d0xing
796 posts


d0xing retweetledi

Let's welcome to the new bug bounty hunters
@m0chan98 @galnagli @d00xing @codecancare @m0uka_Dz @_godiego__
English

The damage of VDP programs and their Incentivization is far greater than giving some hunters "points" for farming none-bugs that they can later boast on their CV's, I believe it might actually ruin Bug Bounty platforms in the near future, Let's explore the facts 📜
So VDP's, as most people refer to "See something, Say something" type of programs, have gone out of control on most bug bounty platforms, the only one who took significant step against the phenomena is @Bugcrowd about ~2 years ago, completely dropping VDP points and truly making them live to their actual purpose.
@Hacker0x01 said at 2021 that they will be pushing to that direction, without anything meaningful so far.
So, why is it so bad?
1. "Worsening experience for Bug Bounty Hunters and Paid Bug Bounty Programs"
IMO, this is the most concerning aspect of VDP's and when platforms double-down on them - major platform resources are invested in triaging, communicating and managing VDP "Points Only" programs.
In 2024 alone, there were between ~3,500 to 5,000 VALID VDP submissions on @HackerOne (Had to do an estimate by looking at the top VDP programs).
With the signal/noise ratio on these public programs, and by looking on top VDP programs "last 90 days reports" statistics, we can see that there were around ~15,000 to 20,000 submissions to VDP programs in 2024, those are being handled by the same Triage teams and same queues that Bug Bounty Programs who pay money to researchers are, thats probably more or if not the same amount of total submissions to all paid BBP programs on the platform, which are ~x5/x6 in numbers.
This leads to:
A. Significant Triage Burn-Out, Triage teams go through hundreds of invalid reports, or hundreds of same-issue submissions that are being triaged individually, exhausting the triage experience on paid bug bounty programs, in which the reports usually are more complex and require better in-depth overview.
B. Absurd triage times - critical reports to CLEAR / BBP programs who are not being looked for over a week, programs miss out on their critical bugs while they are exploitable, hunters miss out on their bugs being paid.
C. Almost none-existing communications on submissions, enormous triage queues and VDP overheads leads to the fact that its super challenging and hard to get a feedback on existing submitted reports, or having a dialogue with triage teams, the situation today is usually leaving a comment and "praying" triage member will respond.
