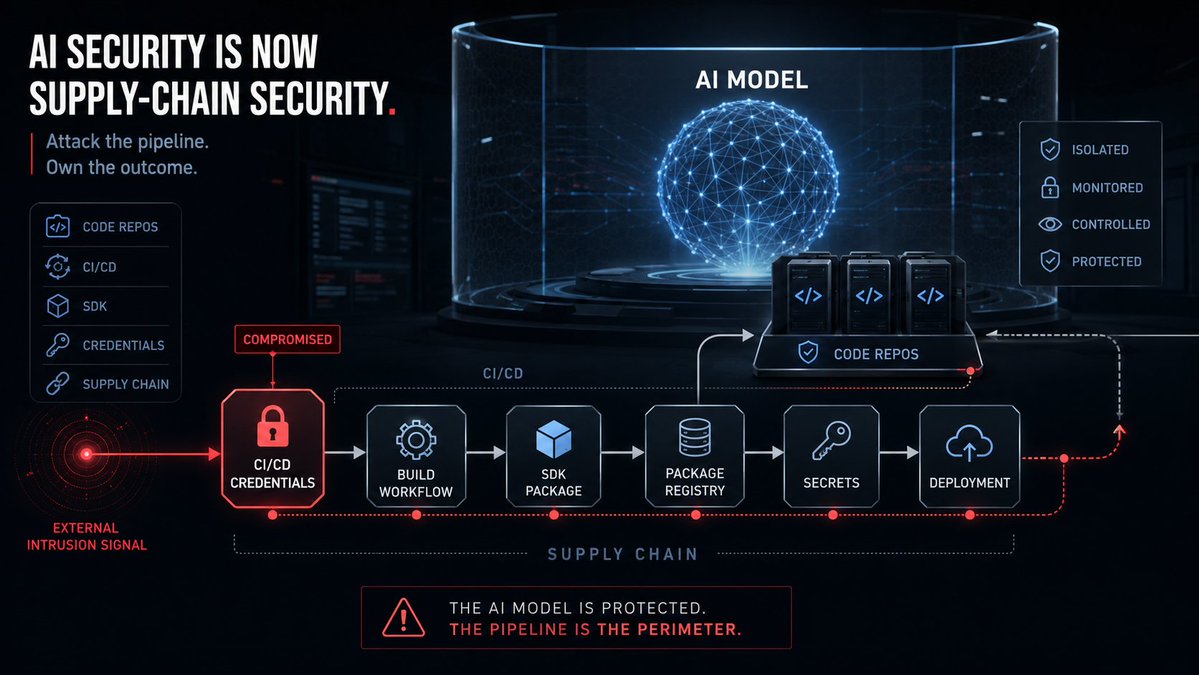
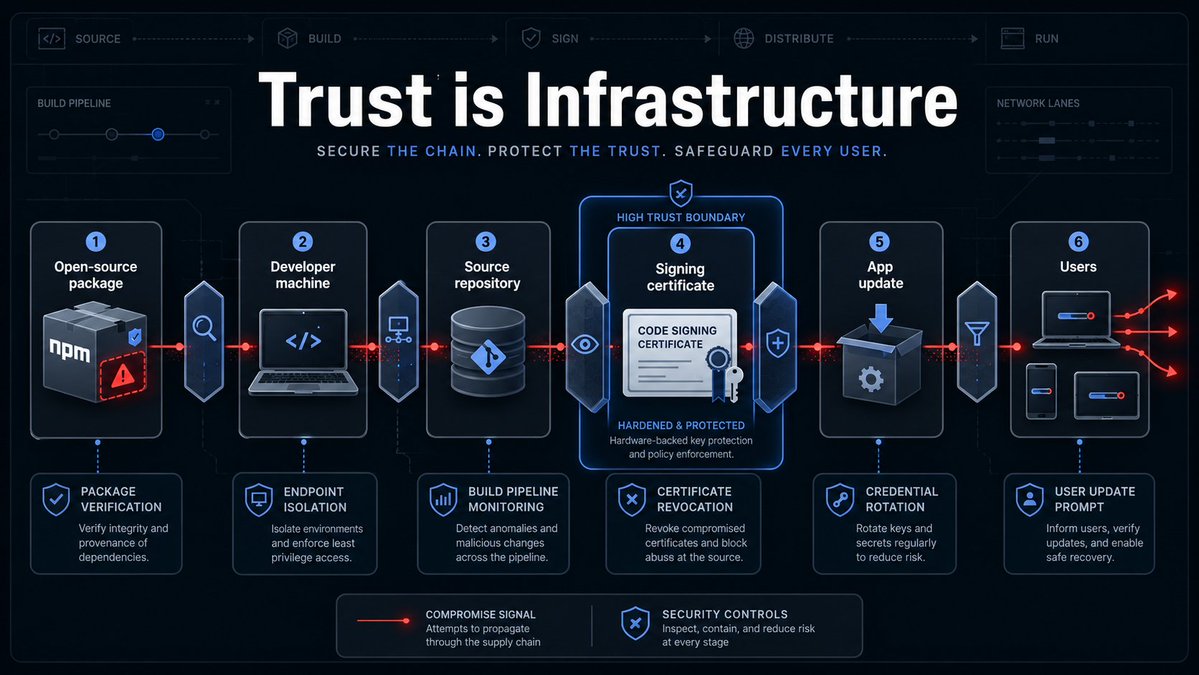
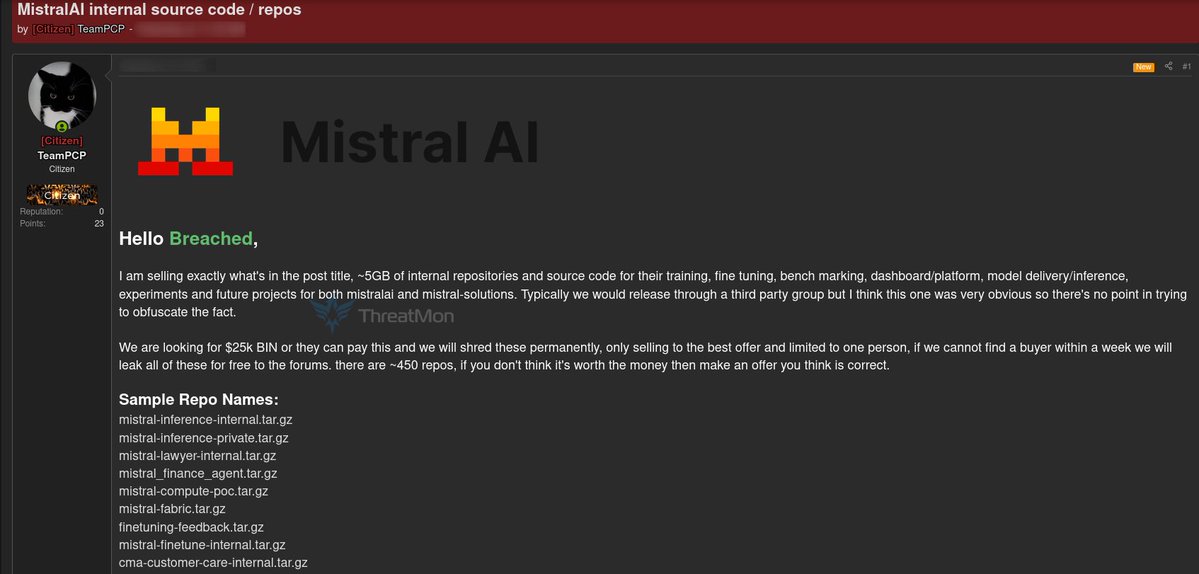
The next big AI breach may not start with prompt injection. 🤖 It may start with a stolen CI/CD credential. Hackers are now advertising alleged Mistral AI code repositories for sale, claiming access to nearly 450 repos and about 5GB of internal code, according to BleepingComputer. The asking price: $25,000. That’s the scary part. AI labs are billion-dollar targets, but attackers may only need one weak link in the software supply chain: SDKs, package registries, build workflows, developer machines, or leaked secrets. Mistral says the issue was tied to the broader TanStack / “Mini Shai-Hulud” supply-chain attack, and that hosted services, managed user data, and research environments were not compromised. Still, the lesson is clear: AI security is no longer just about models, prompts, and evals. The real attack surface is the software factory behind the model.