Roman Melnikov
161 posts

Roman Melnikov
@dimdumon
ex DagLabs / Kaspa L1 C-Arch & Vp RnD, ex Panther Protocol ZKP-Arch, Privacy, ZKPs, L1s, Blockchains



For years, the conventional wisdom was to put 100% of your energy into building, and to ignore politics. The problem was that those who put 100% of their energy into fighting, particularly politicians, would then take everything you’d built. Like the video game Civilization. If you put everything into science and commerce, while the next door tribe puts it all into swordsmen and slogans, they’ll waltz over and walk over you. The temptation is then to respond in kind, by putting 100% of your resources into fighting. This does work to ward off the initial assault. But without building you become just like your violent and unproductive neighbors. Everyone becomes a violent, dumb tribesman. And technological progress grinds to a halt. This is the downward spiral that characterizes the darkest ages of history. Indeed, perhaps some day, long in the past, that violent neighboring tribe that’s trying to steal from you once fell into a similar downward spiral thanks to *their* enemies. And lost their productive capacity, and had only tribal raiding to fall back on, resulting in their current state of contagious degradation. Think Planet of the Apes. There is an answer, though. It’s 70% build, 20% write, and 10% fight. Put most energy into building, some energy into writing, and one tenth towards fighting. Think of the 10% like your defense budget. Your technological progress provides the capital and growth to fund defense. Indeed, you may end up with >10X the resources of the vicious neighboring tribes. Because they focus solely on demonizing others rather than building up themselves. And if so, 10% of your resources will match 100% of theirs. Then, even by devoting 100% of their energy to fighting, they won’t be able to steal. Your defense is too strong. So they’ll simply need to build their own stuff. As will other tribes. Now everyone gets wealthier, and has less reason to fight. And this is the upward spiral.





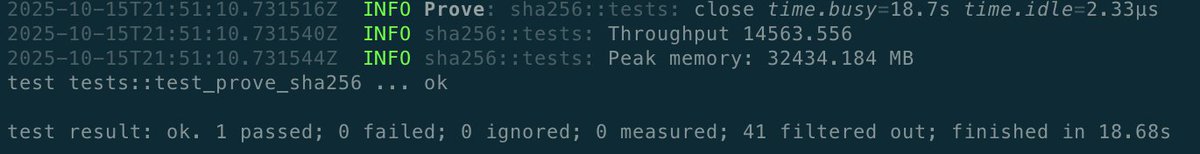
Currently reaching ~8khz proving sha256 locally on my m2 using @StarkWareLtd stwo + an optimized air based on @PapiniShahar work It’s not a lot but it’s honest work Pushing for 2x by eow Only up











Second PR to Reth from Igra Labs. Critical for true sub-second finality support. BlockDAG reorgs within 1-2 second spans are routine. Correctly mapping these to a deterministic EVM sequence is non-trivial -- without them based rollup breaks under real BlockDAG conditions.