eprdude.eth 🐧🦇🔊🌊 🛡️
6.6K posts

eprdude.eth 🐧🦇🔊🌊 🛡️
@eprdude
Systems Engineer - crypto/ai 🔥 UEFI/Linux Ethereum/bitcoin
Katılım Eylül 2017
2.9K Takip Edilen897 Takipçiler

@MurrayHillGuy1 70+= at least 100 count. At an avg dick length of 6 in. That's approximately 50 ft of dick or 2 school buses length of different dicks in just a few years. End it immediately.
English

Friend is in an absolute pickle rn…
He’s been on like 7+ dates with this girl, really likes her, everything’s going great.
Then last night for whatever reason (never ask this question) he asked her body count.
70+.
Now he wants to end it immediately.
She’s 27, he’s 30.
Is this valid or is he being soft?
English
eprdude.eth 🐧🦇🔊🌊 🛡️ retweetledi
eprdude.eth 🐧🦇🔊🌊 🛡️ retweetledi

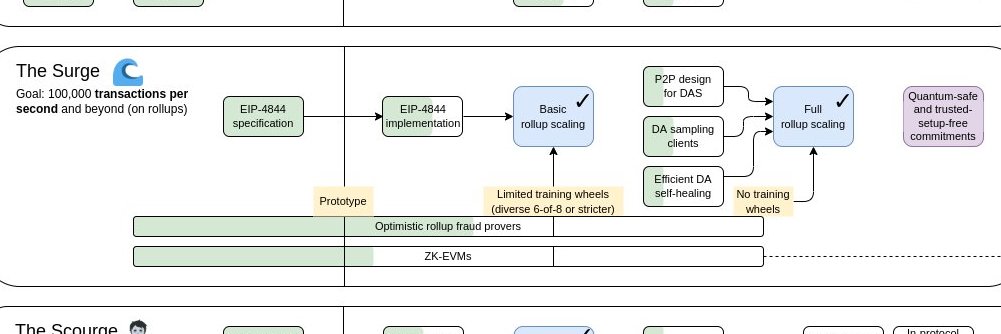
Upgrading Finality - Edition 1
Check out the plan for bringing fast finality to Ethereum.
Hosted on the the brand new and shiny EF Protocol Consensus website 😁 Lots of good stuff there!
consensus.ethereum.foundation/blog/upgrading…
English
eprdude.eth 🐧🦇🔊🌊 🛡️ retweetledi
eprdude.eth 🐧🦇🔊🌊 🛡️ retweetledi
eprdude.eth 🐧🦇🔊🌊 🛡️ retweetledi

