Flow.com@flow_blockchain
Flow Network Exploit Post-mortem
On December 27, 2025, an attacker exploited a vulnerability in the Flow network to counterfeit tokens, extracting approximately $3.9 million USD across bridges. No existing user balances were accessed or compromised. The attack duplicated assets but did not touch legitimate holdings, with the vast majority of counterfeit assets being contained onchain or frozen by exchange partners before they could be liquidated. Network validators have ratified a decentralized governance action authorizing the permanent destruction of 100% of counterfeit assets. The network resumed operations on December 29th and is operating as expected with full transaction history preserved.
Attack Vector
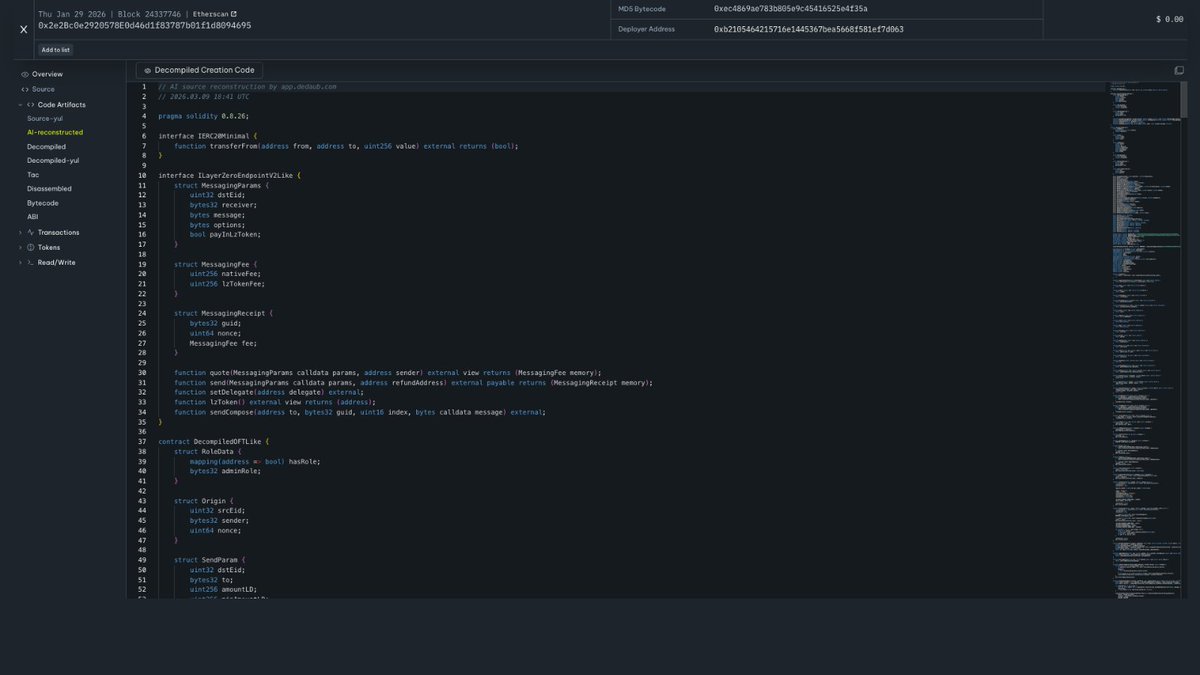
The attack demonstrated significant technical sophistication. The attacker deployed over 40 malicious smart contracts in a coordinated sequence, exploiting a three-part attack chain:
1) Attachment import validation bypass
2) Circumvention of defensive checks on built-in types
3) Exploitation of contract initializer semantics.
The root cause was a type confusion vulnerability in the Cadence runtime (v1.8.8), now patched (v1.8.9 and later). The flaw allowed the attacker to disguise a protected asset (which should be non-copyable) as a standard data structure (which can be copied), bypassing the runtime's safety checks and enabling token counterfeiting.
Remediation
Beyond bridging assets out of Flow, the attacker attempted to deposit counterfeit FLOW across several CEX, with many exchange partners freezing the deposits upon receipt due to the abnormal size and internal AML protocols. Approximately 50% of those counterfeit FLOW deposits have already been returned by cooperative exchange partners (OKX, Gate, MEXC) and destroyed, and the Foundation is actively coordinating with remaining exchanges.
The network was restored on December 29, 2025, via an Isolated Recovery Plan that preserves all legitimate transaction history. This approach was selected following ecosystem-wide consultation with exchanges, bridge operators, and infrastructure partners. The Isolated Recovery Plan was chosen specifically to avoid reconciliation risk for off-chain custodial systems and cross-chain protocols maintaining independent state.
The Foundation is cooperating with blockchain forensic partners including zeroShadow and Find Labs and relevant law-enforcement authorities to support ongoing investigations.
Full technical details of the vulnerability, exploit mechanism, forensic analysis, and remediation architecture are linked in the comment.