Daniel Schell
1.5K posts

Daniel Schell
@danonit
CoFounder & CTO at @AirlockDigital. Practical Execution Control & Allowlisting.



Happy Saturday! Exposed attack surface on the internet has been shifting from legacy appliances and Windows boxes directly on the internet into cloud for years now (Thanks Citrix, Fortinet, MoveIt, etc). The excitement around LLMs findin vulnerabilities and the incoming apocalypse is legitimate, however directly exposed attack surface has been decreasing(Thanks App proxy, zscaler, etc) and now you have more eyes on what was already a shrinking target. Bugs found on the cloud side have a shorter life and once identified, generally patched for everyone at once. Down the line from that you can certainly use LLMs to go after endpoint bugs in Microsoft where you generally lack source and it requires a higher level of human directed iteration, on top of dealing with EDR/AV if your target is enterprise. No doubt people can iterate faster and find more bugs, I've found a ton of these personally, but many bugs have limited to no real world impact. Configurations you won't see in the wild, code paths you can't reach without auth you don't have, features that are off by default. Overlooked in all of this is the ease at which you can reverse and dismantle security products, many of which are forced into design choices by the OS, or into exclusions to avoid drowning clients in false positives. Things like extracting the local ML models from products isn't a big leap these days. It certainly makes the case for application control being a bigger priority going forward, even if it doesn't make for a great funding pitch.











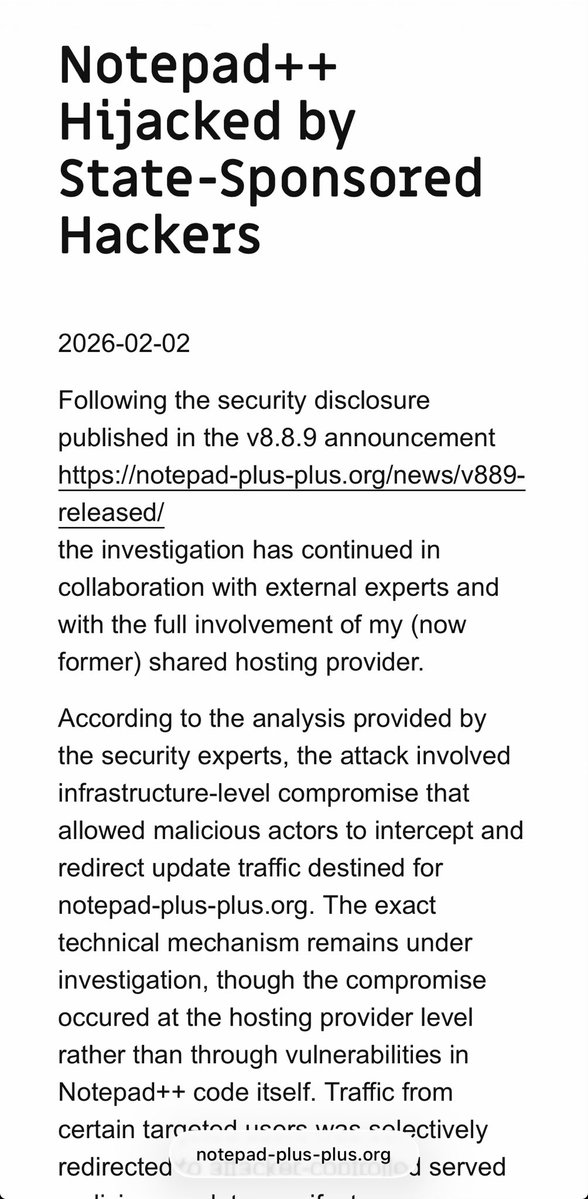
@arekfurt It’s been high risk for a while since the author rallied against proper code signing for a while, switching to self-signed and has come around again now. It’s a great product and free, but yeah…


Notepad++ Hijacked by State-Sponsored Hackers | Notepad++ notepad-plus-plus.org/news/hijacked-…


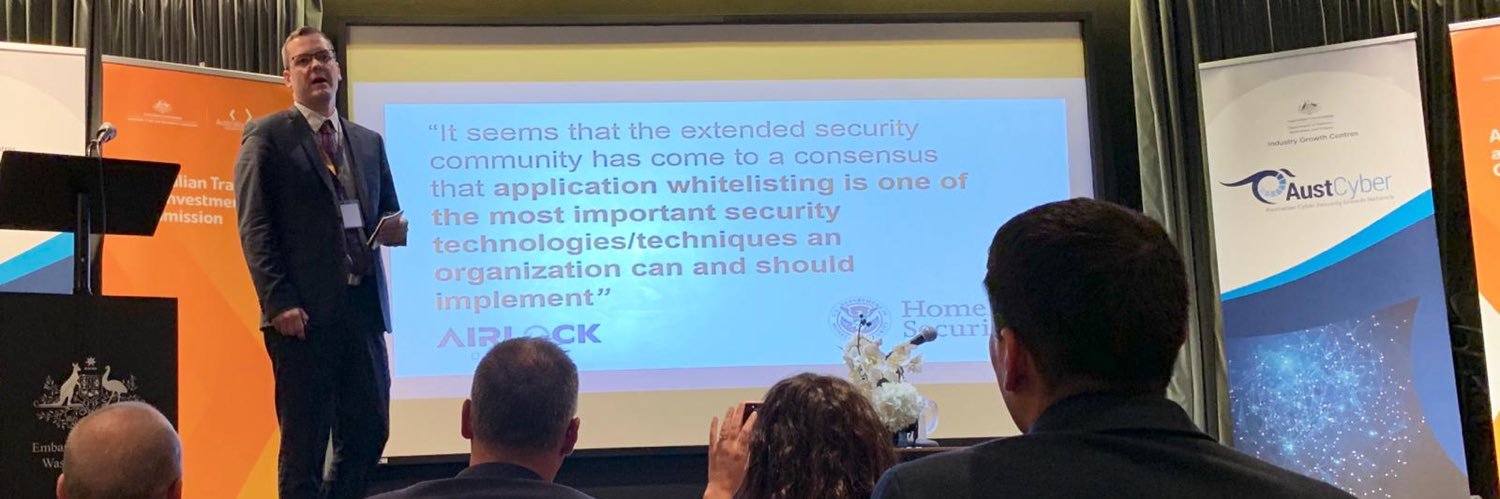
Application control works, I don't think there's many who debate that. But part of the reason it gets a bad reputation is because of flawed deployments. Here's a few things to avoid: 1. Overly permissive path rules (e.g. wildcard paths) 2. Overly permissive publisher rules (e.g. everything from a publisher is allowed) 3. Using only hash rules 4. Allowing CMD/PowerShell/PowerShell_ISE/Terminal



One of the most consistently achievable ways to secure your org is to eliminate unnecessary attack surface You don't have to patch it if it doesn't exist