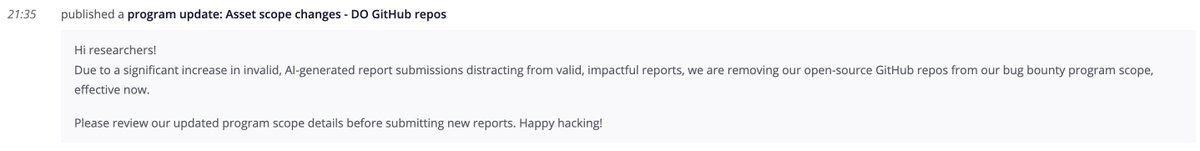
Maxwell ꓘ Dulin (Strikeout)
3K posts

Maxwell ꓘ Dulin (Strikeout)
@Dooflin5
God First ✞ | Web3 & Web2 Security Researcher (Hacker) | Gonzaga U & Centralia HS Grad | Wiffleball @ctownwiffle | Dodgeballer |

🦔 Researchers at Aikido Security found 151 malicious packages uploaded to GitHub between March 3 and March 9. The packages use Unicode characters that are invisible to humans but execute as code when run. Manual code reviews and static analysis tools see only whitespace or blank lines. The surrounding code looks legitimate, with realistic documentation tweaks, version bumps, and bug fixes. Researchers suspect the attackers are using LLMs to generate convincing packages at scale. Similar packages have been found on NPM and the VS Code marketplace. My Take Supply chain attacks on code repositories aren't new, but this technique is nasty. The malicious payload is encoded in Unicode characters that don't render in any editor, terminal, or review interface. You can stare at the code all day and see nothing. A small decoder extracts the hidden bytes at runtime and passes them to eval(). Unless you're specifically looking for invisible Unicode ranges, you won't catch it. The researchers think AI is writing these packages because 151 bespoke code changes across different projects in a week isn't something a human team could do manually. If that's right, we're watching AI-generated attacks hit AI-assisted development workflows. The vibe coders pulling packages without reading them are the target, and there are a lot of them. The best defense is still carefully inspecting dependencies before adding them, but that's exactly the step people skip when they're moving fast. I don't really know how any of this gets better. The attackers are scaling faster than the defenses. Hedgie🤗 arstechnica.com/security/2026/…
i read you guy's solana sec piece, “invocation security: Navigating Vulnerabilities in Solana CPIS,” and liked how you structured the five cpi attack classes. well, i built a rust static analyzer to automatically detect those patterns in anchor & native Solana codebase; hmm,

Big congratulations to @VulsightSec for scoring their very first paid report on Immunefi. And it's huge, huge payout. Well done! You can pledge behind them here to earn IMU when they find bugs: immunefi.com/pledge/vulsigh…

Our intern program is back, now with the option to work in-person in NYC or Zurich. We're looking for security research types who are curious, skilled, and ready to work on security challenges that matter. Apply below ↓

$312,500 worth of stored/reflected XSS vulnerabilities in Meta’s Conversions API Gateway allowed Javascript code to run on any Facebook domain and millions of third-party websites. The flaw enabled zero-click Facebook account takeover and more: ysamm.com/uncategorized/…

Voting is now live for the top ten web hacking techniques of 2025! Grab a coffee, browse the 61 quality nominations and cast your vote on the most creative and ground-breaking techniques: portswigger.net/polls/top-10-w…
Just a few days ago, the legends behind @_blockian found a max critical that earned them $250,000. Merry Christmas!