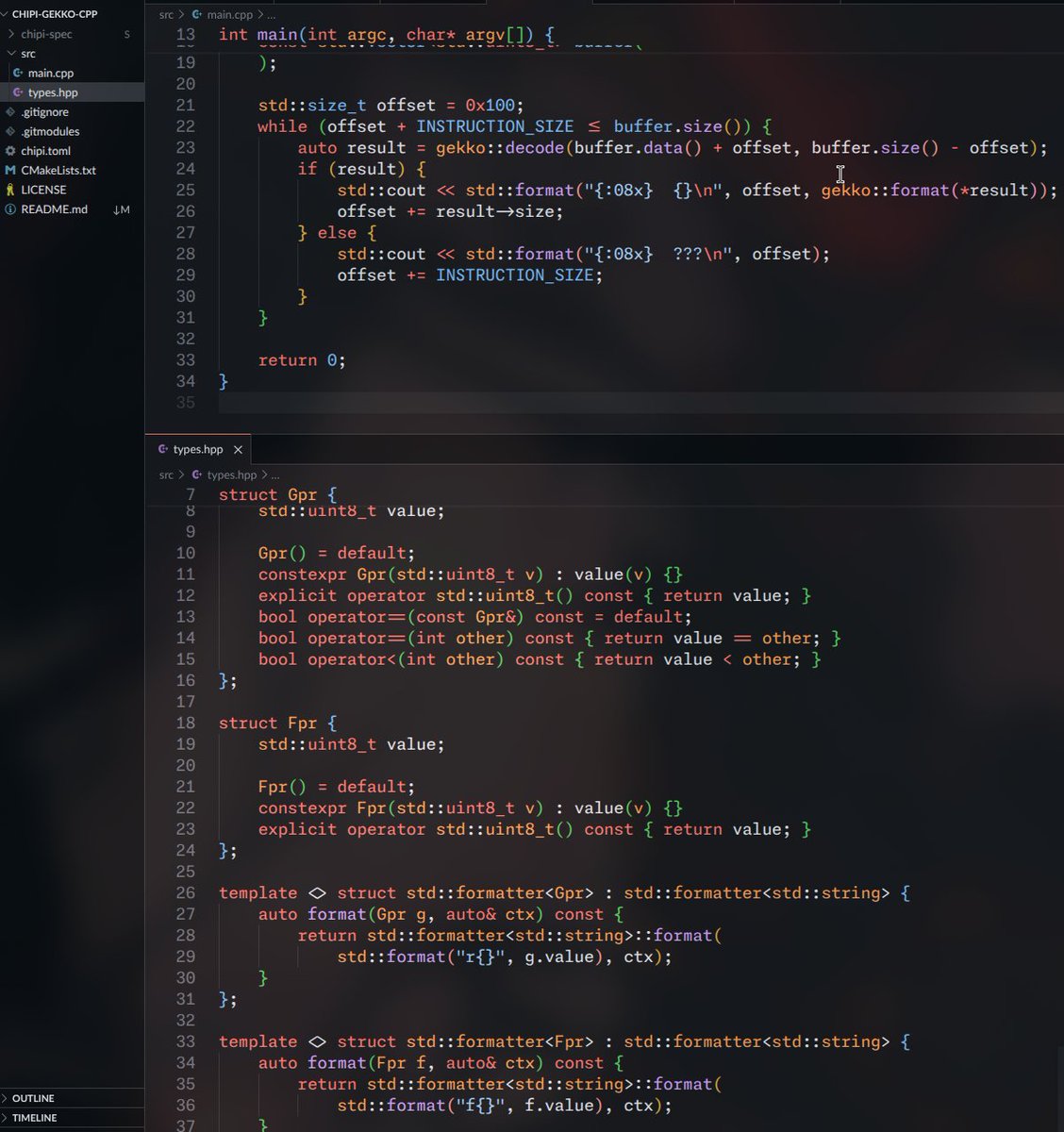
Huge update since this: - Decoupled DSL from Rust (soon backends for other languages!) - TOML support - Grouping of instructions via const generics / templates For emulators: - LUT and jump table generation for dispatch - Handler stub generation for interpreters

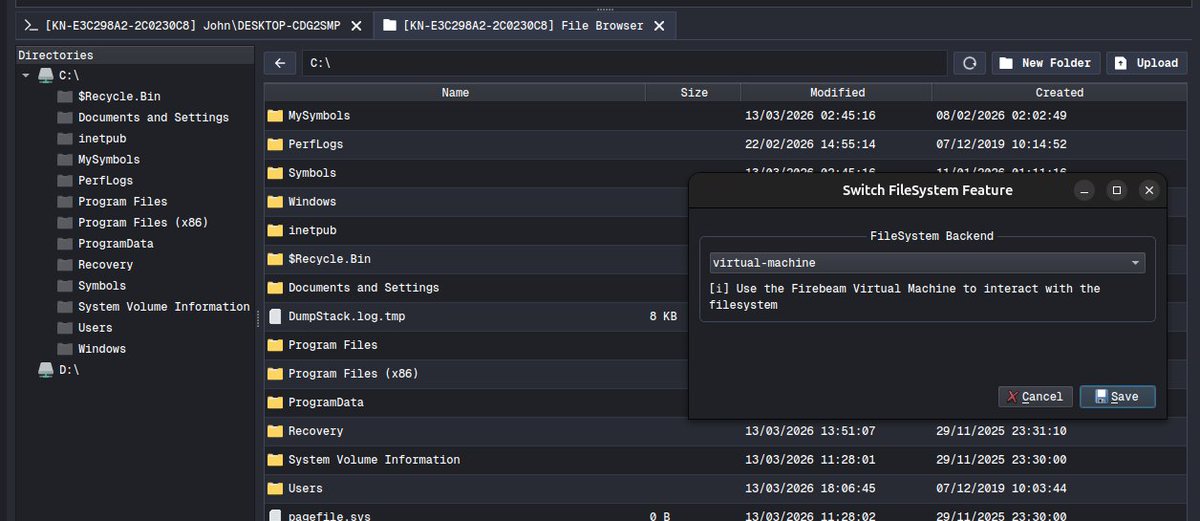
Added initial SOCKS support to CrystalC2. Keeping modularity in mind, the 'extension' needs to be enabled when building a payload. It's the CrystalC2 client that acts as the SOCKS server (rather than the C2 server), so just point tools at localhost and away you go.

You can now enable Claude to use your computer to complete tasks. It opens your apps, navigates your browser, fills in spreadsheets—anything you'd do sitting at your desk. Research preview in Claude Cowork and Claude Code, macOS only.