dhn
281 posts

dhn
@dhn_
By the power of truth, I, while living, have conquered the universe - /OS(C(P|E)|EE)/ - Tweets are my own! - Red teamer @codewhitesec | @[email protected]
0x41424344 Katılım Nisan 2009
328 Takip Edilen740 Takipçiler
dhn retweetledi

You like technical deep dives into binary exploitation and crazy heap wizardry? Then you'll like our blog post by @0xor_solo about unauth'ed RCE in NetSupport Manager aka CVE-2025-34164 & CVE-2025-34165 code-white.com/blog/2026-01-n…
English
dhn retweetledi

Our 2024 applicants challenge is officially #roasted: the full BeanBeat × Maultaschenfabrikle walkthrough is now online. Unwrap the write-up at apply-if-you-can.com/walkthrough/20… and revisit the hacks that escalated from cold brew to full breach.
English
dhn retweetledi
dhn retweetledi

Latest ≠ Greatest? A Retrospective Analysis of CVE-2025-59287 in Microsoft WSUS from our very own @mwulftange who loves converting n-days to 0-days code-white.com/blog/wsus-cve-…
English
dhn retweetledi

CODE WHITE proudly presents #ULMageddon which is our newest applicants challenge at apply-if-you-can.com packaged as a metal festival. Have fun 🤘 and #applyIfYouCan

English
dhn retweetledi

Ten days left. The warm-up fades. Maultaschen were soft. Bean Beats were dark and burnt. But the beats of #ULMageddon will be brutal! #applyIfYouCan

English
dhn retweetledi

Yes, we're beating a dead horse. But that horse still runs in corporate networks - and quietly gives attackers the keys to the kingdom. We're publishing what’s long been exploitable. Time to talk about it. #DSM #Ivanti code-white.com/blog/ivanti-de…
English
dhn retweetledi

My blog post on some vulns in GFI MailEssentials
frycos.github.io/vulns4free/202…
English
dhn retweetledi

Ever wondered how Kurts Maultaschenfabrikle got hacked in 2023? The full story, all technical details, out now ;-) apply-if-you-can.com/walkthrough/20…
English

@ATeamJKR @codewhitesec Sometimes it seems like people treat production as their own personal development environment — skipping local tests and just going with a "yolo" or "let’s see what happens" mindset😅😝
English
dhn retweetledi

BeanBeat has been aquired by Kurts Maultaschenfabrikle! You don't know what that means? Head over to apply-if-you-can.com to find out in challenges that, without exception, stem from real-world vulns #uncompromisingRealism #finestHacking
English
dhn retweetledi

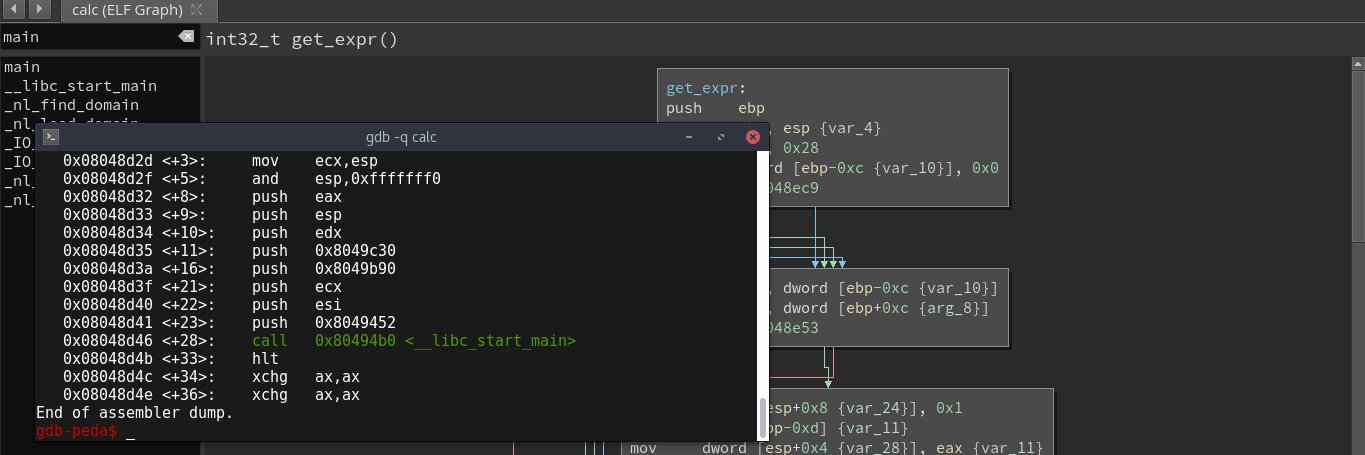
Finally, the second part of the blog post where we go from Windows Paged Pool Overflow to SYSTEM shell starting from Low Integrity 3sjay.github.io/2024/09/20/Win… have a great weekend everyone ;)
esjay@esj4y
First part which covers the bug and finishes off with code allowing us for a controlled overflow in the Paged Pool is up: 3sjay.github.io/2024/09/08/Win…
English
dhn retweetledi

First part which covers the bug and finishes off with code allowing us for a controlled overflow in the Paged Pool is up:
3sjay.github.io/2024/09/08/Win…
esjay@esj4y
Blogpost coming soon!
English
dhn retweetledi

We've received insider information from a reliable source that Kurts Maultaschenfabrikle will be expanding and securing their IT in the coming weeks. So either act fast and get ahead on apply-if-you-can.com or wait for the new challenges. Or better yet, do both 🤓
English

@trickster012 If you'd like to host your own instance, I can recommend Headscale - headscale.net
English
dhn retweetledi

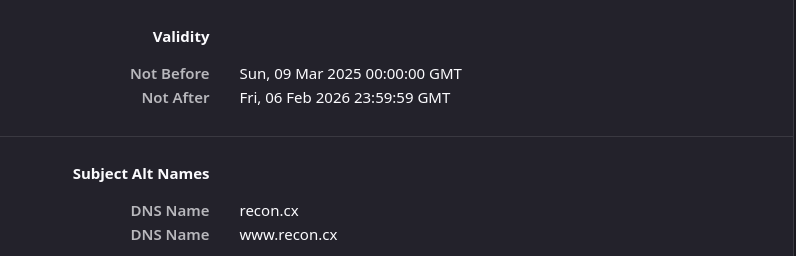
Sometimes, the Certsrv endpoint of a CA is configured to run on TCP port 443. Worth checking for ESC8 even though the most common reason for binding the endpoint to 443 is EPA. Certipy's check was only on TCP port 80; the PR will include both ports. github.com/ly4k/Certipy/p…
English