D. Mediations are completely dead - the significant number of submissions, often from new-comers could lead to mediation requests on none issues, the same queue today exists for paid programs mediations and points only programs, again - affecting the portion of researchers who actually contribute the most value to platforms, finding valid vulnerabilities on paid programs.
2. "Free Labor" / "Can only find bugs on VDPs"
The most obvious thing that comes to mind is the fact that people "work" for free helping multi-billion companies bolster their security, VDP's can be great training ground for new-comers, but the reality today is that >90% of the people who report to VDP programs do so solely to boost their reputation and platform standings because its easier to find bugs there, the programs don't care if you spam ~200 reports on same XSS on same Endpoint and you fake out parameters, and so on.
Think about it - if you managed to find XSS on a VDP via redirect_uri on login page, you most certainly could have found it on a BBP, but you missed it because you were focused on the VDP while the BBP introduced the issue.
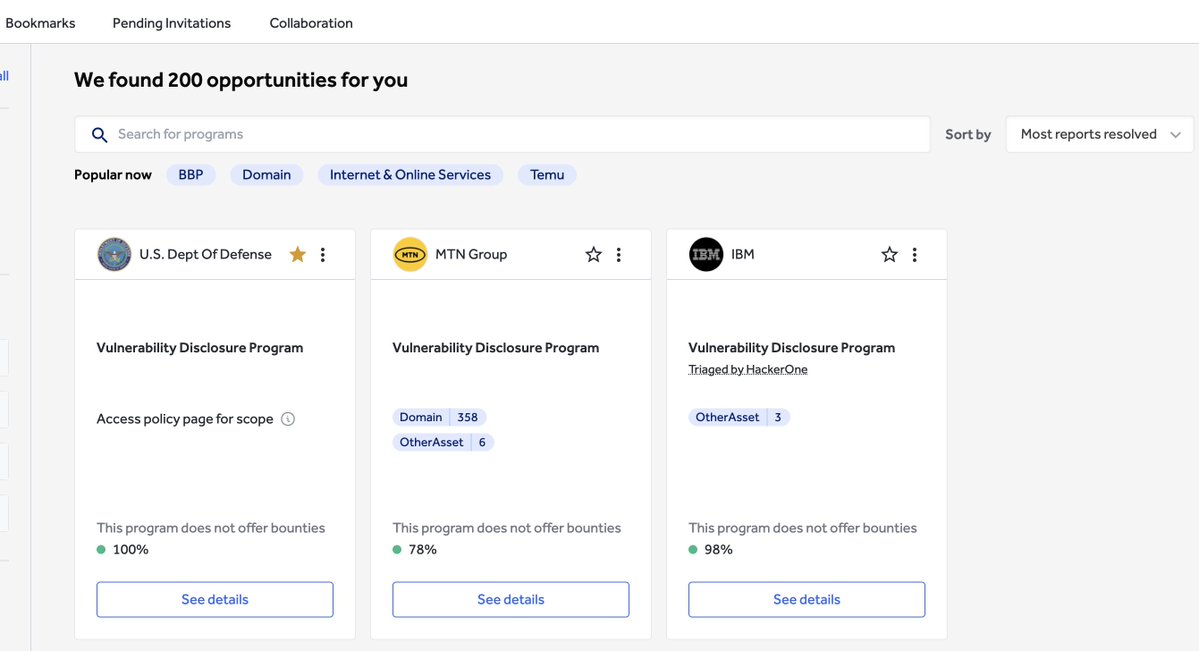
Today, there are ~200 VDPs on @Hacker0x01
133 VDPs on @Bugcrowd (I do like that they have completely separated view on the platform)
3. Leaderboards are not trust-worthy
#BugBounty is well gamified space, we all push ourselves the extra-mile to do well and beat our colleagues in the rankings, however VDP's made the state of public leaderboards so unstable and not trust-worthy that they are not even taken into context when determining "top hackers" for events invites, or so on.
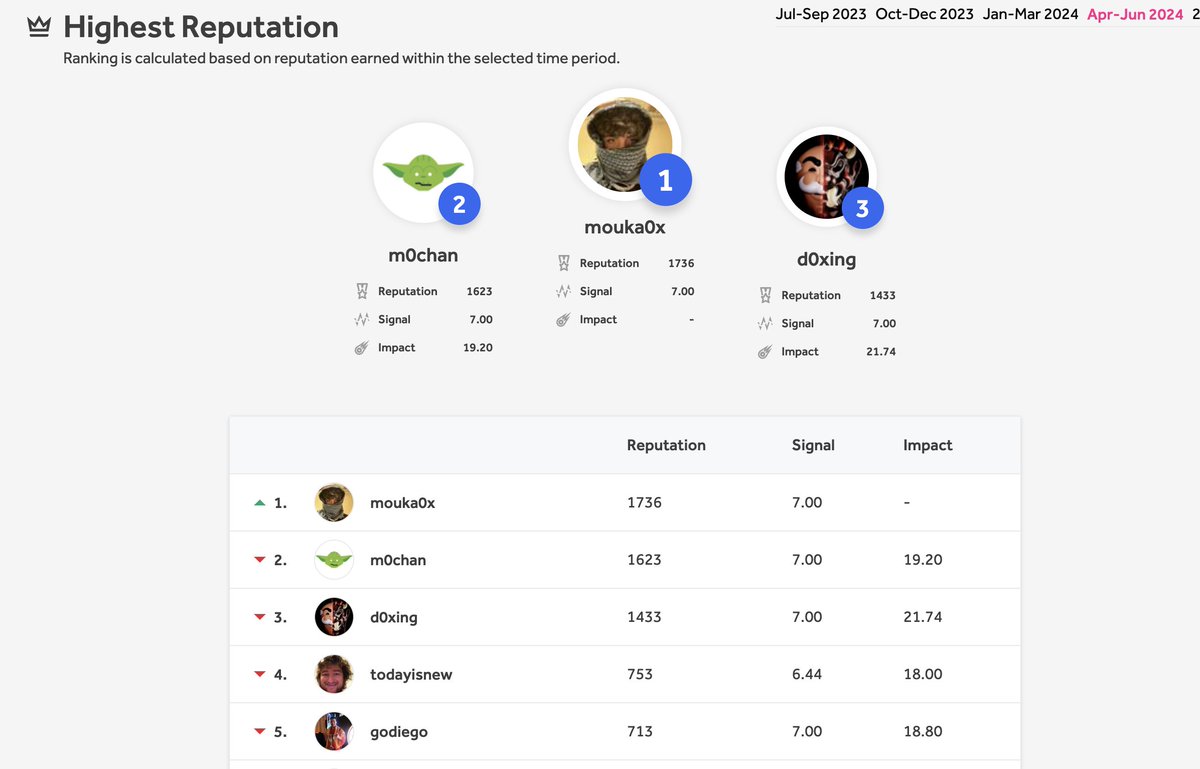
Within Q2 (Apr 1st to Apr 16th) we have 8 VDP-Only Hunters on HackerOne's Top 100 leaderboard, including the #1 hacker in the world.
While on the actual leaderboard you do gain some advantage if you hunt on BBPs, as you get some spare change of reputation points when you are awarded a bounty, the sub-leaderboards as "Highest Critical Reputation" do not distinguish between VDPs and BBPs at at all, it's straight 7 reputation points for any triaged High / Crit, whether a free one / one that got $200k bounty.
This means that in Q2 3 of the Top 5 Most Critical Hackers in the world are VDP-Only hackers, and ~20 out of the Top 100 on the 2024 Leaderboard.
Eventually, this leads to actually debating whether we should focus on VDPs to improve our rankings on platforms leaderboards.
4. "Same Scope VDP/BBP Scams"
The standardization of having public incentivized VDP accompanied to a private BBP is the worst thing you can do as a program.
