Daaf.nl ⚓️ retweetledi
Daaf.nl ⚓️
2.8K posts

Daaf.nl ⚓️ retweetledi

A user reports a suspicious email. Your SOC resets the password and revokes the session. Ticket closed.
The attacker re-authenticates the next morning using the MFA method they registered during the 30 minutes they had access.
This is the most common failure pattern in M365 identity compromise response. Teams jump to containment before they've enumerated persistence. A password reset removes the original access method while leaving everything the attacker built during their session — new MFA methods, OAuth applications, registered devices, and mailbox forwarding rules.
Every one of those survives a password reset. Everyone survives a session revocation.
We wrote a step-by-step investigation sequence for M365 identity compromise that most SOC playbooks get wrong:
Step 1: Identify the compromise sign-in — how they got in and why your controls allowed it
Step 2: Map post-compromise activity — what they did with the access
Step 3: Enumerate every persistence mechanism — MFA, OAuth, devices, mailbox rules
Step 4: Contain in the right order — revoke persistence BEFORE resetting the password
The post includes the KQL queries for each step, a persistence comparison table showing what survives password resets, and a baseline query you should run on your tenant right now — before the next alert fires.

English
Daaf.nl ⚓️ retweetledi

🔒 Secure Bits 💡
𝗕𝗿𝗲𝗮𝗸-𝗴𝗹𝗮𝘀𝘀 𝗮𝗰𝗰𝗼𝘂𝗻𝘁𝘀: 𝗳𝘂𝗹𝗹 𝗴𝘂𝗶𝗱𝗲 (𝗣𝗗𝗙)
In my last post I talked about the “worst day” scenario: CA misconfig → admins locked out. Most orgs think they’re covered… until they test it.
As promised, 𝗵𝗲𝗿𝗲’𝘀 𝘁𝗵𝗲 𝗳𝘂𝗹𝗹 𝗣𝗗𝗙 𝗴𝘂𝗶𝗱𝗲 that walks you through a practical break-glass setup:
▪️ Naming
▪️ Permissions
▪️ Role-Assignable Security Group
▪️ Custom Break-glass Administrator role (Optional)
▪️ Restricted Management Administrative Unit (RMAU)
▪️ Authentication Methods
▪️ Conditional Access Configuration
▪️ Monitoring & Alerting
▪️ Operational Procedures
📎 Download the PDF here:
academy.horizon-secured.com/p/m365-securit…
𝘈𝘶𝘵𝘩𝘰𝘳: Martin Strnad
💬 When was the last time you tested your break-glass access?
#EntraID #IdentitySecurity #ConditionalAccess #SecureBits #HorizonSecured




English
Daaf.nl ⚓️ retweetledi

23 deep dives. Every E7 admin component. How it works, demoed by the people who build it. One playlist, all the answers: youtube.com/playlist?list=…
English
Daaf.nl ⚓️ retweetledi

Plug a $30 USB stick into your laptop and you can listen to satellites, decode pager traffic, intercept walkie-talkies, and watch TV signals fall out of the air around you.
Free. No license. No subscription.
Just one tool nobody outside the radio underground talks about.
It's called SigDigger. An open source digital signal analyzer that turns a cheap SDR dongle into a full radio intelligence rig.
Here is what it can actually do.
Point it at the sky and you can pull down NOAA weather satellite images as they pass overhead. Tune it to your local airport and you can decode aircraft transponders in real time. Sweep the FM band and you can demodulate analog voice the moment it hits the antenna.
The interface looks like a Bloomberg Terminal for the airwaves.
A live waterfall display showing every signal in your area. PSK, FSK, and ASK demodulation. Burst signal analysis for the weird short transmissions nobody can identify. Analog video decoding. Panoramic spectrum sweeping across entire frequency ranges.
All running on a Linux or macOS laptop with zero specialized hardware.
What used to require a $40,000 spectrum analyzer locked inside a defense lab now runs in your living room for the price of a USB stick.
The author built the entire DSP backend from scratch instead of leaning on GNU Radio. He wrote his own core library called Suscan, his own signal processing library called Sigutils, and his own widget library called SuWidgets. Faster. Cleaner. Optimized for the exact tasks reverse engineers and amateur radio operators actually need.
Plugin support is built in. AmateurDSN for deep space network monitoring. APTPlugin for weather satellites. AntSDRPlugin for the AntSDR hardware. ZeroMQPlugin for piping signal data into other tools. Everything snaps in with one command.
The whole stack supports SoapySDR, which means almost every SDR device on the market works out of the box. RTL-SDR. HackRF. LimeSDR. Airspy. Plug it in and start digging.
1.5K stars. LGPL-3.0. 100% Opensource.

