Chris Beckett retweetledi

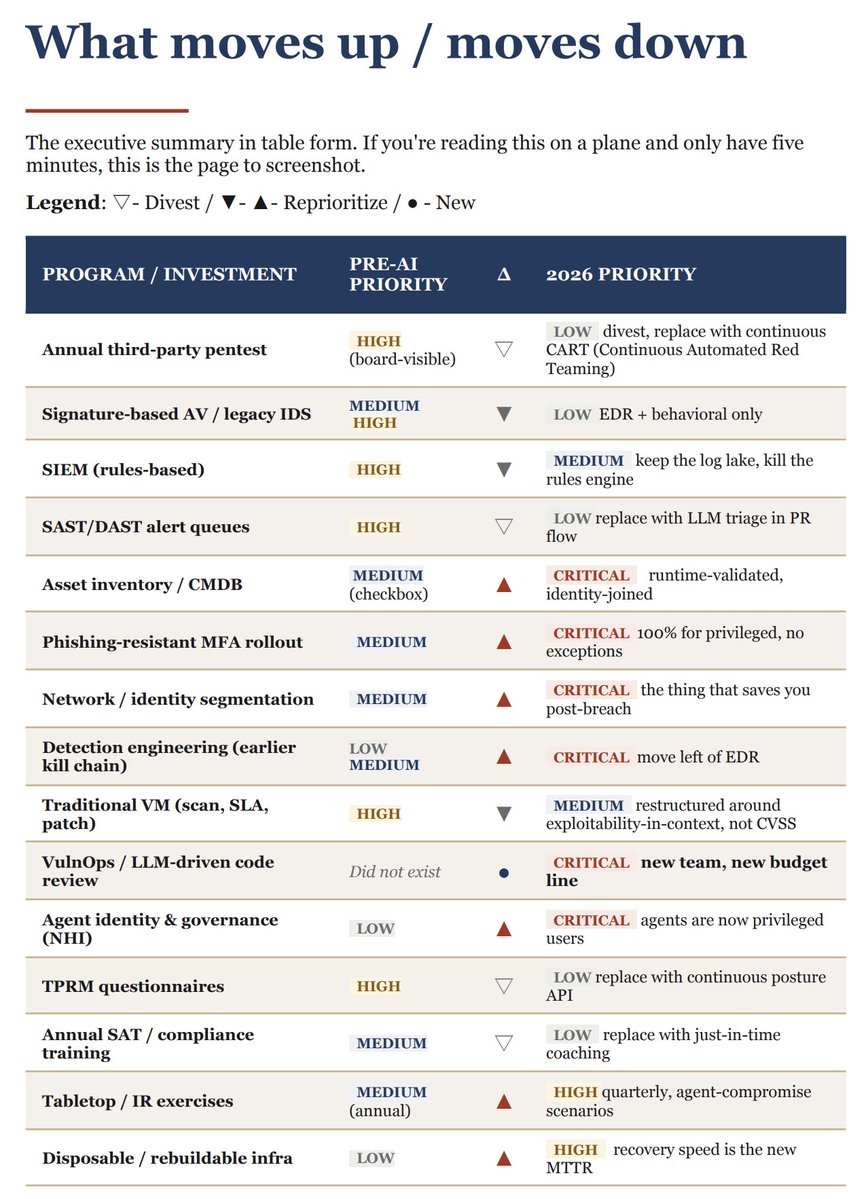
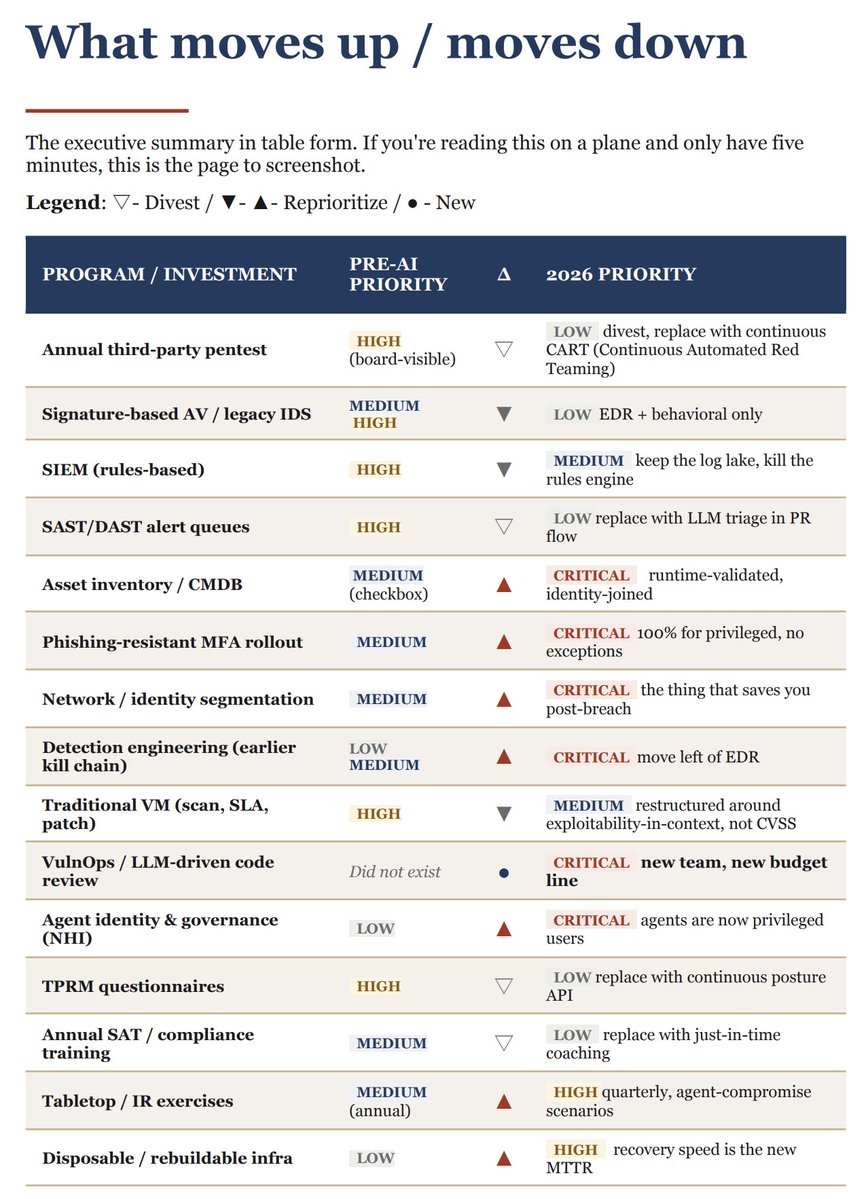
. @mubix shared this on LinkedIn and thought some of you might find it useful: “A Practical Reprioritization Guide for CISOs Entering the AI Vulnerability Era”
linkedin.com/posts/mubix_th…


