crdØx.49
2.9K posts





Added 3,600+ publicly disclosed HackerOne reports that paid a bounty to the MCP. 👇 github.com/PatrikFehrenba… This should help Claude to decide where to focus on, what attack surface was looked at before, and where new vulnerabilities could be 👀 (in theory 😏)



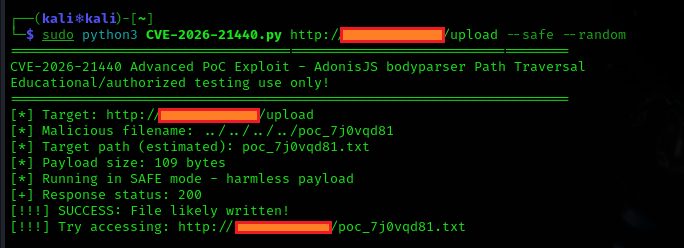
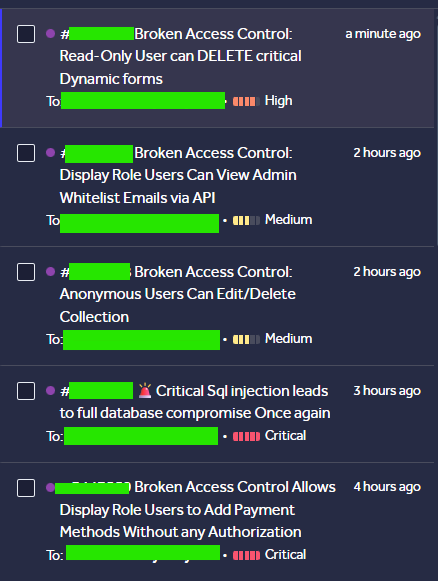
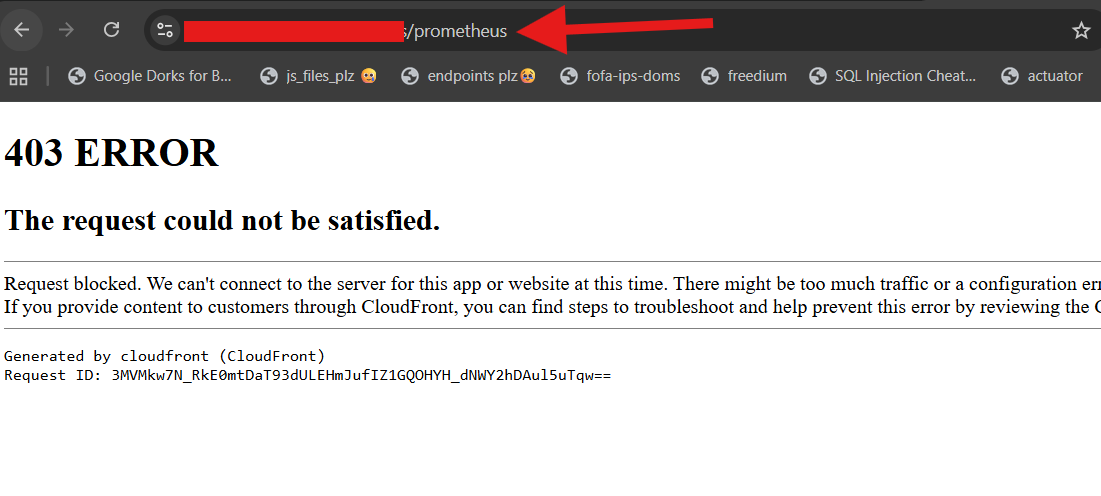
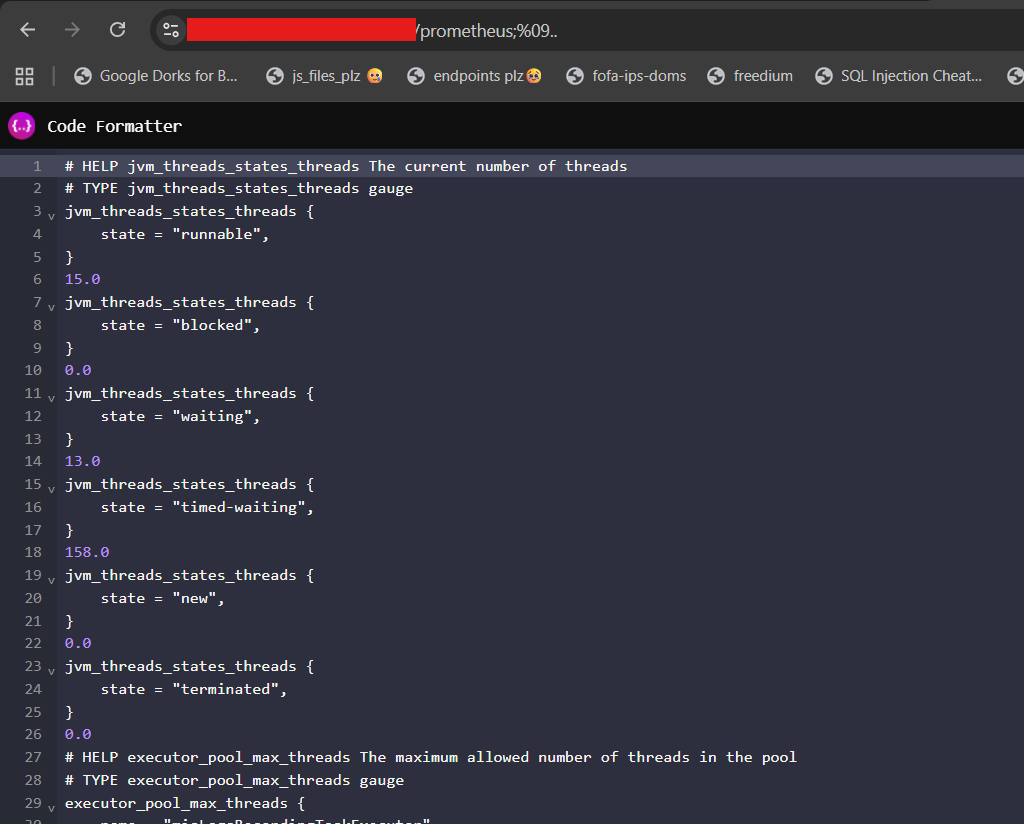
Em uma pesquisa de segurança conduzida pelo time da Hakai, foram identificadas três vulnerabilidades críticas no Centreon Web e no módulo Open Tickets. As falhas incluem SQL Injection, Path Traversal e Command Injection, permitindo desde a extração completa do banco de dados até a execução remota de comandos no servidor. Todas as vulnerabilidades podem ser exploradas por qualquer usuário autenticado, sem necessidade de privilégios administrativos. Como resultado da pesquisa, foram atribuídos três identificadores CVE: CVE-2026-2749 (CVSS 9.9), CVE-2026-2750 (CVSS 9.1) e CVE-2026-2751 (CVSS 8.3). O post irá demonstrar desde a análise técnica das vulnerabilidades, como realizar a exploração e a correção realizada pelo time do Centreon. Autor: Gabriel Rodrigues - Texugo: @g.lllllllllllllllllllllllll Confira o artigo: hakaisecurity.io/en-deep-lookin… - EN hakaisecurity.io/pt-br-deep-loo… - PT








