Sabitlenmiş Tweet

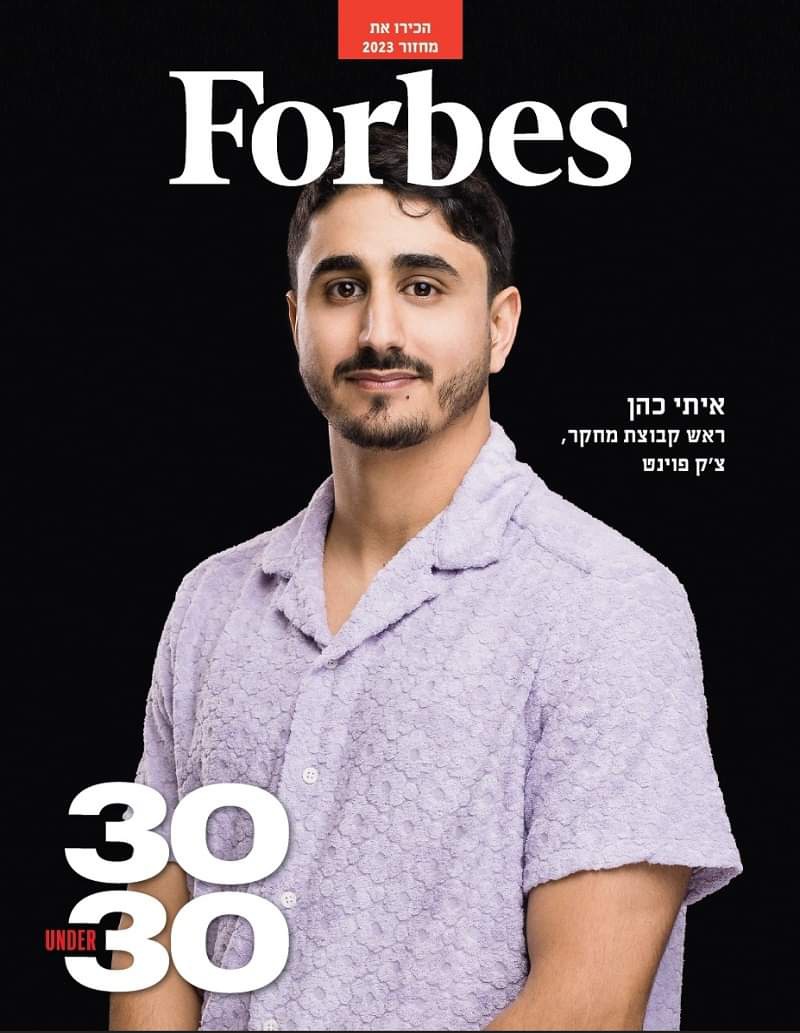
I am incredibly honored and grateful to have been selected to the Forbes 30 Under 30 list for 2023! 🎉 This recognition is deeply important to me.
I’ll continue pursuing my biggest goal — making the world a safer and more just place for all of us, humans & animals.❤️
#30under30
English