I graduated this weekend. I’ll be focusing on streaming for at least the next few months, and hopefully longer. I’ll be live at noon EST every day starting today. See you there 🥳
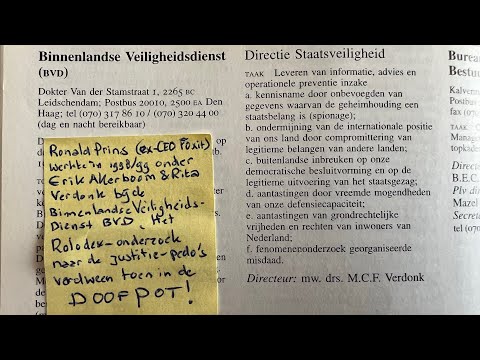
𝗥𝗼𝗻𝗮𝗹𝗱 𝗣𝗿𝗶𝗻𝘀 🇿🇦
9.5K posts


@cryptoron
Cyber Security / Hunt & Hackett / Ooit NFI/AIVD/Fox-IT/TIB/OVV/Kiesraad. Maakt podcast Cyberhelden. Zuid-Afrika is nu. 🇿🇦🇿🇦

I graduated this weekend. I’ll be focusing on streaming for at least the next few months, and hopefully longer. I’ll be live at noon EST every day starting today. See you there 🥳








Introducing Project Glasswing: an urgent initiative to help secure the world’s most critical software. It’s powered by our newest frontier model, Claude Mythos Preview, which can find software vulnerabilities better than all but the most skilled humans. anthropic.com/glasswing



⚡️🇺🇸🇮🇱🇮🇷 Numbers Station “V32” Reliable sources claim that the location from which the ciphered Farsi/Persian-language transmissions are being sent, has been pinpointed with extreme precision. I don't want to reveal the exact location. Have fun in the comments.