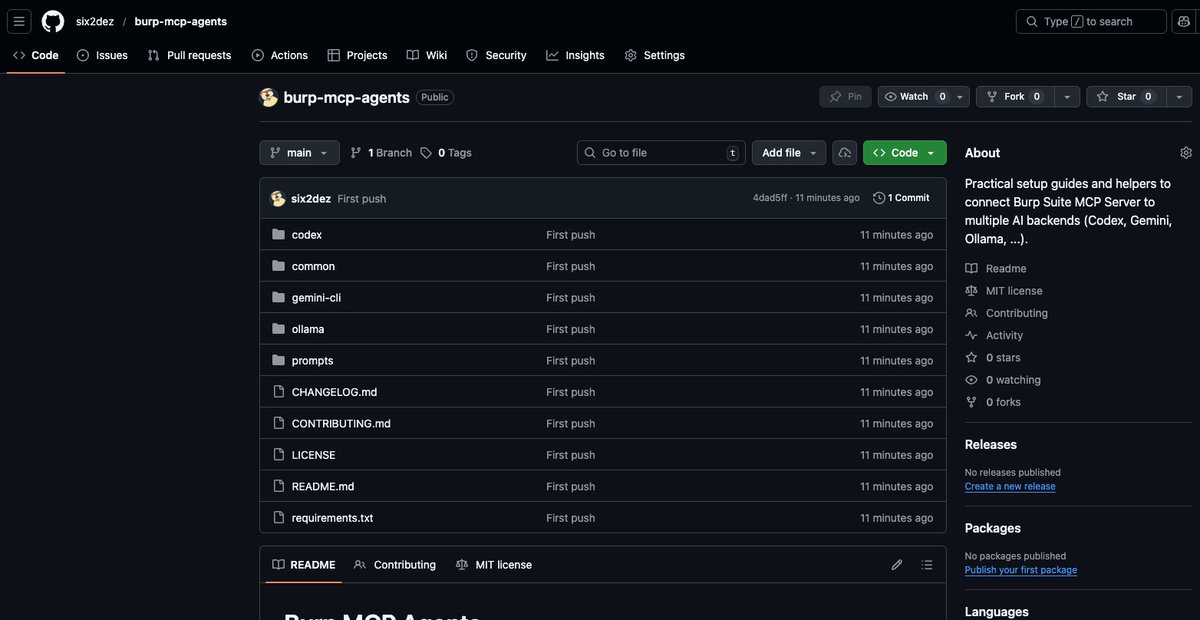
not sure who needs this, but i couldn’t find any real guide for wiring burp mcp + codex… so i wrote one live vuln reasoning on top of burp, no api keys setup is basically: burp mcp proxy jar, codex config, caddy Guide #burp-mcp–codex-cli" target="_blank" rel="nofollow noopener">pentestbook.six2dez.com/others/burp#bu…
#PenTest #Burp #bugbountytips