Devarotech
248 posts


Devarotech
@devarotech
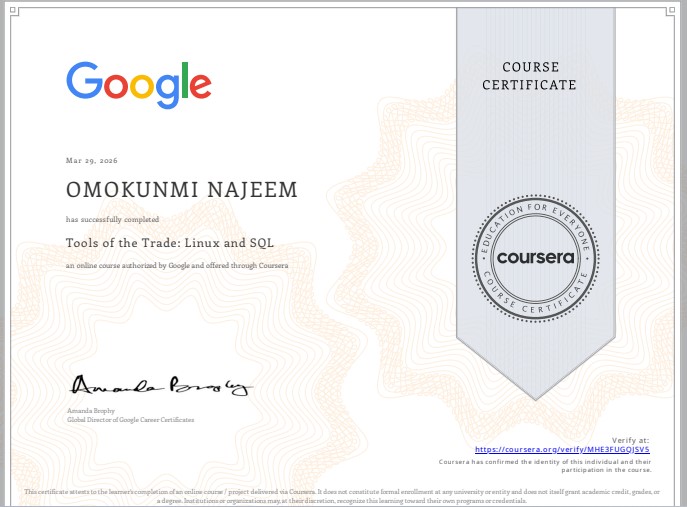
Cybersecurity learner | Google Cybersecurity & IBM track Python for automation | Ethical hacking in progress Building skills daily 🚀









#Day86 of hacking with @tryhackme DAy82 #100DAysOfCyberSecurity #RedTeamer @segoslavia @ireteeh @cyberjeremiah @jay_hunts I just completed AV Evasion: Shellcode room on TryHackMe! Learn shellcode encoding, packing, binders, and crypters. tryhackme.com/room/avevasion… #tryhackme via @tryhackme
















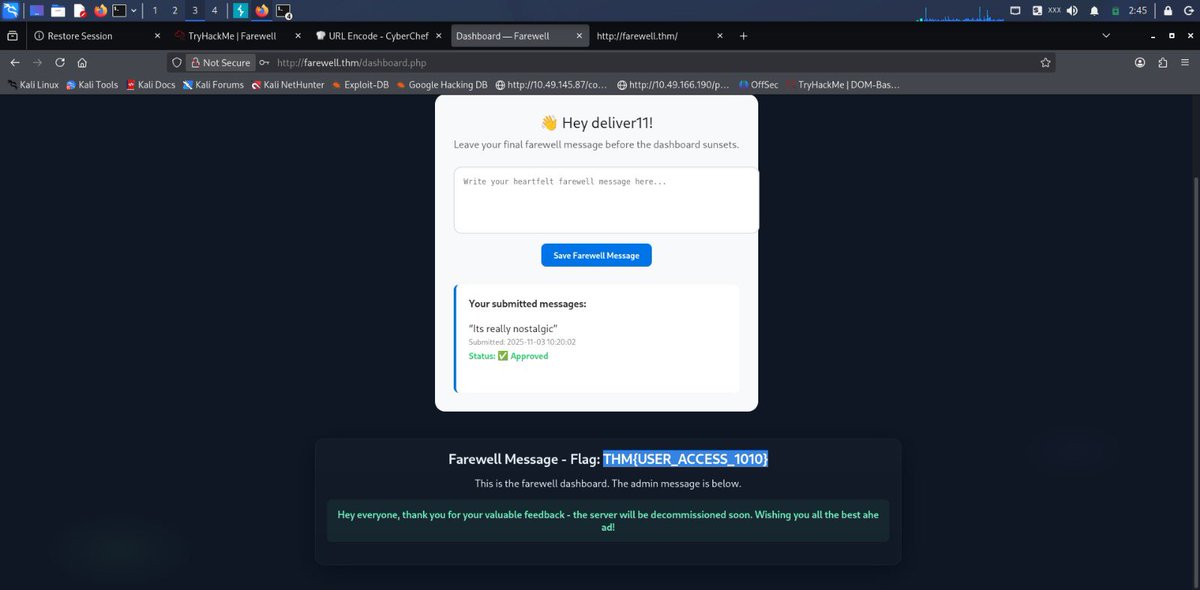
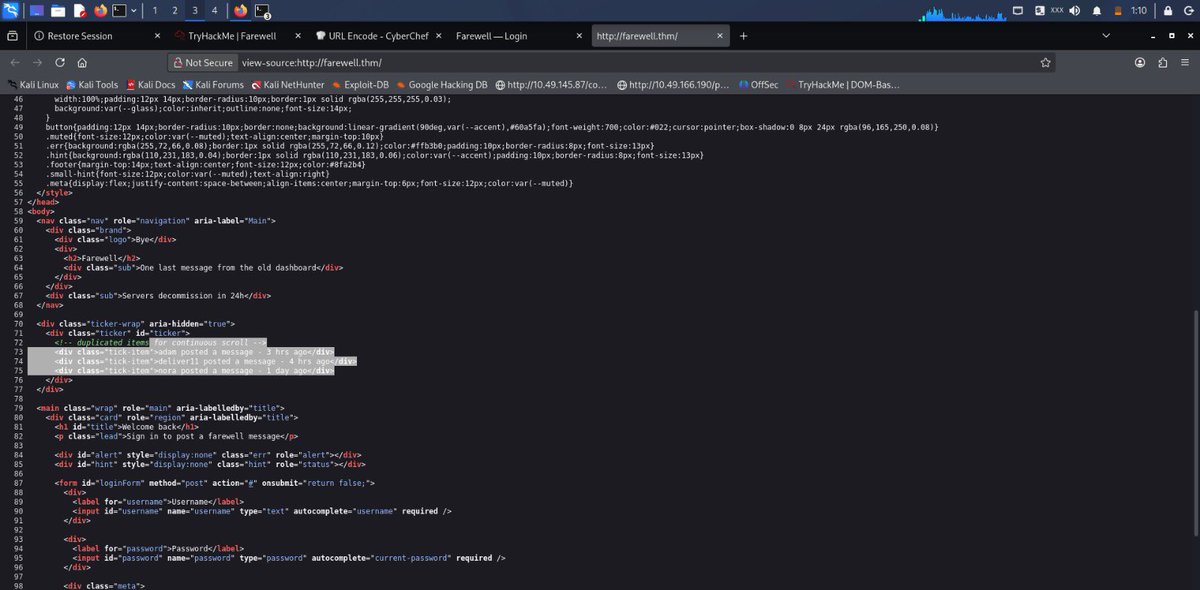
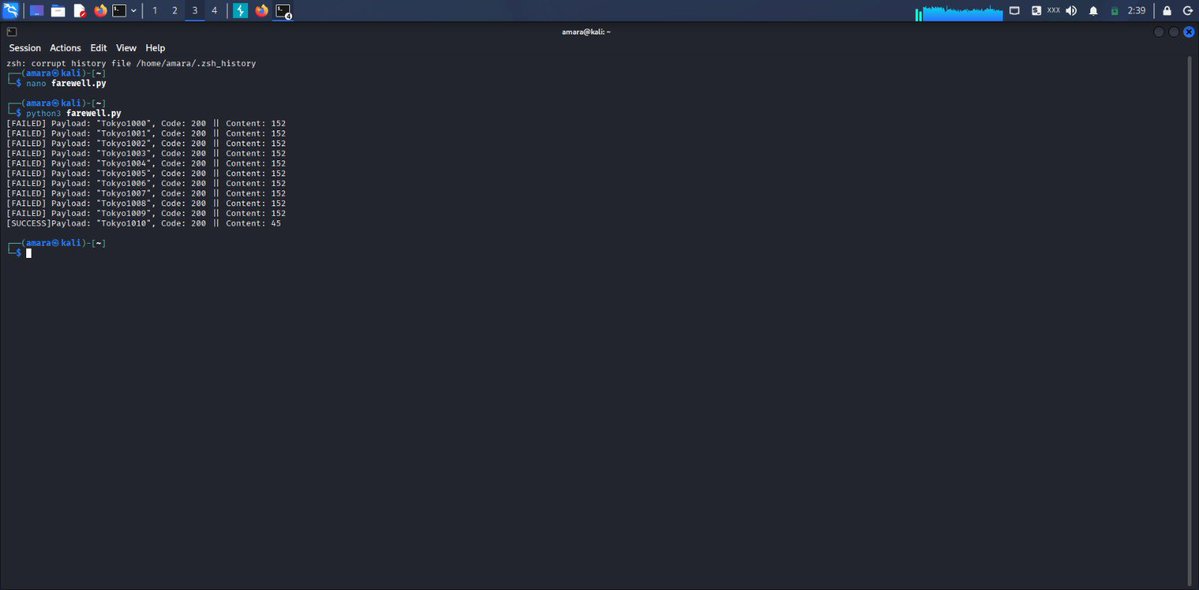
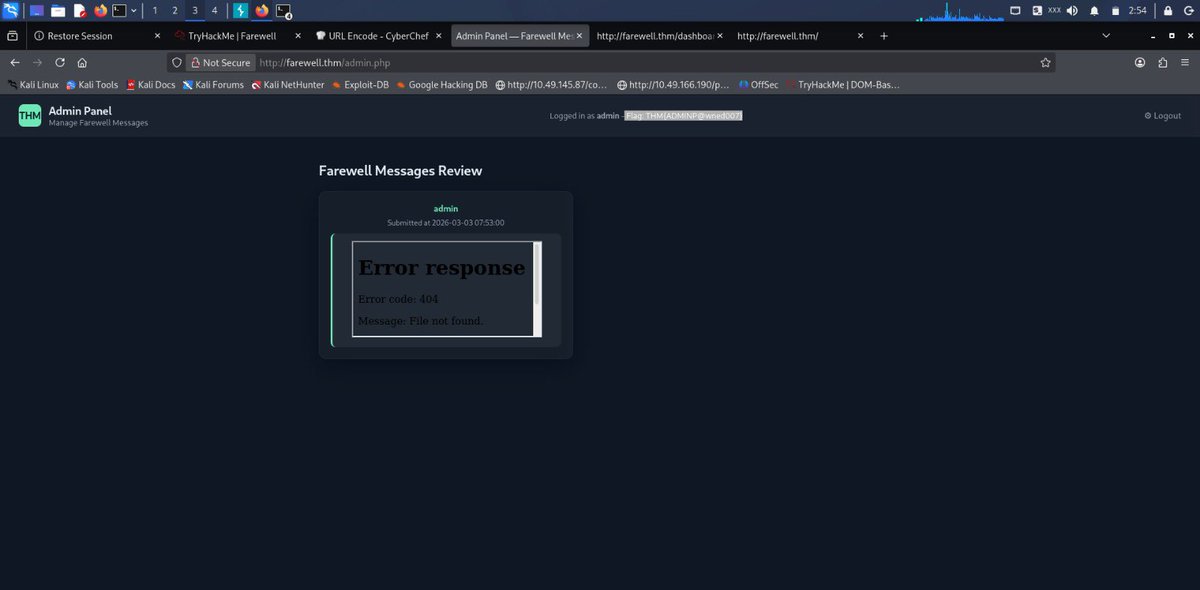
Day58 #100DaysOfCyberSecurity #RedTeamer Worked on the Padelify room on @TryHackMe today. It was fun and definitely challenging. Here’s a quick summary of the process👇👇 The lab was hosted behind a Web Application Firewall (WAF), so the first challenge was figuring out a way to bypass it and make my way to the moderator and eventually the admin page. I started with normal Nmap and Gobuster enumeration. While digging around, I accessed the error log page and noticed previous payloads submitted by other attackers. That was the turning point. It confirmed that anything submitted through index.php would later be viewed by the moderator, meaning the browser would process whatever payload was injected. Leveraging on that, I deployed an XSS payload which allowed me to steal the moderator’s cookies, log in as the moderator, and retrieve the moderator’s flag. To obtain the admin flag, I then exploited a Local File Inclusion (LFI) vulnerability. Using an encoded payload, the admin password was exposed. I logged into the admin panel and retrieved the admin’s flag. Vulnerabilities involved: •Cross-Site Scripting (XSS) •Local File Inclusion (LFI) •Weak WAF configuration •Poor input validation •Improper access control Another reminder that a weak firewall can fail. Documentation in progress ! @segoslavia @ireteeh @TemitopeSobulo @cyberjeremiah @jay_hunts