English
Daaf.nl ⚓️ retweetledi

Service accounts are prime targets for attackers. Some advice on protecting them…
1. Use Managed Service Accounts - this is as close to an easy button as you can get
2. Rotate passwords strategically - what I mean here is, if you don’t need to rotate the password, don’t. Unless you suspect compromise or the password has been leaked or used elsewhere.
3. Monitor for abnormalities - Monitor for suspicious logins like when the account authenticates outside of typical time windows or when it’s used on hosts it doesn’t typically login to.
One last bonus tip is to document where your service accounts are being used and its purpose.
One of the worst issues I’ve seen is when a service account password is updated and one location the account is used gets missed, brining production systems or applications down. That’s no fun (:
English
Daaf.nl ⚓️ retweetledi

Microsoft now lets admins choose pre-installed Store apps to uninstall
bleepingcomputer.com/news/microsoft…
bleepingcomputer.com/news/microsoft…
English
Daaf.nl ⚓️ retweetledi

📢 New blog post: Blocking Bring Your Own Copilot (BYOC)
Users can use personal Copilot plans on work documents by default in M365, unless you block it.
Here’s what it means & how to disable it in Intune.
🔗 welkasworld.com/post/blocking-…
#M365 #Copilot #DataProtection #ShadowAI
English
Daaf.nl ⚓️ retweetledi

Tomorrow's the day! 👀
Secure Boot cert changes are coming, and most environments aren’t as covered as they think.
No alerts. No failures. Just hidden gaps.
If you can’t prove you’re covered, that’s your signal.
Join us 👉 bit.ly/4sHDU6y
#MSIntune #ConfigMgr #EndpointManagement
English
Daaf.nl ⚓️ retweetledi

