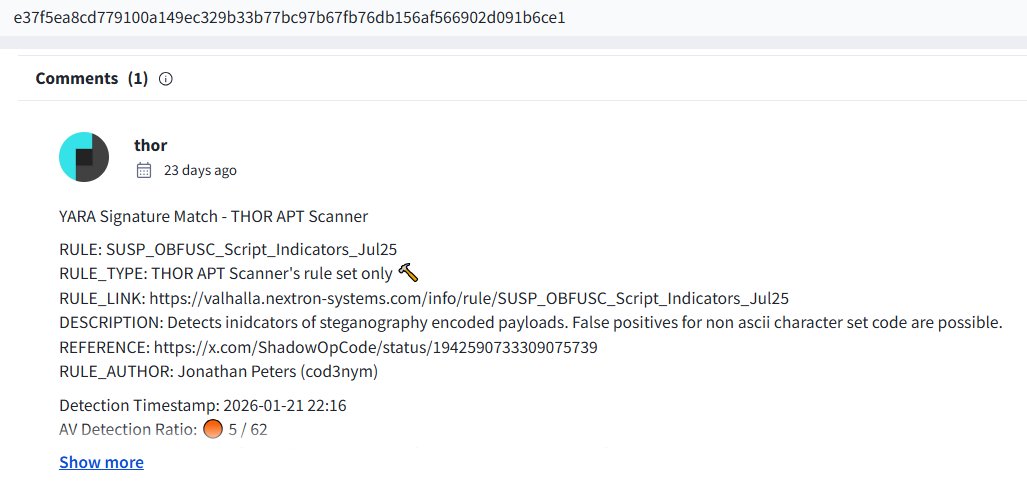
Jonathan Peters
397 posts


@cod3nym
Threat Researcher | Detection Engineer @nextronsystems @nextronresearch #Yara enthusiast | C# Developer














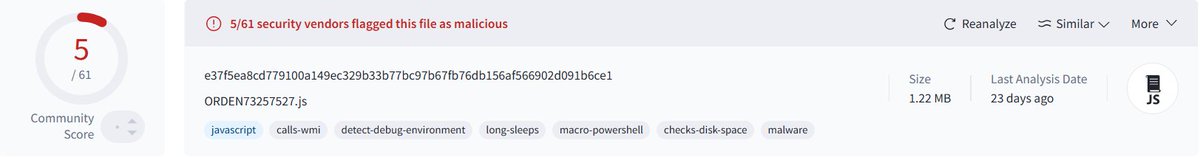

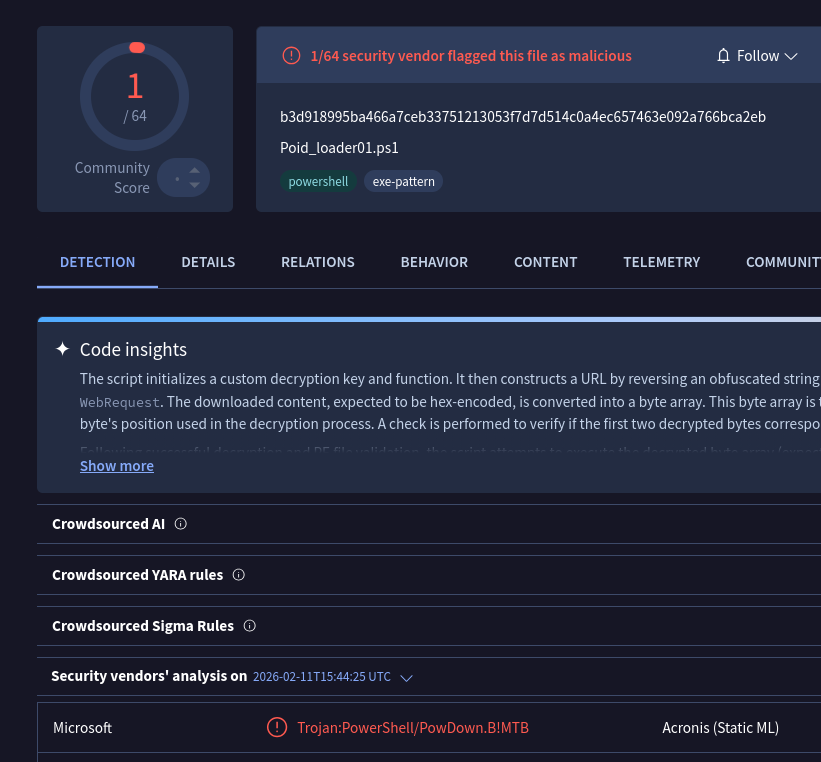

Our artifact scanner flagged what appears to be an LLM generated malware loader hosted on Gist. The PowerShell script targets MSBuild.exe, using crafted project files to load additional .NET payloads. It includes extensive debug messages and comments, typical indicators of LLM generated code. ☝️While not highly sophisticated, this highlights how threat actors are leveraging LLMs for malware development. Sample: virustotal.com/gui/file/b3d91… Original source: hxxps[://]gist[.]githubusercontent[.]com/kaporaliven/157347814587c26ae241385ea0d1302a/raw/72287b1c62e6b794622df9927fc19b5ddb658ff0/Poid_loader01[.]ps1