Apple and Google are gradually expanding their use of hardware-based attestation. They're convincing a growing number of services to adopt it. Google's Play Integrity API and Apple's App Attest API are very similar. Apple brought it to the web via Privacy Pass, which Google intends on doing too.
Google's Play Integrity API requires hardware attestation for the strong integrity level and is gradually phasing in requiring it for the more commonly used device integrity level. Apple already has it as a requirement. Over the long term, this will increasingly lock out hardware and OS competition.
The purpose of these systems is disallowing people from using hardware and software not approved by Apple or Google. This is wrongly presented as being a security feature. Banks and government services are the main ones adopting it but Apple and Google are encouraging every service to use it.
Apple's Privacy Pass brought hardware attestation to the web to help with passing captchas on their own hardware. Many people saw that as harmless since few sites would be willing to lock out non-Apple-hardware users. Apple and Google are both likely to bring broader hardware attestation to the web.
Google's reCAPTCHA is planning an approach where they use Privacy Pass on Apple hardware, their own approach on Google Mobile Services Android devices and a QR code scanning system to require an iOS or Google certified Android device for Windows and other systems:
support.google.com/recaptcha/answ…
Banking and government services increasingly require using a mobile app where they can use attestation to force using an Apple or Google approved device and OS. Apple's privacy pass, Google's 'cancelled' Web Environment Integrity and now reCAPTCHA Mobile Verification are bringing this to the web.
Current media coverage for reCAPTCHA Mobile Verification misunderstands it and the impact of it. They're bringing a hardware attestation requirement to Windows, desktop Linux, OpenBSD, etc. by requiring a QR scan from a certified smartphone to pass reCAPTCHA in some cases. They could expand it more.
Control over reCAPTCHA puts Google in a position where they can require having either iOS or a certified Android device to use an enormous amount of the web. Google defines certification requirements for Android which includes forcing bundling Google Chrome, etc. It's enormously anti-competitive.
Google's Play Integrity API bans using GrapheneOS despite it being far more secure than anything they permit. It also bans using any other alternative. This isn't somehow specific to an AOSP-based OS. You can't avoid this by using a mobile OS based on FreeBSD instead. You'll just be more locked out.
Google's Play Integrity API permits devices with no security patches for 10 years. The device integrity level can be bypassed via spoofing but they can detect it quite well and block it once it starts being done at scale. The strong integrity level requires leaked keys from TEEs/SEs to bypass it.
It doesn't provide a useful security feature, but it does lock out competition very well. Services requiring Apple App Attest or Google Play Integrity are primarily helping to lock in Apple and Google having a duopoly for mobile devices. Play Integrity is more relevant due to AOSP being open source.
Governments are increasingly mandating using Apple's App Attest and Google's Play Integrity for not only their own services but also commercial services. The EU is leading the charge of making these requirements for digital payments, ID, age verification, etc. Many EU government apps require them.
Instead of governments stopping Apple and Google from engaging in egregiously anti-competitive behavior, they're directly participating in locking out competition via their own services. Requiring people to have an Apple device or Google-certified Android device is anti-competition, not security.
reCAPTCHA Mobile Verification will currently work with sandboxed Google Play on GrapheneOS but it clearly exists to provide a way for them to start using hardware attestation on systems without it. People without an iOS or Android device will be locked out when this is required even without that.
This isn't about security or any missing functionality. GrapheneOS can be verified via hardware attestation. Google bans using GrapheneOS for Play Integrity because we don't license Google Mobile Services and conform to anti-competitive rules already found to be illegal in South Korea and elsewhere.
Services shouldn't ban people from using arbitrary hardware and operating systems in the first place. Google's security excuse is clearly bogus when they permit devices with no patches for 10 years but not a much more secure OS. It's for enforcing their monopolies via GMS licensing, that's all.
English

@TrustlessState It's probably going to flirt with TAO mcap on this narrative.
English
eprdude.eth 🐧🦇🔊🌊 🛡️ retweetledi

ethereum got flooded by fucking mercenaries pretending to be revolutionaries. everyone talks about decentralisation until there's money on the table, then suddenly compliance, surveillance, business opportunities, and extraction become pragmatic. most of this ecosystem does not give a shit about freedom. they care about pumps, fees, and turning users into fucking exit liquidity. cypherpunk was never about making founders rich. it was about making tyranny obsolete. the grifters will cash out. the cowards will comply. cypherpunks will outlast all of them. principles compound harder than capital. you don't have to believe me. you won't. because you'll be gone while i'm still here.
English
eprdude.eth 🐧🦇🔊🌊 🛡️ retweetledi

firewalls can't stop this.
A developer just open sourced a tunnel that smuggles your entire internet through port 53 the port every router on earth is forced to leave open.
It's called MasterDnsVPN. It hides your traffic inside DNS queries, the one type of packet no network can block without breaking itself.
Every firewall on earth has to allow DNS. Schools, airports, hotels, hotel WiFi, entire countries running ISP-level censorship all of them keep port 53 open or nothing on the network resolves. This repo turns that loophole into a full encrypted tunnel.
Here's what makes it different from every other DNS tunnel that came before:
→ Custom ARQ layer gives you TCP-level reliability over UDP DNS, so nothing drops even on garbage networks
→ Sends every packet through up to 12 different resolver paths at the same time, if 11 fail the packet still arrives
→ Auto probes the maximum DNS payload your path can handle, then locks in the fastest MTU possible
→ AES-256-GCM, ChaCha20, AES-128, AES-192 all built in, pick your encryption
→ SOCKS5 proxy on 127.0.0.1:1080 point any browser or app at it and you're through
Killed: $12/mo Mullvad, $10/mo NordVPN, $15/mo Astrill, every commercial DNS tunnel charging monthly fees for the exact same idea.
Pre-built binaries for Windows, Linux AMD64, Linux ARM64, macOS ARM64. No Python install needed. Configure two DNS records, drop in the encryption key, run the executable.
Works in environments where every other VPN protocol is dead on arrival.
MIT License. 100% Opensource.