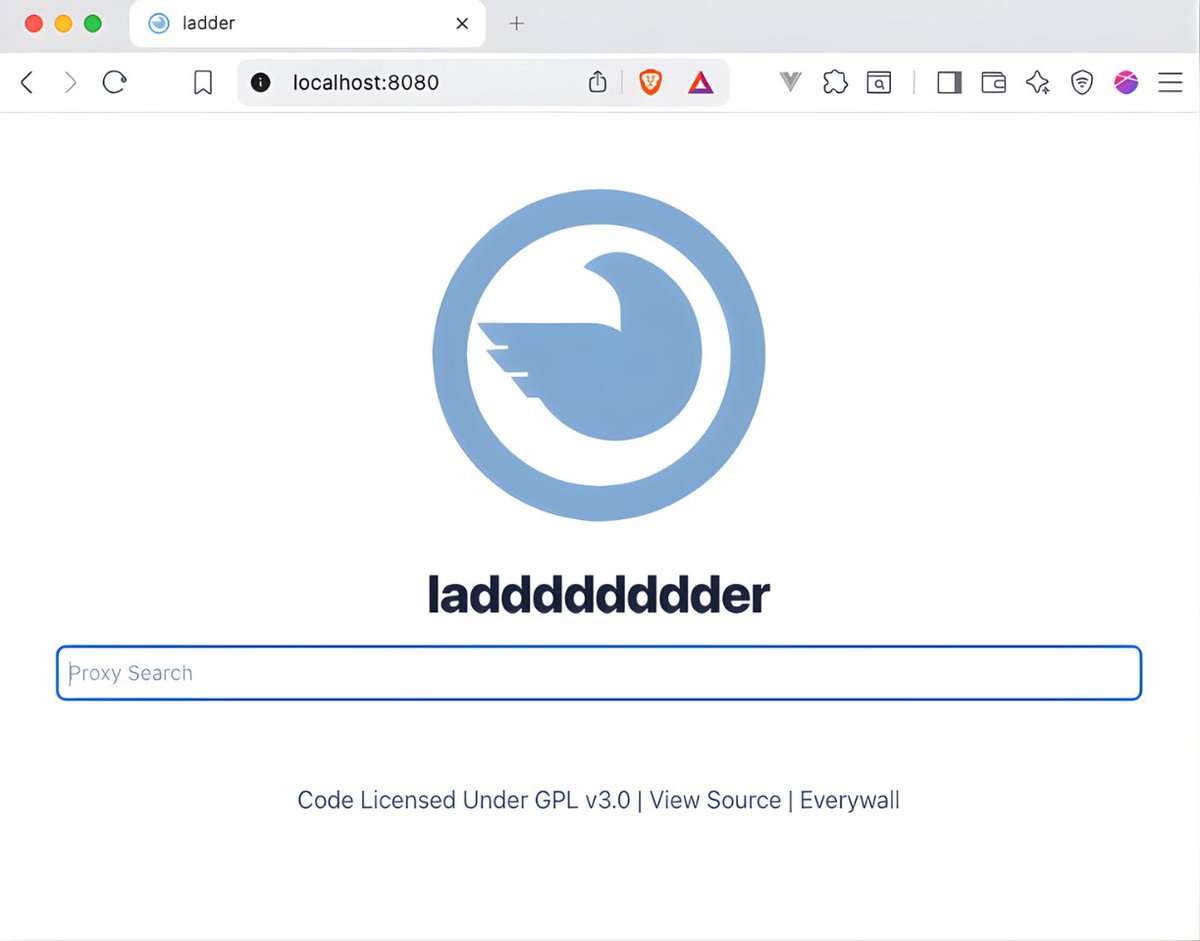
The New York Times charges $17/month.
The Wall Street Journal charges $38/month.
Nature charges $199/year.
Someone just open sourced a proxy that bypasses all of them for $0. And publishers cannot shut it down.
It's called Ladder.
Here's the trick that makes it work:
Every news site and academic journal on earth shows Google the full article text for free. They have no choice. Block Googlebot and you disappear from search results overnight.
Ladder pretends to be Googlebot.
Same headers. Same fingerprint. Same access Google gets.
→ Paste any paywalled URL
→ Full article loads instantly
→ No account. No subscription. No credit card.
→ Works on NYT, WSJ, Bloomberg, Nature, Science, The Lancet, The Atlantic, and hundreds more
→ Also strips CORS headers from any URL, which saves developers a stupid amount of time
Publishers got 12ft killed by pressuring the domain registrar.
Ladder runs on your own server. There's no domain to seize. No company to pressure. No central server to shut down.
One Docker command. Your machine. Your rules.
6.3K stars. MIT License. 100% Opensource - github.com/everywall/ladd…
English
Daaf.nl ⚓️ retweetledi

Copilot, Agent 365, Entra Suite, and E5 security unified in one subscription. Watch deep dives into how each E7 component works in our playlist: youtube.com/playlist?list=…
English
Daaf.nl ⚓️ retweetledi