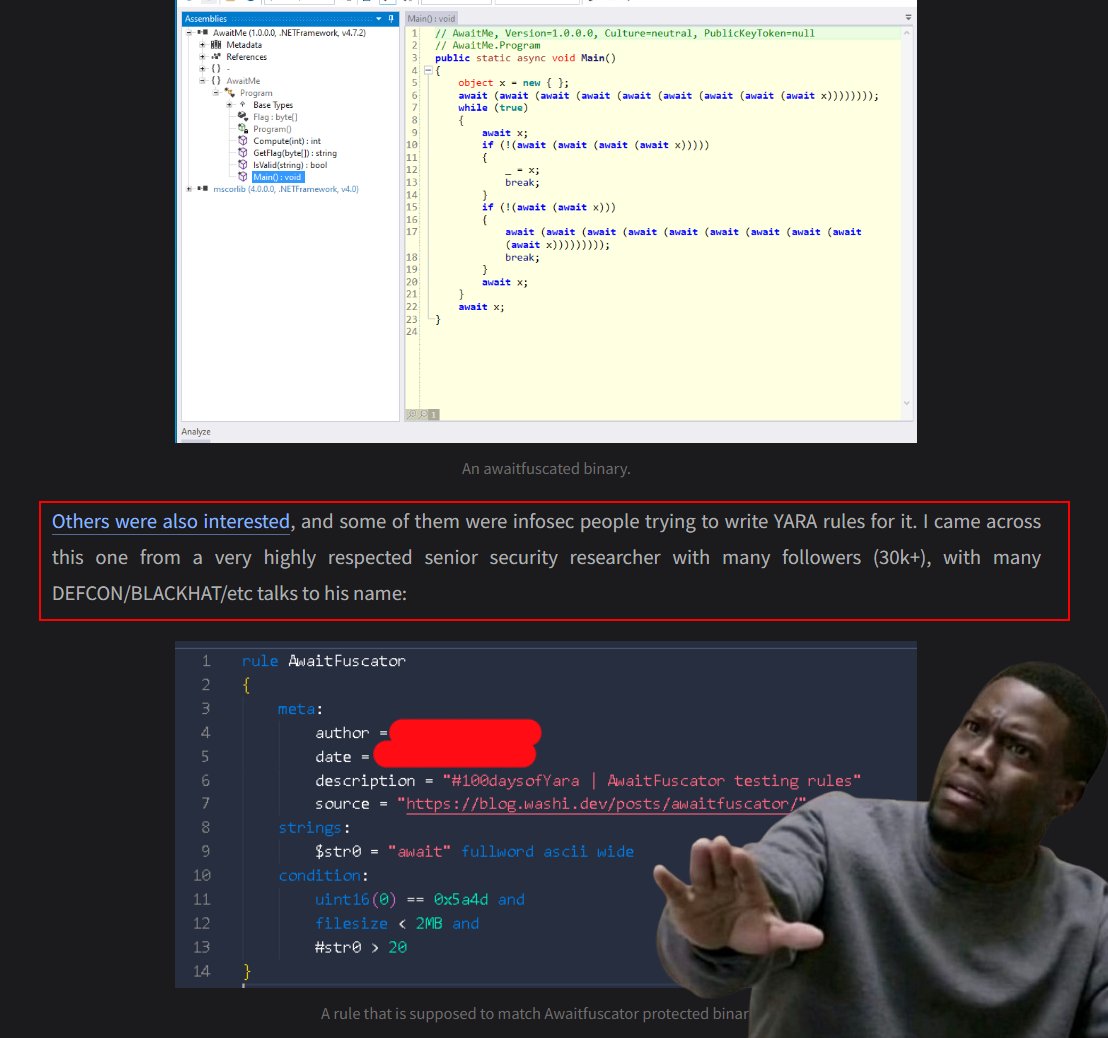
@Cyb3rMonk Maybe reach out to him privately and help him fix the query? I am sure you did it and it probably didn’t work, but the name and shame is probably not the best solution. 🙂