Sabitlenmiş Tweet

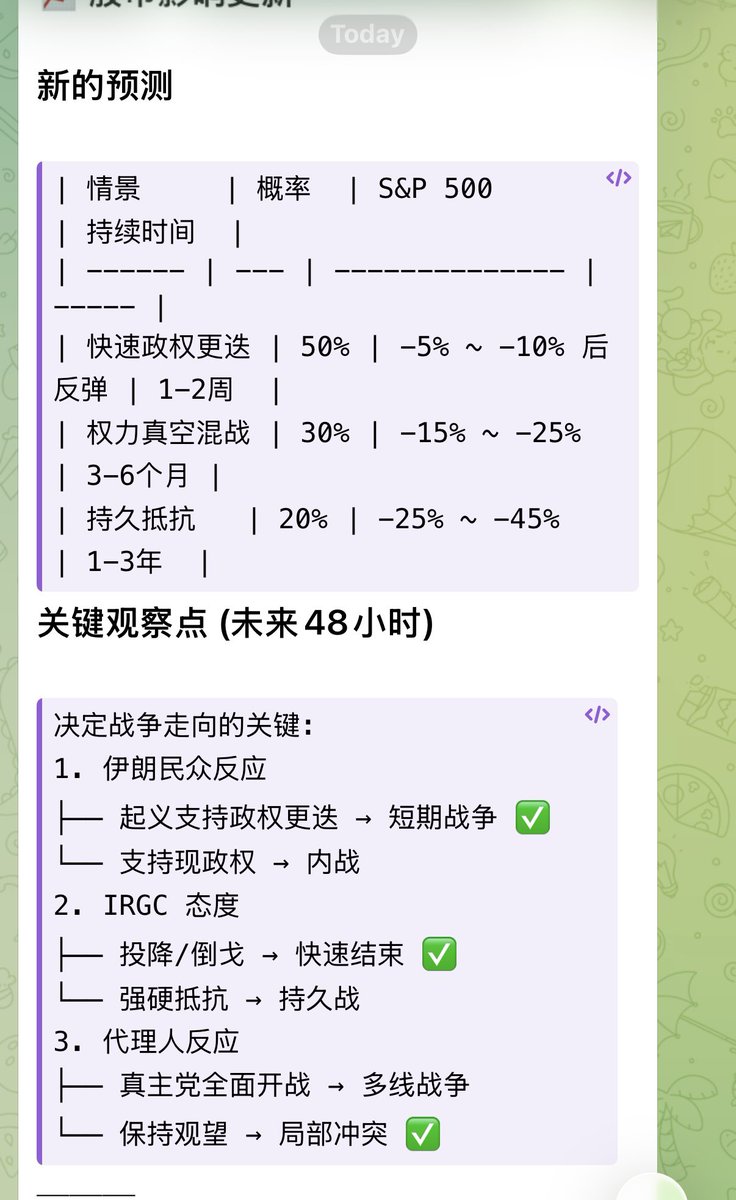
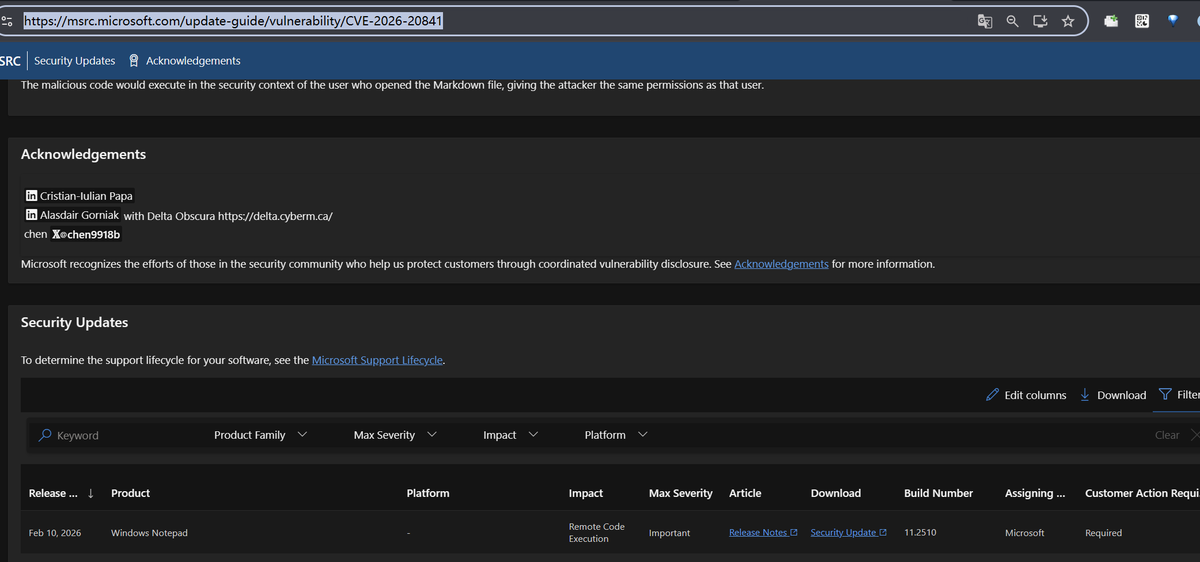
I got CVE - 2026 - 20841 in the latest Microsoft patch. I'm glad Microsoft fixed his new challenge and continued to attack the latest targets. Enjoy the hunting process. Happy hackers 😁📷
msrc.microsoft.com/update-guide/v…
@msftsecresponse
English