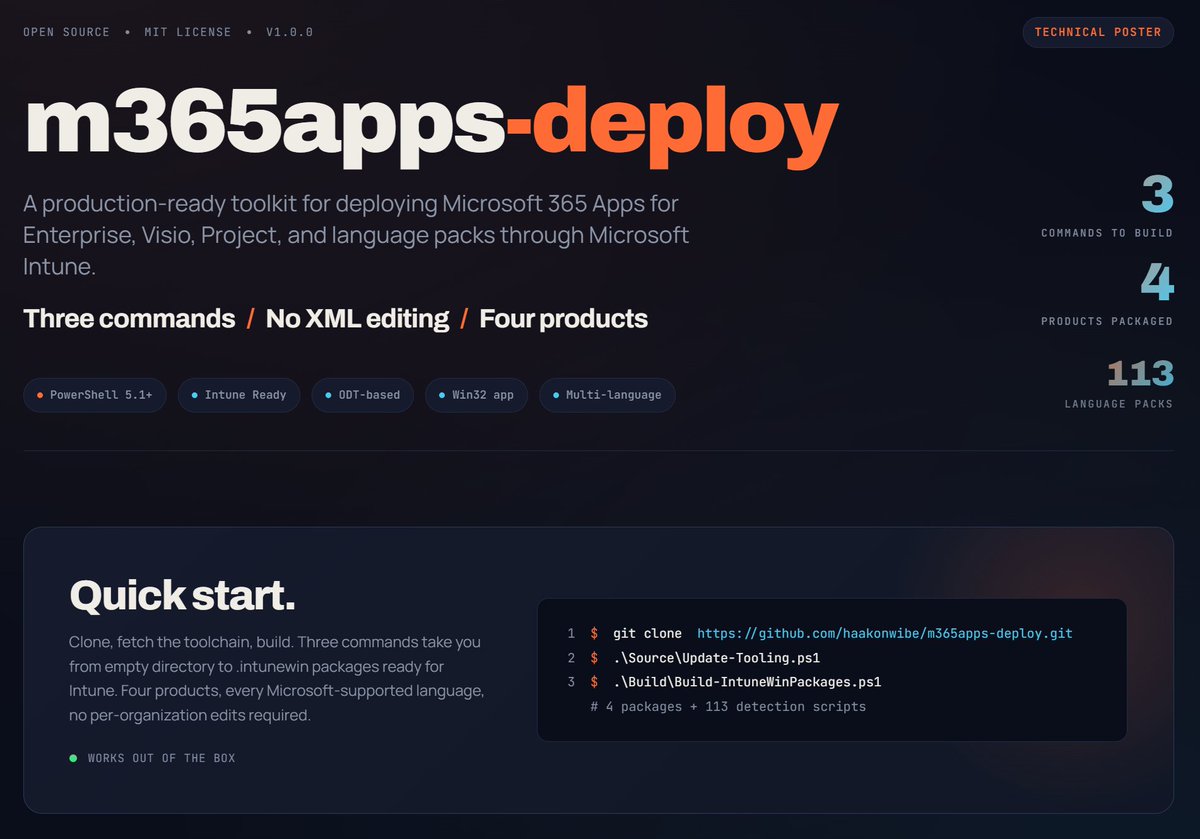
Every Intune admin has lost an afternoon to an M365 Apps + Visio + Project + language pack deployment that "almost" worked. Got tired of that, built a toolkit so my team doesn't have to. Three commands to get going, four products covered, 113 language packs for those counting, install/uninstall whatever order you like. github.com/haakonwibe/m36…
English
Daaf.nl ⚓️ retweetledi

