Debug Majora
102 posts


Debug Majora
@debug_majora
Threat Intel, macOS based threats, and cats. Check out my blog! https://t.co/Cm0LoV3KtX
Katılım Ağustos 2021
361 Takip Edilen26 Takipçiler

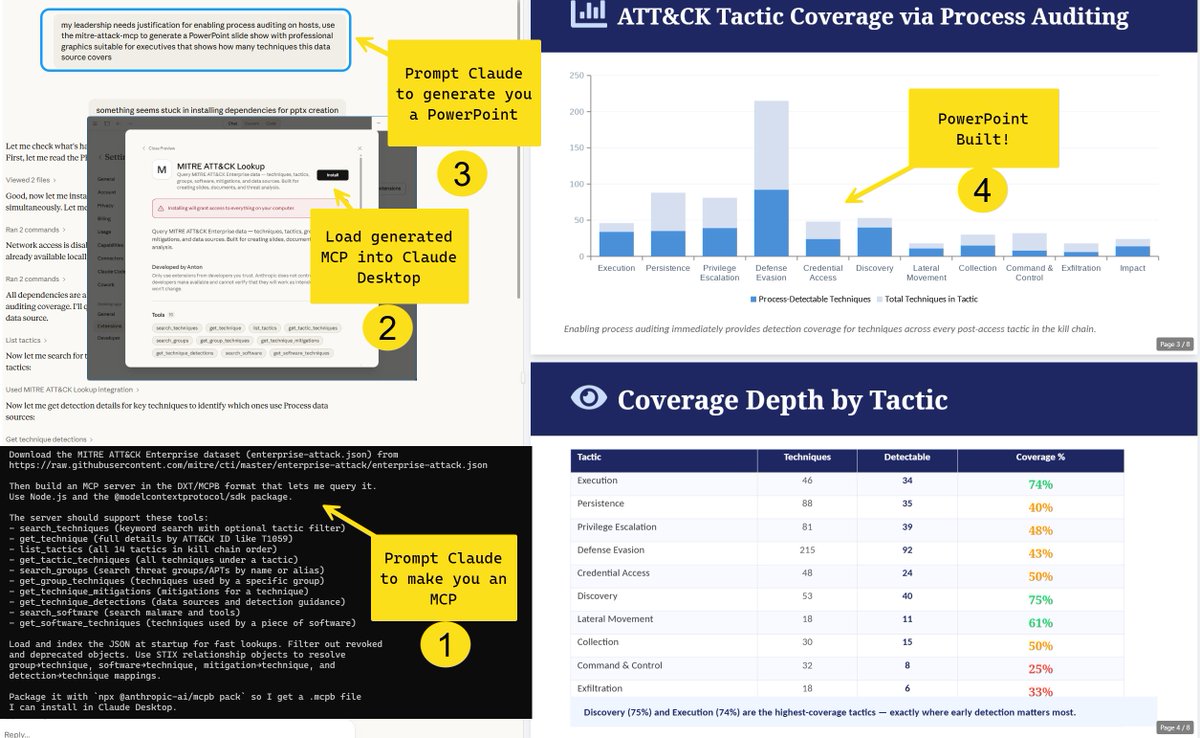
Day 2 of #ClaudeForBlueTeam
Building visuals and presentations using ATT&CK can be a pain.
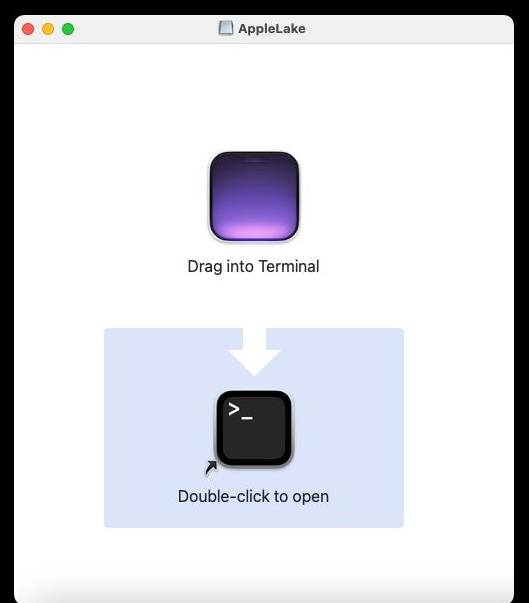
Prompt Claude to build an ATT&CK MCP for you - then load this ATT&CK MCP in Claude Desktop.
Now you can ask Claude to generate executive briefings for you, using rich ATT&CK data.
English

