Me retweetledi

Shadow Credentials Attack
🔥 Telegram: t.me/hackinarticles
✴ Twitter: x.com/hackinarticles
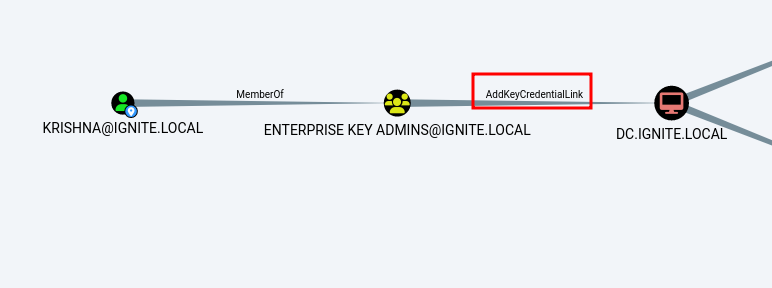
Shadow Credentials attack abuses Active Directory Certificate Services (AD CS) by injecting rogue public keys into the msDS-KeyCredentialLink attribute, allowing attackers to authenticate as a target user without knowing their password or NTLM hash.
📚 Topic Covered
📖 Introduction
🧠 Understanding Kerberos & PKINIT
🔑 msDS-KeyCredentialLink Attribute
⚙️ Prerequisites & Lab Setup
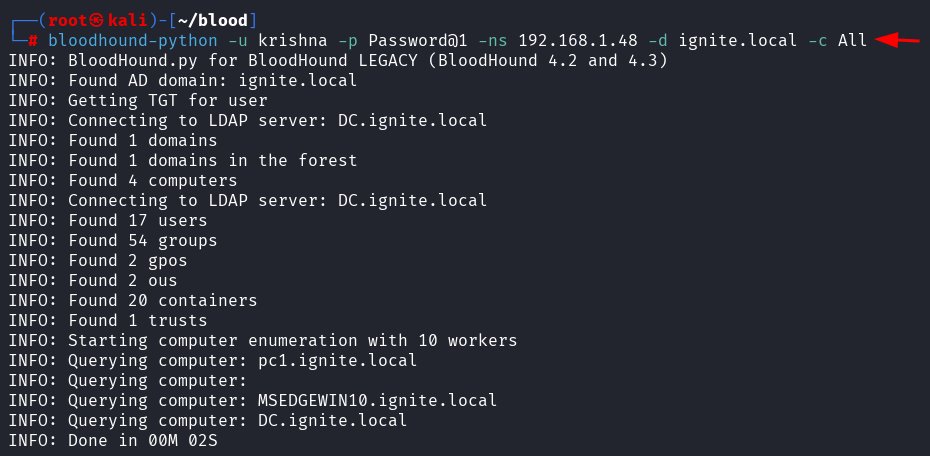
🔍 Hunting Weak Permissions (BloodHound)
💉 Injecting Shadow Credentials
📦 Tools: PyWhisker, Certipy, Impacket
🔐 PKINIT Authentication using Certificate
🎟 Obtaining TGT (Kerberos Ticket)
🪪 Extracting NTLM Hash (getnthash.py)
💻 NTLM Relay Attack (ntlmrelayx)
💣 Metasploit Shadow Credentials Module
🚀 Privilege Escalation & Persistence
🛡 Detection (Event ID 4768, 5136)
⚙️ Mitigation & Hardening Techniques
📖 Article:
hackingarticles.in/shadow-credent…
#CyberSecurity #ActiveDirectory #RedTeam #Pentesting #EthicalHacking #ADCS #Kerberos #InfoSec


English