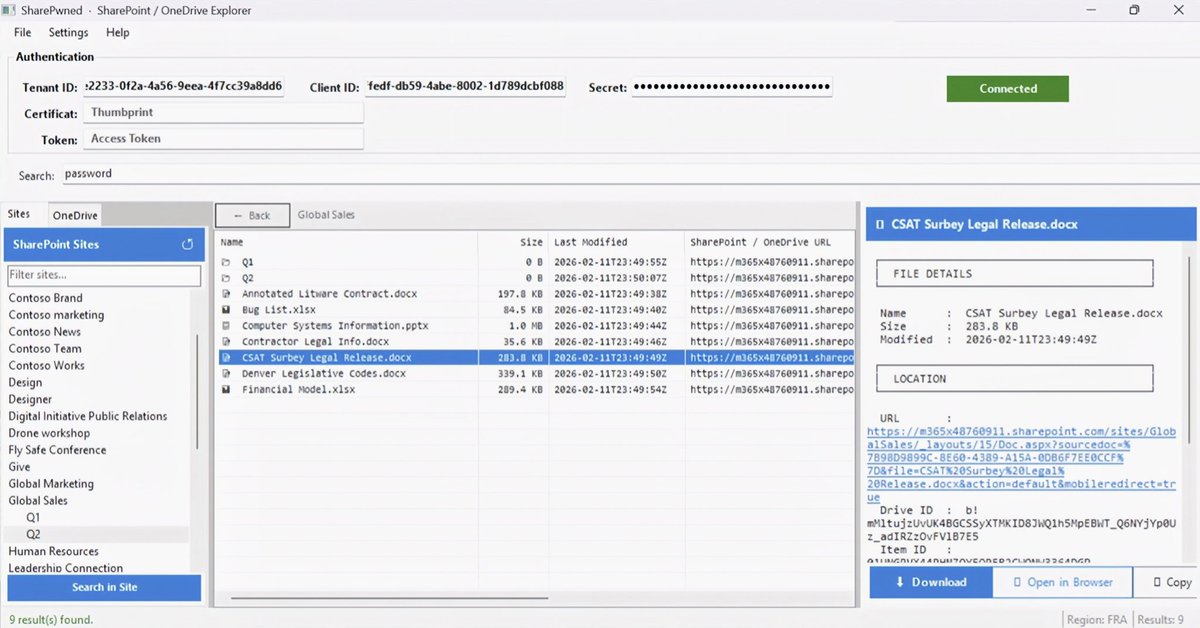
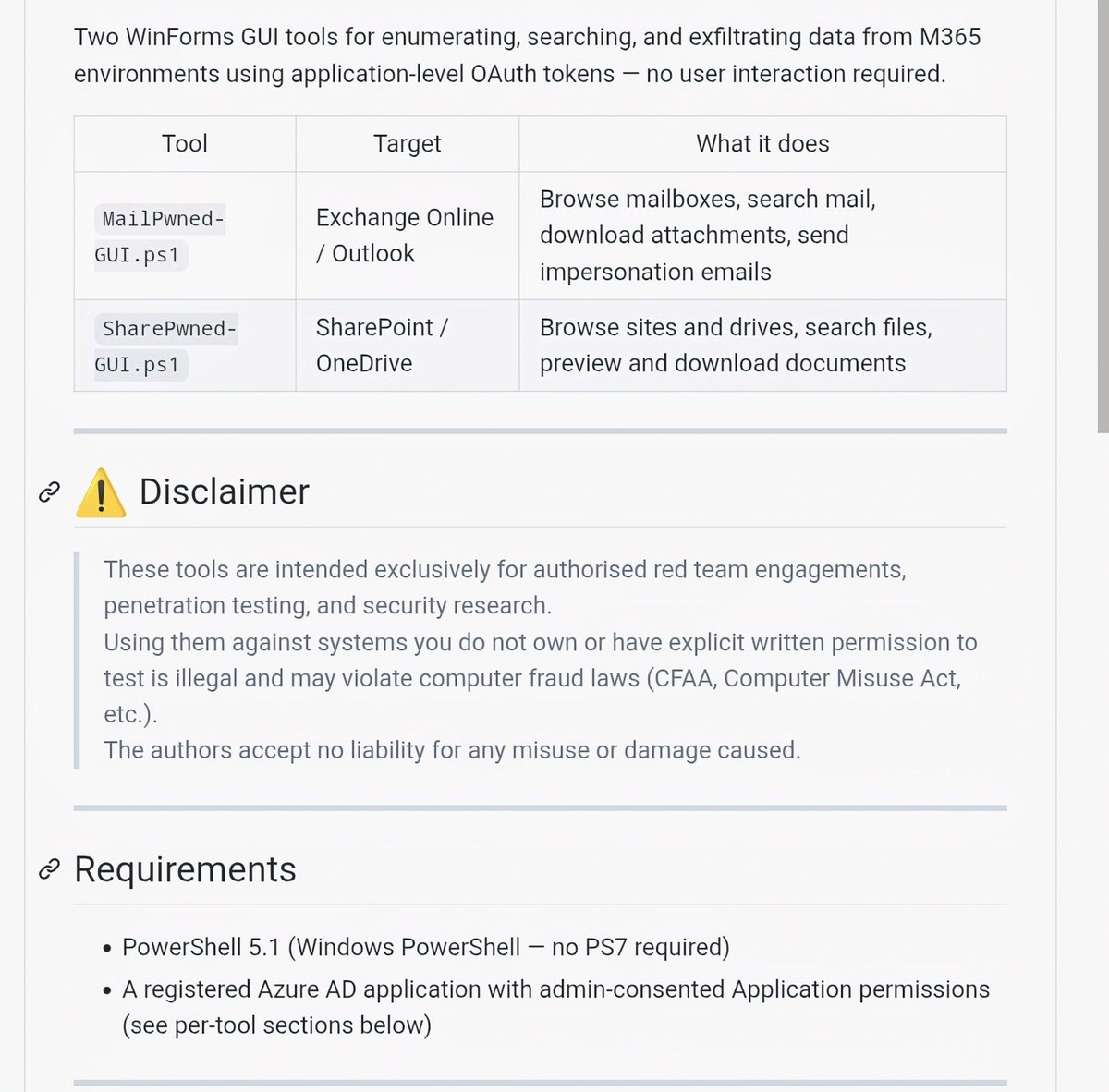
M365Pwned: Red Team Tooling for Microsoft 365 Exploitation via Microsoft Graph API 🔐💀
Browse mailboxes, search emails, download attachments & send impersonation emails
Access SharePoint & OneDrive data across the tenant with OAuth tokens
github.com/OtterHacker/M3…
#RedTeam #M365 #CyberSecurity #Pentesting