@fr0gger_ great read 🙏🏼
I created something similar for Compromised Credentials (querying individual API’s -> aggregating the results -> a final verdict is provided) but your approach introduces some improvements I could introduce
English


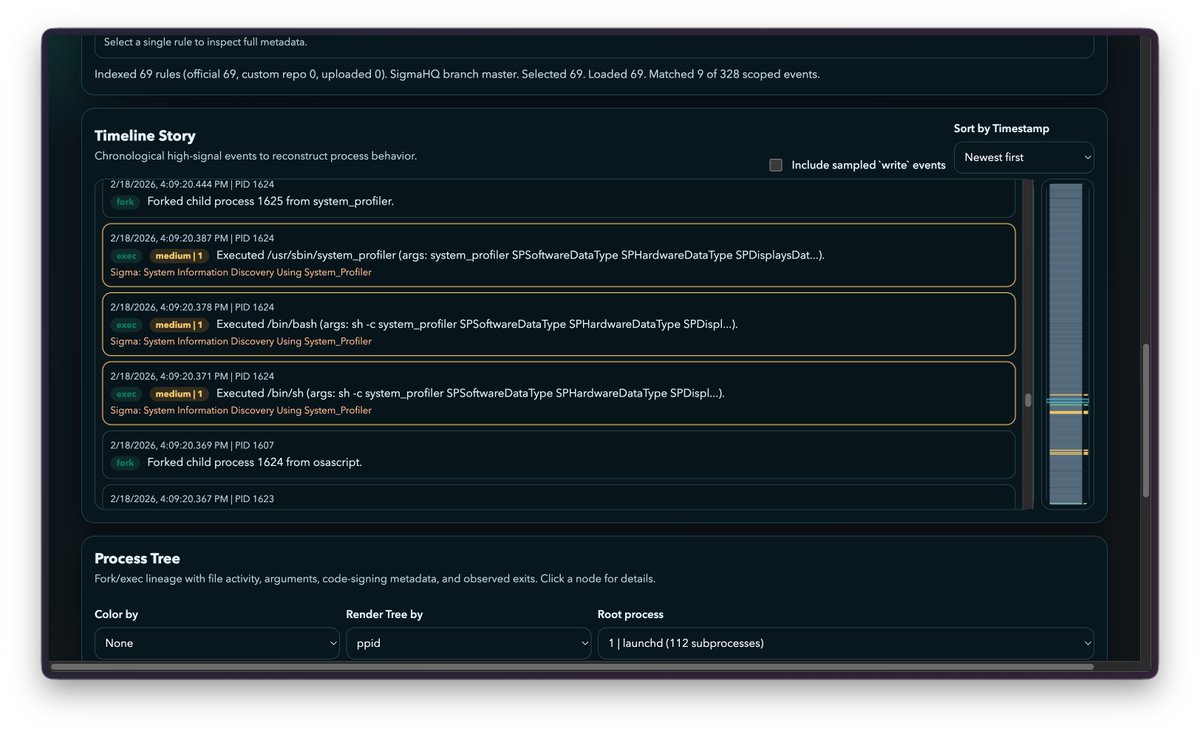
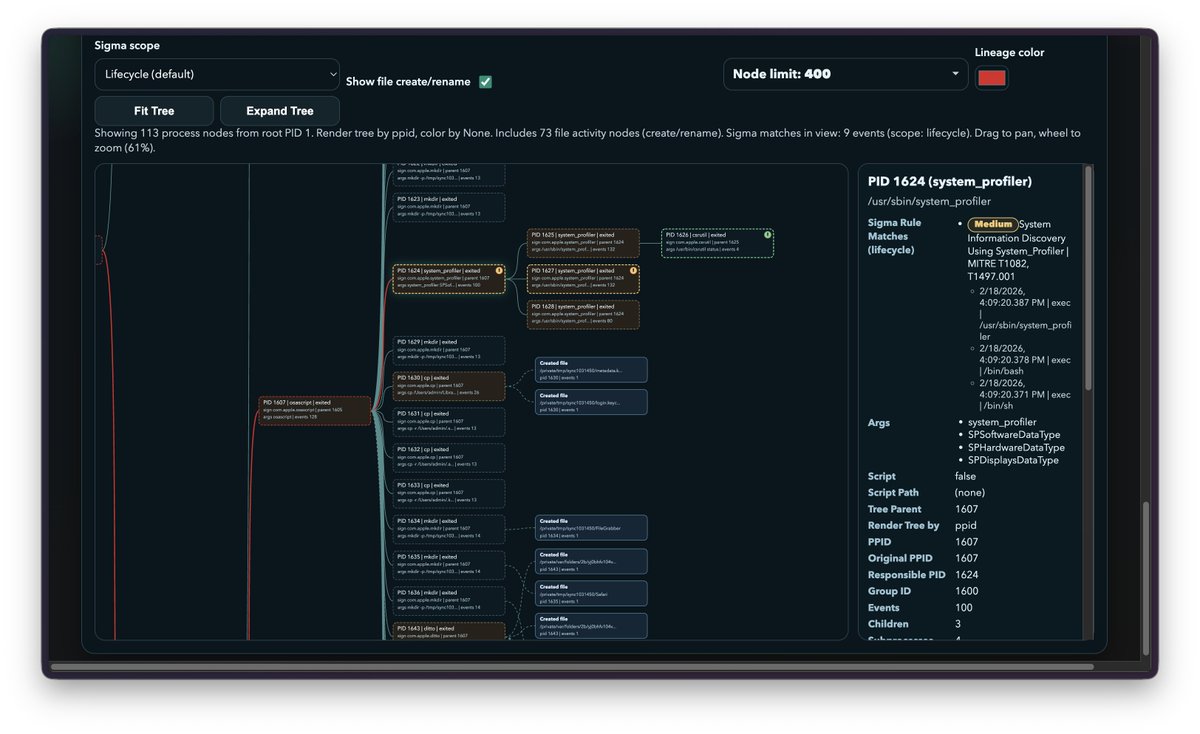
Is ESLogger or Mac Monitor your friend for dynamic malware analysis on macOS? Then i've got something that might come to use!
An browser based ES/Mac Monitor log analyzer with a lot of neat features like story timelines, Sigma rule matching, an in-depth process tree analyzer and much more and the neat thing is, nothing is uploaded to any backend!
I'm looking for feedback!
Take a look at es.decompiler.dev
#macos #malware #reverseengineering #re #ThreatHunting #dfir


