Faav
418 posts


Faav
@efaav
Hacker & Developer. Hunting bugs. Building https://t.co/qiMEJOUaRf & NameMC Extras.



Been grinding out on HackerOne and I beat @rez0__ somehow, not sure how long this'll last though... 😅 (USA Leaderboard)

Been grinding out on HackerOne and I beat @rez0__ somehow, not sure how long this'll last though... 😅 (USA Leaderboard)


Thanks everyone for playing! I talk about the solution here, as well as how I discovered this behavior while looking into the Chrome Sanitizer API: slcyber.io/research-cente…



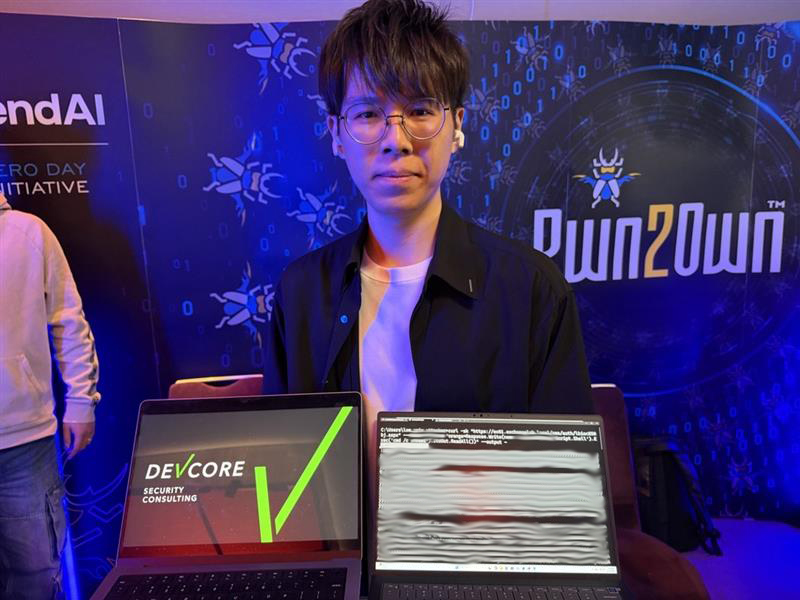

Confirmed! Orange Tsai (@orange_8361) of DEVCORE Research Team (@d3vc0r3) chained 4 logic bugs to achieve a sandbox escape on Microsoft Edge, earning $175,000 and 17.5 Master of Pwn points. Full win! #Pwn2Own #P2OBerlin



I’ll share the story behind CVE-2022-33649 in a few days before I forget…🤔 an interesting bug and methodology

🚨 Update: @mistralai npm packages are now confirmed compromised as part of the ongoing Mini Shai Hulud attack. Affected versions: @mistralai/mistralai 2.2.2, 2.2.3, 2.2.4@mistralai/mistralai-azure 1.7.1, 1.7.2, 1.7.3@mistralai/mistralai-gcp 1.7.1, 1.7.2, 1.7.3If you use the Mistral SDK in any CI pipeline, treat your environment as compromised. Rotate npm tokens, GitHub PATs, and cloud credentials immediately.