English
Daaf.nl ⚓️ retweetledi
Daaf.nl ⚓️ retweetledi

Daaf.nl ⚓️ retweetledi

V2 of the #Kali365 PhaaS toolkit has emerged with dedicated OAuth and AI-based lure generation, seeing widespread abuse. This kit is distributed via Telegram and has features like a domain marketplace, Cloudflare worker hosting and keyword searching: bit.ly/3QupSXM


English
Daaf.nl ⚓️ retweetledi
Daaf.nl ⚓️ retweetledi
Daaf.nl ⚓️ retweetledi

OAuth consent phishing is the #M365 attack most orgs still aren’t watching.
No password stolen.
No MFA bypassed.
Just one “Sign in with Microsoft → Approve” click.
Malicious app gets a refresh token with persistent access to mail, files & calendar. Bypasses Conditional Access. Logs look normal. Default detections miss it.
Fix: Monitor Entra audit logs for “Consent to application”. Alert on risky scopes (Mail.Read, Files.ReadWrite.All, offline_access) from unverified publishers.
Better: Disable user consent entirely. Force admin approval only, where practical.
This is the gap between “we have MFA” and real security. M365/SecOps pros: auditing your consents right now!

English
Daaf.nl ⚓️ retweetledi

Microsoft: Some Teams users can’t join meetings after Edge update
bleepingcomputer.com/news/microsoft…
bleepingcomputer.com/news/microsoft…
English