English

@Gootloader @GoogleAds Ah I see. I remember working a case where we tracked the threat actors malvertising campaign via their advertiser profile/email (aka the profile they were using to serve their malicious ads). Not sure if that helps
English

Anyone have a good way to monitor new @GoogleAds for a specific domain?
English

@GamingWithNep @PJ_Marcum agreed - not seeing the correlation either lol
English

@PJ_Marcum This was a typosquatted domain that was weaponized. Not sure if this is a bait post. This has been going on since the beginning of time.
English

First Notepad++ and now 7-zip. This shows why we need to limit apps installed on corporate devices to only things with a valid business justification.
Malwarebytes@Malwarebytes
A fake 7-Zip site has been quietly spreading a trojanized installer that turns victims’ machines into proxy nodes. bit.ly/4r7Joa7
English

@txhaflaire @malwrhunterteam thank you!
and cheers I see one pointing to applelake[.]io/assets/files/AppleLake.dmg that i just grabbed
#summary" target="_blank" rel="nofollow noopener">urlscan.io/result/019bf0b…
English

@txhaflaire @malwrhunterteam wrote a small blog on this updated campaign - seems to be spreading via Youtube ads/videos
debug-majora.github.io/digitstealer/2…
English

@malwrhunterteam Digitstealer, most likely retrieved from applelake[.].org, the download is there provided through Dropbox.
English

@cyb3rops @nextronsystems this the way. Santa (aka now @northpolesec) does a great job at managing/implementing this for macOS.
English

At @nextronsystems we treat all RMM/remote tools the same - equally suspicious. We flag them all and let the analyst decide. They get a higher score when they’ve been renamed or found in an unexpected location.
rustdesk@rustdesk
I'm happy to see that @ESET has marked RustDesk as a PUA, but the problem is: why aren't @AnyDesk and @TeamViewer marked the same way? Aren't they also remote access software?
English

@banthisguy9349 sounds very similar to SpyClouds Investigations Portal/service. Even the same name lol
English

@Enderman @rawsalerts for marketing purposes only, srs lol. Companies create distinct monikers for said threat actor which helps drive traffic to them (in this case Salt Typhoon which was coined by Microsoft)
English

🚨#BREAKING: Chinese hackers linked to the group known as Salt Typhoon have breached the email systems of U.S. congressional committee staff, gaining access to internal communications.
English

@tuckner GreyNoise keeping their tradition going of proving quality community tools
English