English
Chris Beckett
741 posts


@cbecks_2
Infosec and the Green Bay Packers. Interested in all things DFIR, Detection Engineering, Purple, and CTI. Opinions are mine, certainly not those of my employer.








We are back! The #SecureTheBall Cyber Security Fantasy Football league returns for its ***third year***! I expect this will be the most ice filled year yet. 🧊🧊🧊


this part is brutal.













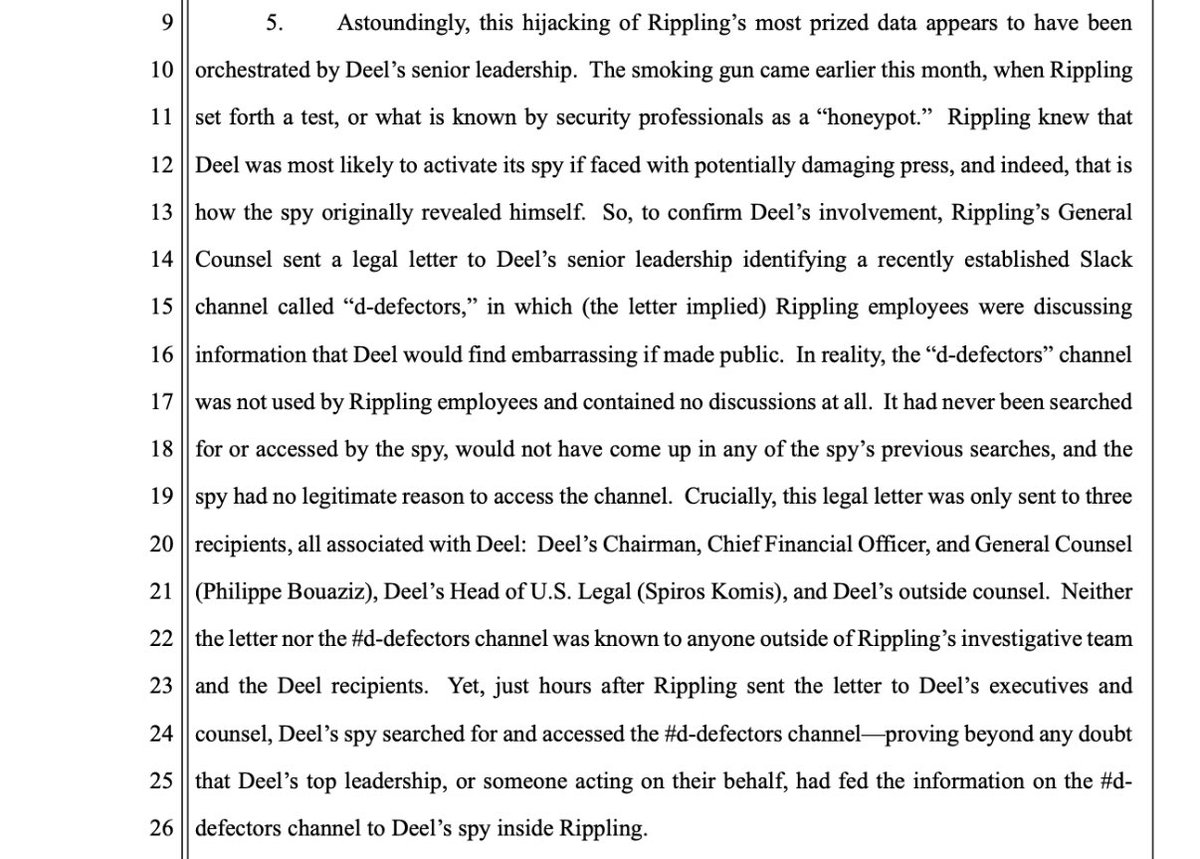
Rippling sued @Deel today. Our lawsuit alleges Deel cultivated a spy at Rippling & orchestrated a long-running trade-secret theft. The spy searched “deel” in our systems 23 times per day on avg, letting him spy on Deel’s own customers who were considering a switch to Rippling.