English

A month before our wedding, my fiancée asked me to swing by her sister’s condo and pick up her favorite old sweatshirt. She said she’d left it there after a family barbecue and really wanted it back before the honeymoon.
I knocked on the door and her sister answered wearing workout leggings and a fitted top. I'd always thought my fiancée's sister was hot but she was exceptionally hot today. She’d clearly just come in from a jog and still had that fresh-from-the-shower look. She handed me the sweatshirt and gave me a quick hug that lasted just a second too long.
As I turned to leave, she said, “What’s the rush?”
I told her I didn’t want to interrupt her afternoon. That’s when she lowered her voice and said, “Before you marry my sister, I need you to know I think you're super hot, and I've always wanted to get it on with you. If you want to have a last little bit of fun before you walk down that aisle, it will be our little secret.”
I didn’t say a word. I spun around and headed straight for my car like it was the last lifeboat on the Titanic.
When I got outside, my fiancée and her parents were standing by the driveway, all smiles. Her dad clapped me on the back and said, “Son, that was quite a test. We’re proud to welcome you to the family.”
Her sister stepped out behind me laughing and said, “Well, I’ll be. I have to hand it to you there; I didn't think you'd turn me down." I was dumbfounded. We all hugged and went out for dinner.
And the moral of the story?
Always keep your condoms in your glove compartment of your car.
English
eprdude.eth 🐧🦇🔊🌊 🛡️ retweetledi

Inference that doesn't spy on you
Sabrina@sabrinaesaquino
Venice API token usage over time. (G=billion)
English
eprdude.eth 🐧🦇🔊🌊 🛡️ retweetledi

Past days has been extremely hardcore for our team and DeFi in general. DeFi went trough a substantial stress test and the consequences were felt. It definitely was the hardest couple of weeks that I experienced in my life and during the past decade building in the space. I am still writing this with couple of hours of sleep per day so bear with me.
For me personally, the rsETH bridge incident was unfortunate as our team and community has put so much effort into securing the protocol and seeing the exploit happening outside of the protocol smart contracts, and affecting the markets is hard to watch even when the markets had (and still have) full backing like Mainnet Core. That being said, Aave has seen multiple market/credit cycles and always has been able to prove its resiliency. I have more confidence in DeFi today than ever, not because of the industry is stepping up and improving security practices, but because there is a true community behind DeFi that is willing to help and do whatever it takes to ensure our space has future.
I want to say that during all this madness there were lot of people that were extremely supportive and proactive to mitigate any issues and contagion. At the first glance, from Aave's perspective we were positive that we would find a resolution and we had overall balance sheet, protocol revenue and external/public support to over come the issue from Aave's perspective but what we understood is that the issue was beyond Aave. It was about restoring the whole state of DeFi, avoid contagion and ensuring that the whole ecosystem overcome this incident not solely Aave.
DeFi United started as an initiative from DeFi protocols that were affected but eventually became an industry wide movement to save DeFi and bring protocols together. I am grateful for all the contributions and support that everyone has been providing and can say that this wouldn't be possible without it. I'd hope that DeFi United becomes a permanent movement in some shape or form with the right form factor. DeFi United was executed at insane speed and other constraints but there could be a model that could continuously support the industry from the unexpected.
I'd say during the past week lot of people stood up and I really don't have the space to mention everyone (you know who you are) but specifically I want to say that @MikeSilagadze deserves more respect from the space than anyone else atm, he went above and beyond and was willing to sacrifice a lot to solve what actually wasn't something cause by his efforts. Full respect.
@LidoFinance team also deserve special credit, this team truly cares about DeFi and was extremely helpful along the way. They deserve full credit.
@gdog97_ deserves credit as well, who helped to brainstorm various solutions and also stepping in with Ethena and helping on coordination.
@arbitrum community for doing the right thing and rescuing the funds from the bridge contract that was a difficult but the right call.
@Mantle_Official @Bybit_Official team for stepping up as well and showing strong support. The team has been supportive and truly cares about making the space safe.
Last but not least lot of credit goes to @ethereumJoseph who really stepped in to help DeFi and the ecosystem. Joe cares about Ethereum, he cares about DeFi and understand the importance of DeFi for the future of Ethereum.
We have truly good people within our community.
These folks are true guardians of our space (among others on my long list) that really want DeFi to win.
I feel very optimistic now about our space, it is true that events like these can be a setback but in reality it builds resiliency, which our space stands for, and over time that is hard to beat by legacy systems.
The past week we had to operate in multiple different constraints from time, information, resources, governance and other. We had to move as fast as we could as time was against us. It was a large coordination effort that we haven't experienced so far. I'd like to give most of this credit to our team and community especially @Token_Logic and @LlamaRisk who went also above and beyond to find resolutions and coordinate.
There has been some banter about right type of market structure for onchain lending between shared or isolated pools but the reality is that when capital moves, it moves at scale and market structures are less of a mitigating factor. These kinds of times require to find solutions fast and reestablish the trust in the markets and the technology, that's whats important.
All this being said there are some great learnings from this indecent like from any incident and we as any other team involved will share a post mortem and steps to improve anti-fragility. I might be now less bullish on onchain lending as infrastructure and more leaning towards a model where the market structures need to be backed by strong balance sheets and risk transfers, however this is another discussion for the future as issues can stem outside of the protocol's control.
Now as the markets on Ethereum mainnet Core are restoring, our team continues to execute the technical plan to restore rest all the markets.
Thank you for everyone who has been supportive and we will keep you up to date as we progress.
DeFi United.
English
eprdude.eth 🐧🦇🔊🌊 🛡️ retweetledi

