Eli
63 posts


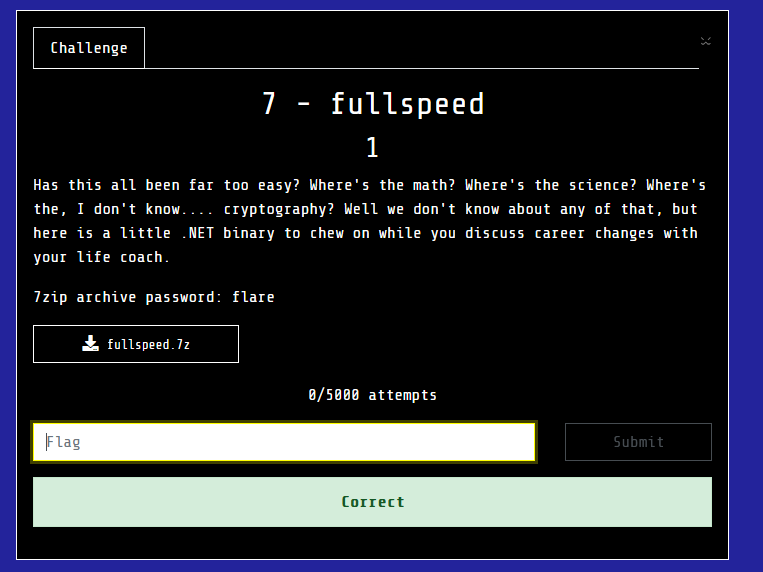
Finally done with #flareon12. The 9th task was quite a ride. I need some tips from those who did the whole thing in less than a week.

English

Completed all 9 challenges of #flareon12 🥳Kudos to all challenge authors - you did a great job! No doubt, Reverse Engineering is pure joy and misery. See you all next year
English

Finished all of this year's #flareon12 challenges 🥳
This is my 7th year in a row of completing them all, and this year I reached top-30 worldwide.
Thank you Google's FLARE team for the great challenges, and see you next year!

English

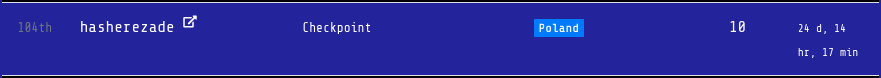
#FlareOn11 is over, so I published the repository with all my source codes: github.com/hasherezade/fl…. Write-ups coming soon!
English

@lorenzo2472 A few weeks ago I wrote an ECC CTF challenge that is based on this vulnerability, I didn't know there is also a CVE for it. Adding this to the article is a great idea, thanks for the suggestion!
English

@elikaski And this one ? neilmadden.blog/2022/04/19/psy…
English

I wrote an article about known attacks on Elliptic Curve Cryptography, check it out! github.com/elikaski/ECC_A…
English

I learned this subject in the weeks prior to #flareon11, and coincidentally one of the attacks I demonstrate also appeared in challenge 7 (which helped me and many others solve it). Due to the demand, I translated the article to English so that everyone could benefit from it.
English

🐰 I wrote one easy challenge for @IntentSummit CTF, feel free to register:
intentsummit.org
English

flaaaaaaare on!
fla-a-a-a-re on!
flareon done and ... that's it.
thank you to everyone involved. glad to have finished yet another year.
don't forget to check back for the #flareon11 writeups-short-short-version
GIF
English

Finally done with #flareon11. Not my best year, but I am happy from all the things I learned. 7 and 9 kicked my butt, and 10th was a lovely breeze after the nightmares.

English

#flareon11 finally completed! Made it to top 50 for another year 🙂 Challenges 7 and 10 were my favorites, challenge 9 was absolutely brutal. A big thank you to FLARE team, see you next year! 💙

English



@hasherezade @_CPResearch_ I was looking forward to this blog post, great work!
English

In my new blog for @_CPResearch_ I propose a new injection technique, using the Thread Name API - check it out! 💙
GIF
Check Point Research@_CPResearch_
In this blog we introduce Thread-Name Calling - A new process injection technique using Thread Name. We also discuss various scenarios in which this not widely-known API can be used for offense. research.checkpoint.com/2024/thread-na…
English

@jamieantisocial Reminds me of github.com/woodruffw/steg… which hides data in x86 instructions encoding
English

Eli retweetledi