Sabitlenmiş Tweet

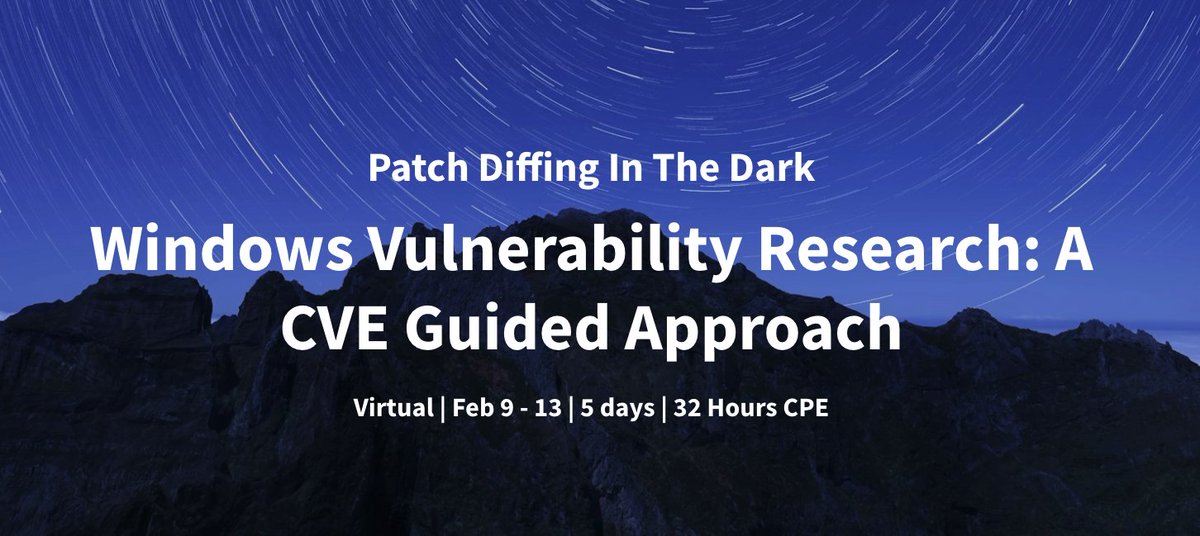
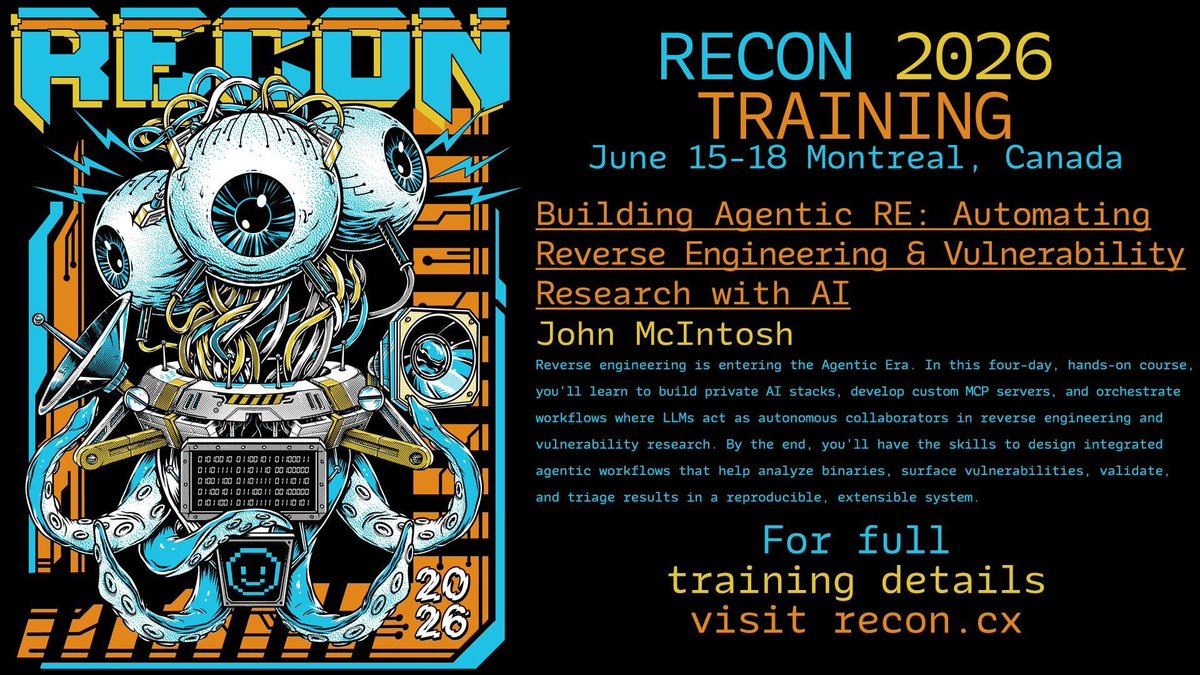
If you want RE to feel lighter and faster, not because the work is simpler, but because you’re operating with more leverage, this is where that shift starts.
@reconmtl
Training Link: l.clearseclabs.com/wuz62
English
clearseclabs
169 posts


@clearseclabs
Clear Security, Training, and Solutions Check out website for latest course offerings.


Video is up from my RE//verse talk on Agentic Diffing Apple Security Updates. If you're curious about how AI can accelerate your reverse engineering workflows, check it out. Especially useful if you're looking to get started with agentic RE.






Friendly reminder - Early Bird Pricing for our Singapore Training Event ends February 8. Signing up now reserves your spot and earns you a $250 discount. training.defcon.org #defcon #defcontraining #singapore #earlybird