Nethermind Client 1.37.1 is live.
Worldstate backend refactor lands with pluggable backends. Flat DB ships opt-in. RocksDB and column DB snapshots. EIP-7928 block-level access lists. Initial zkEVM groundwork and witness generation. EVM hot paths, pruning, and networking hardening throughout.
Breaking: Engine API versioning reworked. eth/66 and eth/67 dropped. eth/69 default, eth/70 live.

English

@pcaversaccio @wslyvh This. We should have all converged on a single OS decades ago. Tons of Mal investment, massive tech debt and complexity. Baffling really.
English

rant time: people are so fucking obsessed with building more tools, more products, more services, more "security" layers. are you guys all fucking insane?? every single thing you add is more complexity. and complexity is exactly what makes systems _dangerous_. you don't get safer by stacking abstractions on top of abstractions. you just increase the attack surface and pray the whole dependency chain doesn't collapse (hint: it will collapse!!). now you depend on 10, 50, 100 moving parts. all needing updates, all with their own bugs, all potential supply chain failures and we call that "security" like fucking retards.
dude, it's the fucking opposite. we're not building safer systems. we're building systems so complex nobody actually understands them anymore. and almost nobody is asking the obvious question: **what can we remove?** everyone wants to add. nobody wants to reduce. that's how you end up in a nightmare system (hint: we're already in that nightmare). not because of one big failure. but because of thousands of tiny dependencies you never should have had in the first place.
English
eprdude.eth 🐧🦇🔊🌊 🛡️ retweetledi

basically all of my code is _open-source_ and _free_ to use; in most cases it's licensed under AGPL-3.0 so everything stays open & accessible forever. a lot of my code is used to protect millions or even billions in funds (e.g. my `safe-tx-hashes-util`), yet many projects still don't donate because i don't go through some retarded kyc process (guys, fuck u!), even though i actively help secure their systems & money (yeah fml). the Ethereum Security QF round will hopefully change that tbh.
so i've submitted 2 applications:
- snekmate: i started snekmate in 2022 as its sole author and have poured thousands of hours into it over the past 3.5 years (1,200+ commits so far). its math functions are now even formally verified, it's used by Curve to help secure millions in funds, it's included in external integration tests in Foundry & Halmos (and has found various bugs already), and even used in the Vyper compiler itself (various bugs detected in the new venom IR because of this integration). it's essentially a one-person project that powers & ships essential Vyper modules to teams across the ecosystem.
- safe-tx-hashes-util: before the EF deploys capital into some defi protocols, the multisig txs are verified using my tool. before we deployed 69,420 ETH into staking at TheDAO, those multisig txs were verified with it. major protocols rely on it as a local-first verification layer for one of the most critical parts of any multisig: transaction correctness. i also recently shipped an easy-to-use Qubes template. so far i've received around ~$25k in donations, while this script alone has helped secure billions in funds.
pls donate:
- snekmate: qf.giveth.io/project/snekma…
- safe-tx-hashes-util: qf.giveth.io/project/safe-m…


Giveth@Giveth
If you’re tired of watching exploits dominate the timeline, this is your moment to act. The Ethereum Security QF Round is LIVE! Support the people and projects securing Ethereum and its L2s. 500 ETH (~$1M+) in matching from @thedaofund. Explore & donate: qf.giveth.io/qf/ethereum-se…
English