A. Programs will tend to think that the "winning model" would be having main application in scope for private BBP, and have public VDP for all their "wildcards", that's a huge mistake if your company are actually looking in preventing their next breach, so many critical vulnerabilities that can cause to a complete incident in matter of minutes will remain unattended for weeks, no-one would bother to give you an actual time sensitive submission on a program without monetary rewards.
B. Sometimes, it's just straight up a scam - same scopes for both programs, researchers submit to VDP and lose on money.
Having an unincentivized responsible disclosure policy submission form on your website and a private BBP is more than okay, thats actually a perfect use-case, have your own set of researchers and accept in-coming reports as "see something - say something" from the crowd, I bet that if you'll find someone reporting super critical submission, It'll probably lead to a private program invite - unlike when having a "Points Reward" program on a platform already, that you feel the "award" was given already.
Solution 💡
Well, if you made it so far - there is a solution, and it's one that will make all parties happy.
The formula:
1. Remove VDP Points from platforms and Leaderboards.
2. VDP Contribution Recognition - Whenever a researcher submits a valid report to a VDP, display the company logo on his profile, and auto-generate a "Thank You" letter in which he could use in his CV.
3. Auto-Invite researchers who discover a valid bug on private BBP scope in a pubic VDP.
4. No Mediations on VDPs.
5. Sales pitches should specify that companies won't be getting time-sensitive issues on VDPs, pushing them to create BBPs.
6. Kill Private VDPs.
Going through the formula, VDP hunters will still receive valuable recognition for their VDP submissions, BBP hunters will enjoy a clean leaderboard who pushes for paid program submissions, Triage teams will go through way less overload, Mediations will start working again, Less VDP's => More BBP's because companies eventually want to be secured, more BBP's => More Money to platforms.
Disclaimer: everything I've wrote here is based on my thoughts and analysis.
Thoughts? Is there any advantage to any party for awarding points on VDP's? am I hallucinating?
#BugBounty


Israel 🇮🇱 English
d0xing retweetledi
d0xing retweetledi
d0xing retweetledi

Cache Poisoning at Scale:
Identifying and Exploiting over 70 Cache Poisoning Vulnerabilities
youst.in/posts/cache-po…
English

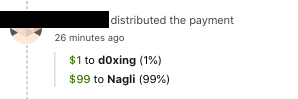
@naglinagli @Bugcrowd Collaboration FTW, thanks for paying my cheeseburger
English